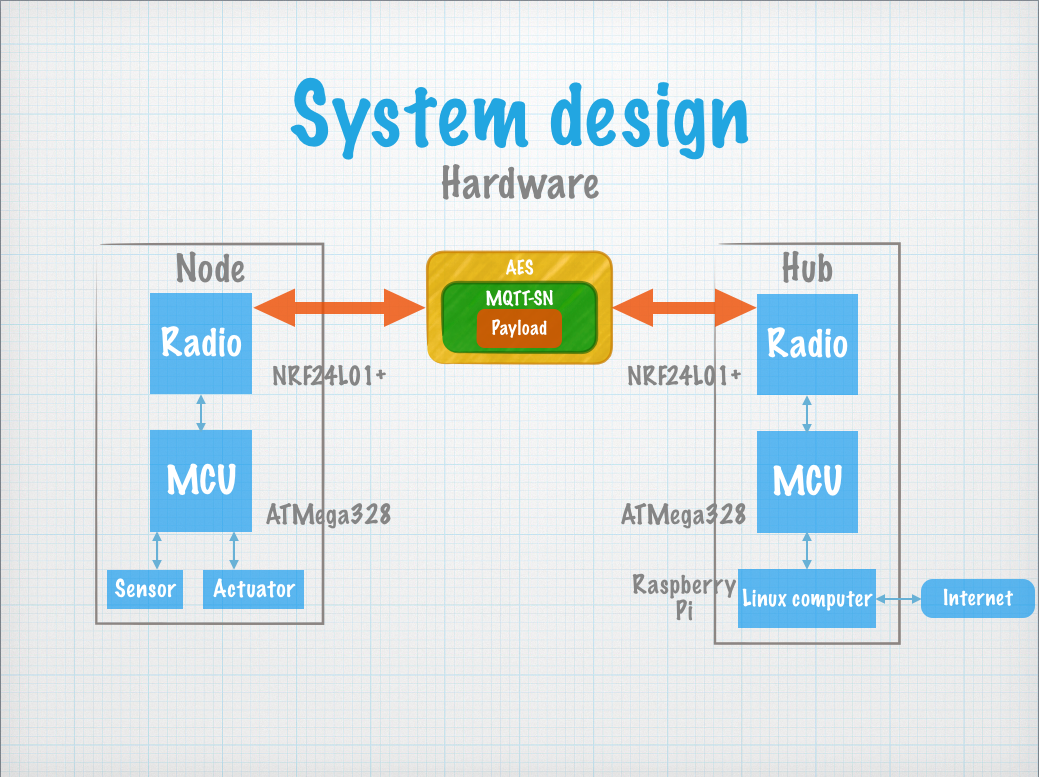
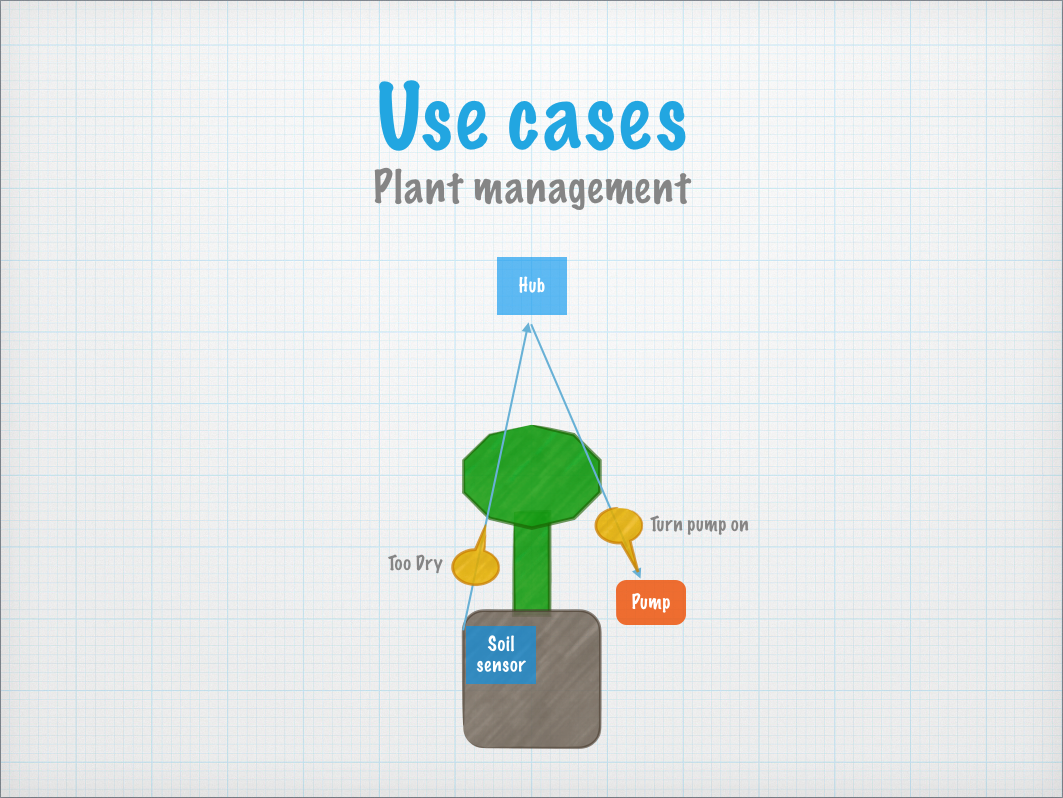
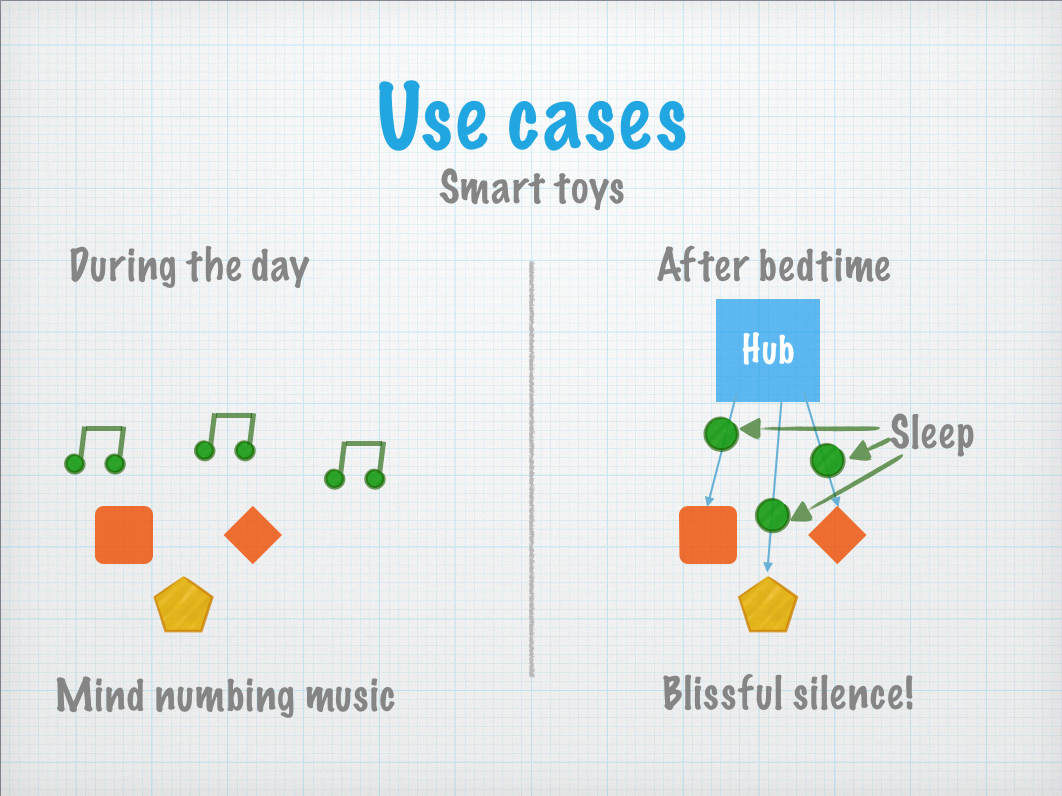
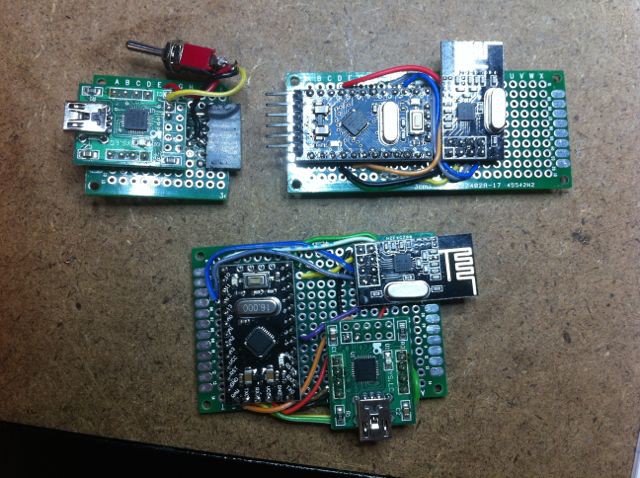
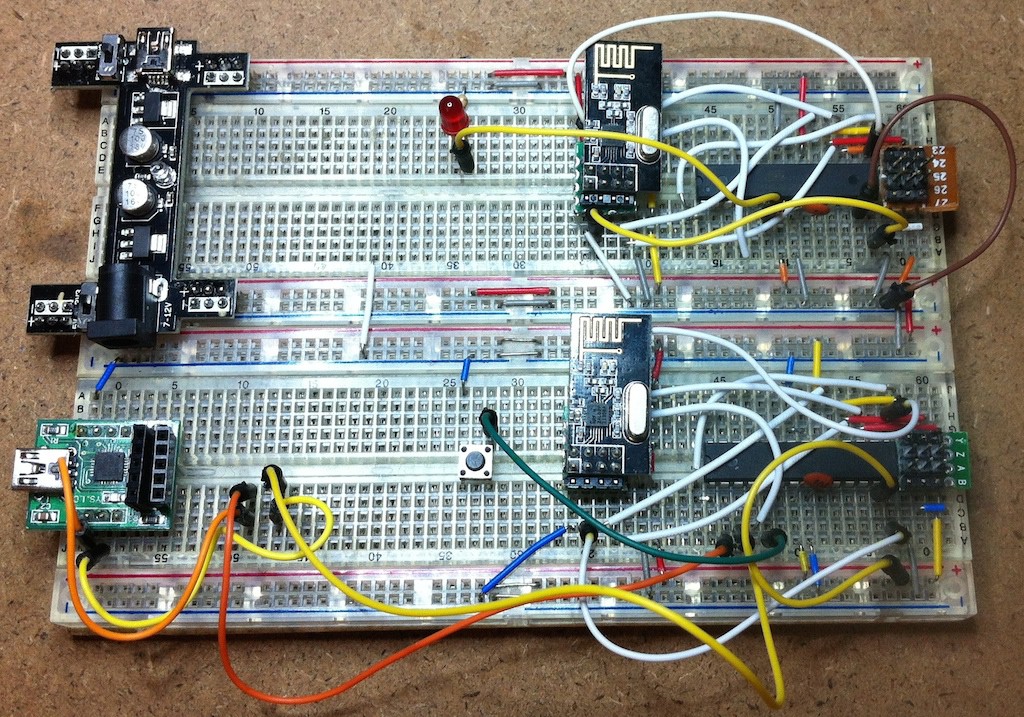
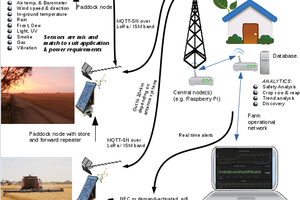
Iota combines cheap AVR dev boards and cheap nRF24L01+ radio modules to create a home network of sensors, and "actuators" which can switch things on and off through your house.
Over time you can build up a custom smart home, all wirelessly and designed to be light on power to allow long run times from 2xAA batteries.
