Join the Hack Chat by clicking on the JOIN HACK CHAT button. Then, request to join #Hack Chat.
Don't request to join from this page, click the JOIN HACK CHAT button.
____________________________________________________________
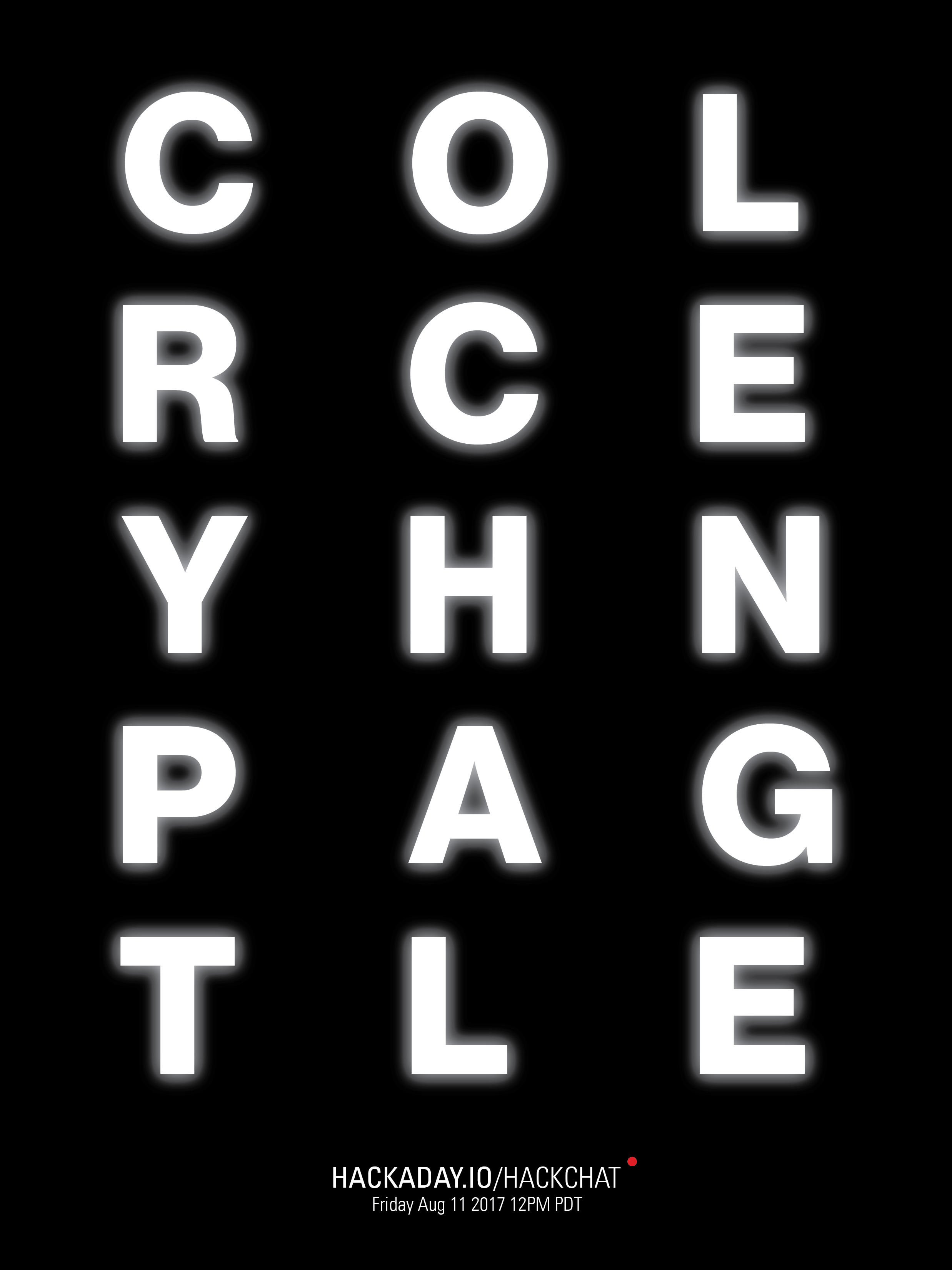
@Karl Koscher and @John Adams will be hosting the Hack Chat this week.
Hack Chats are (almost) always on Fridays at noon PDT.
Time Zones got you down? Here's a handy time converter!
In this chat, we'll be talking about some of the Crypto challenges that were created for Defcon. DEF CON is a hacker convention in Las Vegas, Nevada, USA. The convention has multiple speaker tracks about computer and hacking-related subjects, social events, and contests.
One of the crypto challenge writeups from 2016 starts like "The challenge this year started a week before DEFCON 24 began, when we noticed that some HTML comments on lostboy.net had been changed. It didn’t take long for us to discover that the site was appending the text “Watching are you?” to the bottom of the page, every minute on the minute."
@Karl Koscher is a research scientist at the University of Washington where he specializes in embedded systems security. In his spare time, he likes to dabble in RF and electronics. He is one of the co-organizers of the Crypto and Privacy Village.
@John Adams is a security researcher and engineer. He is best known for his early work scaling and securing Twitter. When not hacking on electronics and security related issues, he is usually producing and writing music. He is one half of the creators of the IDES OF DEFCON badge. Follow him on Twitter @netik.
TL;DR :: we'll be discussing:
- How Crypto Challenges work - who wins, who loses?
- Crypto firmware
- Techniques used to solve Crypto Challenges
- How Crypto Challenges are created
Here's the sheet to guide the discussion.


Most of all I would like to hear the opinion of Karl Koscher from the University of Washington. Besides, it would help me with https://edubirdie.com/blog/informative-speech-topics when dealing with similar events. Various business nuances and details help in creating informative speech topics.