Hash will host the Hack Chat on Wednesday, April 14 at noon Pacific.
Time zones got you down? Try our handy time zone converter.
That electrical meter on the side of your house might not look like it, but it's pretty packed with technology. What was once a simple electromechanical device that a human would have to read in person is now a node on a far-flung network. Not only does your meter tote up the amount of electricity you use, but it also talks to other meters in the neighborhood, sending data skipping across town to routers that you might never have noticed as it makes its way back to the utility. And the smartest of smart meters not only know how much electricity you're using, but they can also tease information about which appliances are being used simply by monitoring patterns of usage.
While all this sounds great for utility companies, what does it mean for the customers? What are the implications of having a network of smart meters all talking to each other wirelessly? Are these devices vulnerable to attack? Have they been engineered to be as difficult to exploit as something should be when it's designed to be in service for 15 years or more?
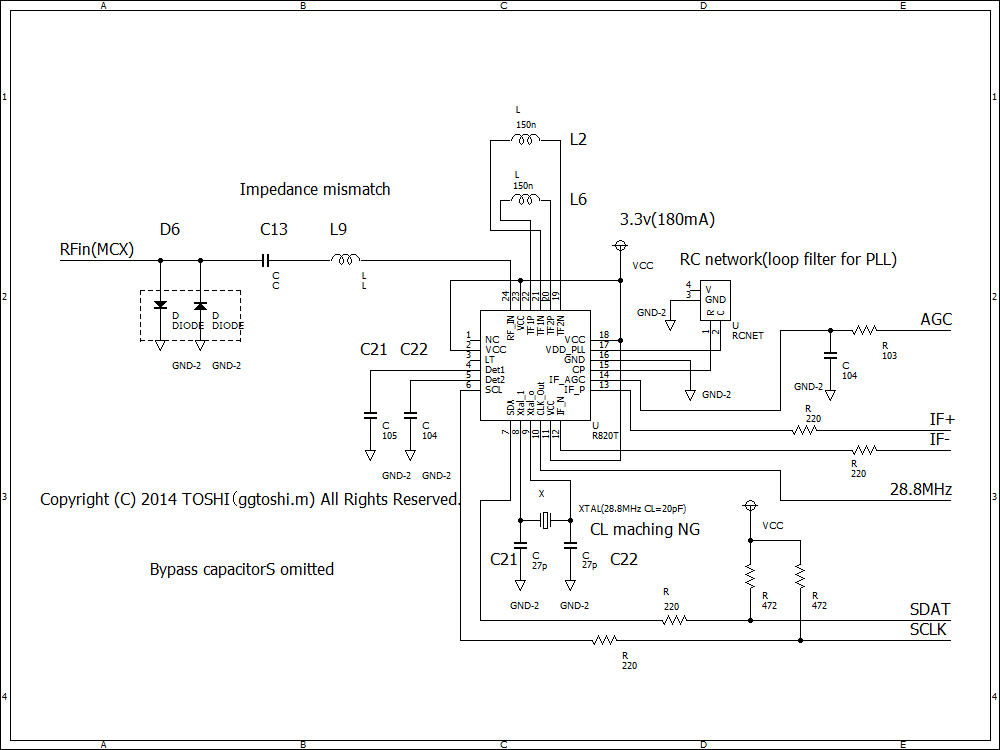
These questions and more burn within Hash, a hardware hacker and security researcher who runs the RECESSIM reverse-engineering wiki. He's been inside a smart meter or two and has shared a lot of what he has learned on the wiki and with some in-depth Smart Meter Hacking videos. He'll stop by the Hack Chat to discuss what he's learned about the internals of smart meters, how they work, and where they may be vulnerable to attack.





 Beat me to it...
Beat me to it...