System Design
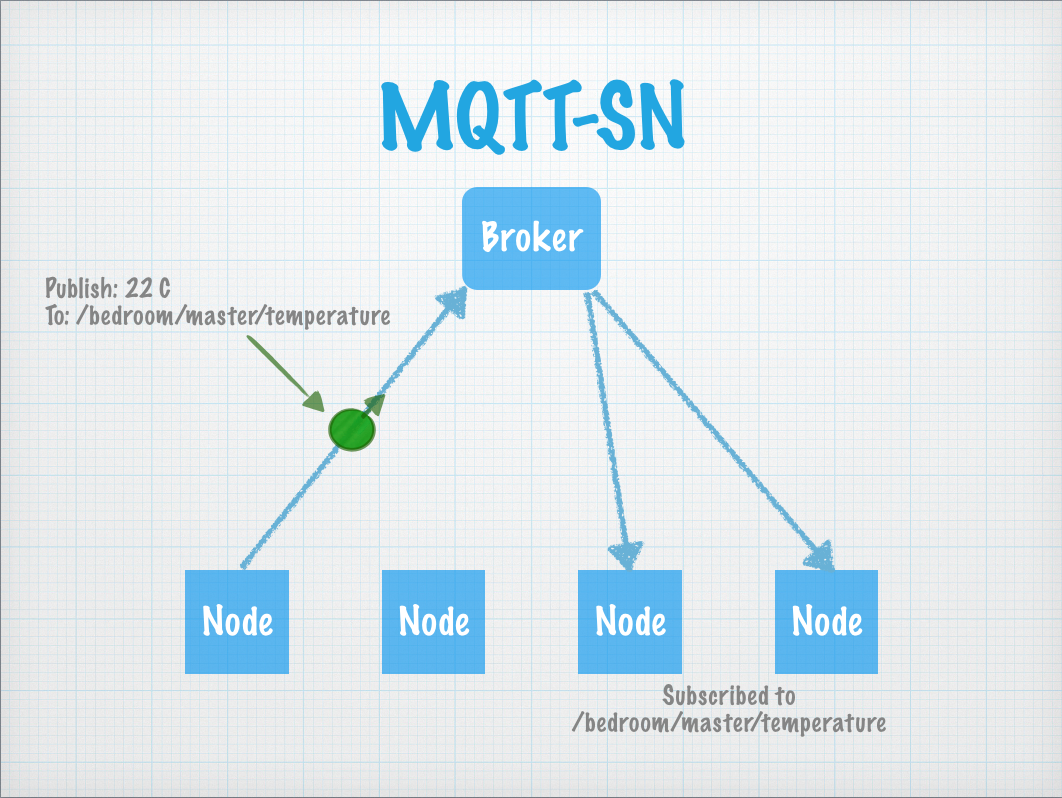
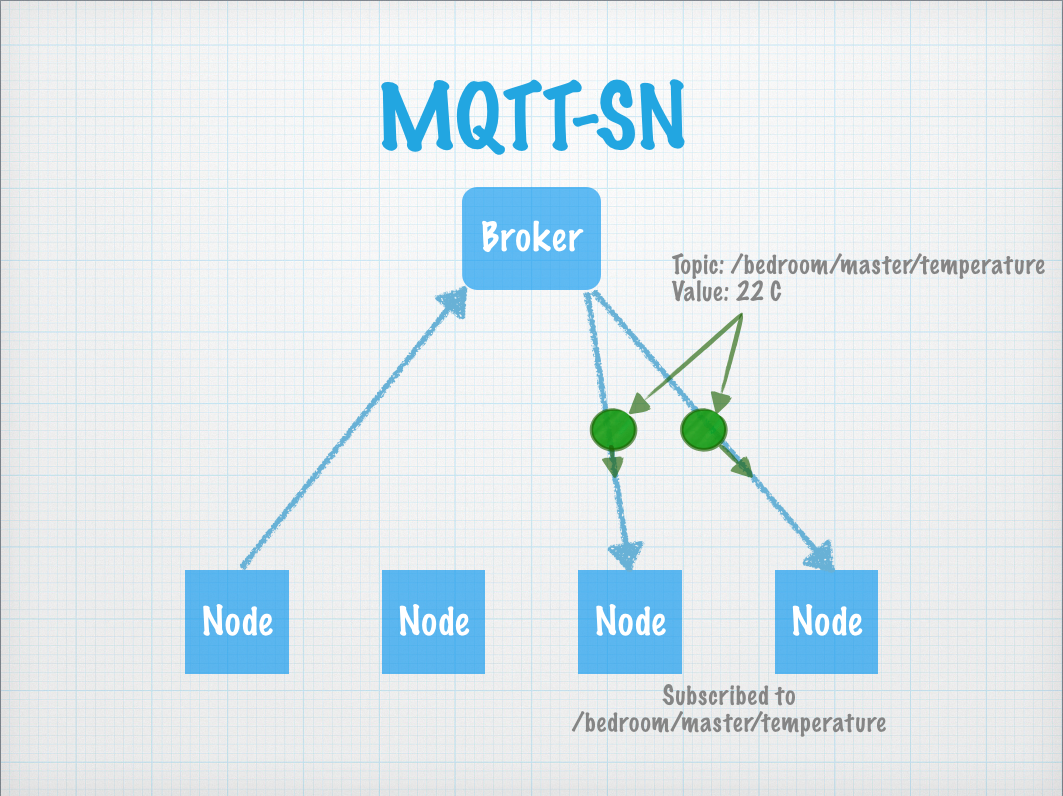
One of the primary goals of Iota is to make it simple to build a network of sensor and actuator nodes.
It is easy enough to combine a micro controller and radio to send simple messages, but you have to write special code for each case, each new message you want to send.
So as you add more nodes, more combinations, the code becomes harder to write, harder to combine.
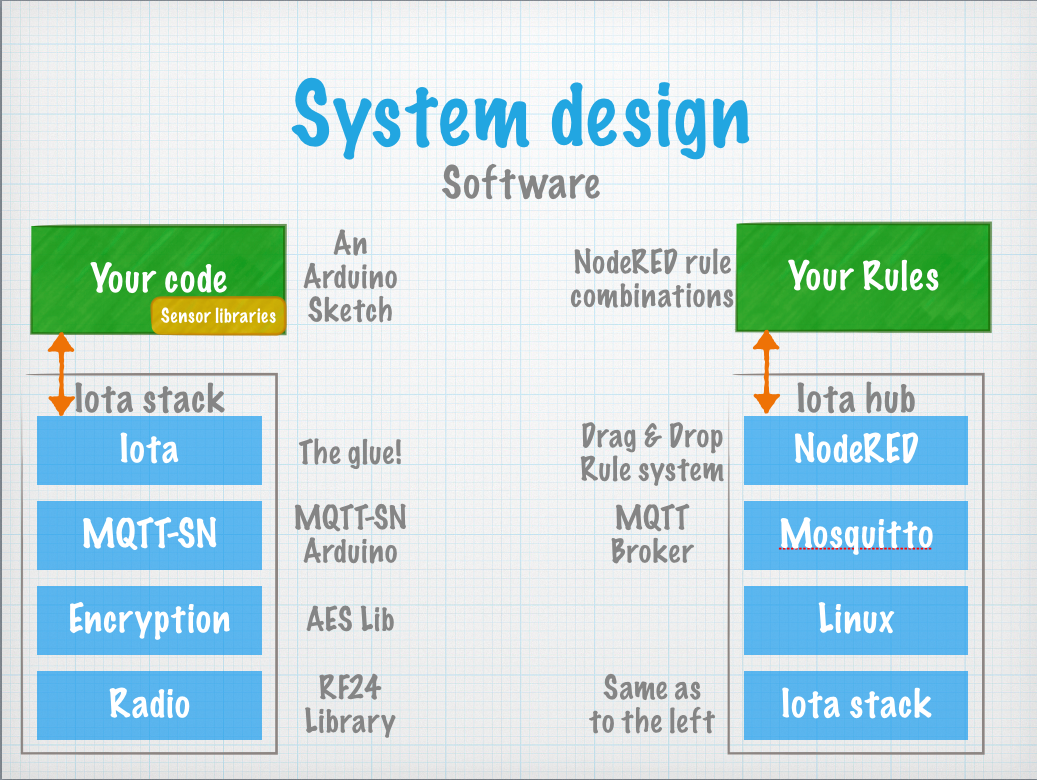
Iota solves this by providing a higher level abstraction using the MQTT-SN protocol allowing different messages to be sent without needing special code for each case.
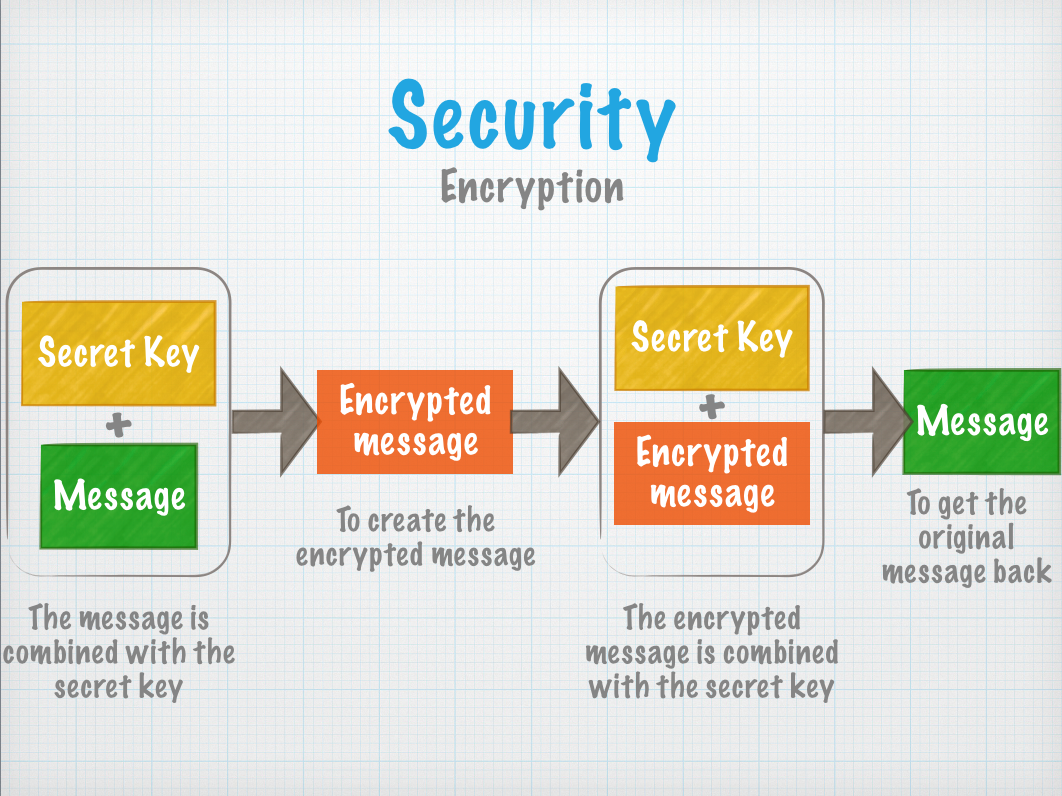
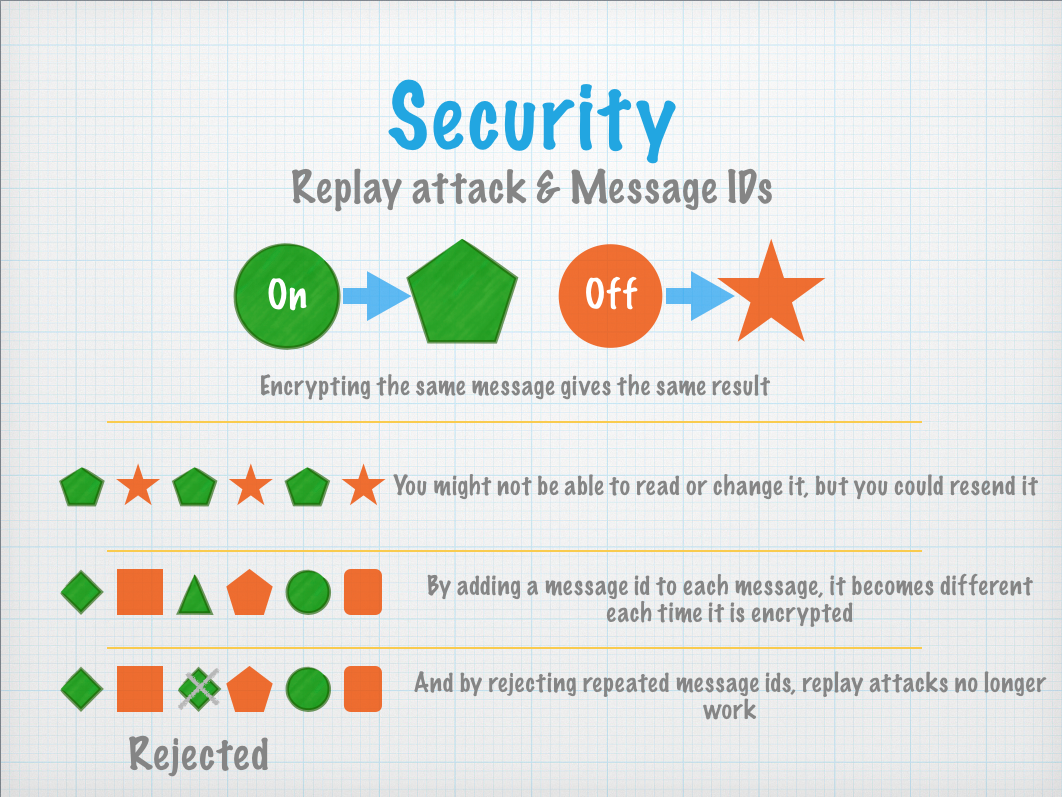
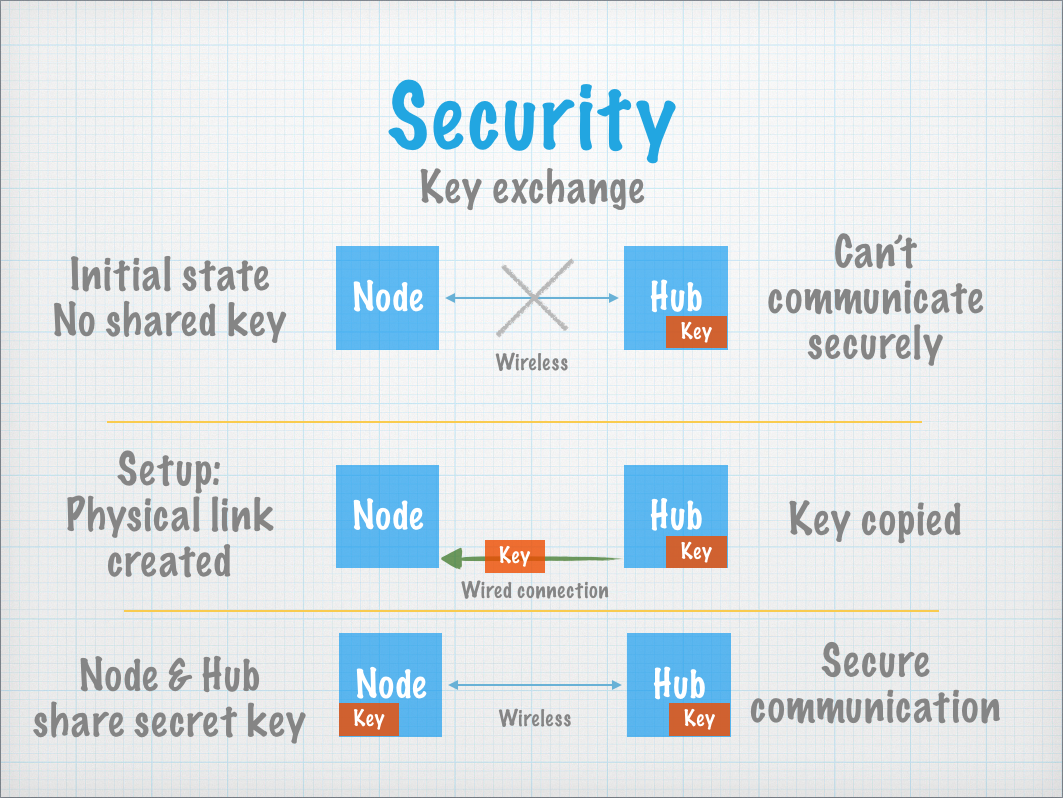
Another thing Iota provides is security.
By default, the radios used in Iota send messages in plaintext, which means anyone can listen in or even inject their own messages.
You might not care if your neighbour knows the temperature of your room, but you sure don't want them switching your lights on and off in the middle of the night!
To protect your network of things, Iota encrypts messages between the nodes and the hub using the AES encryption standard.
 nathan.andrew.williams
nathan.andrew.williams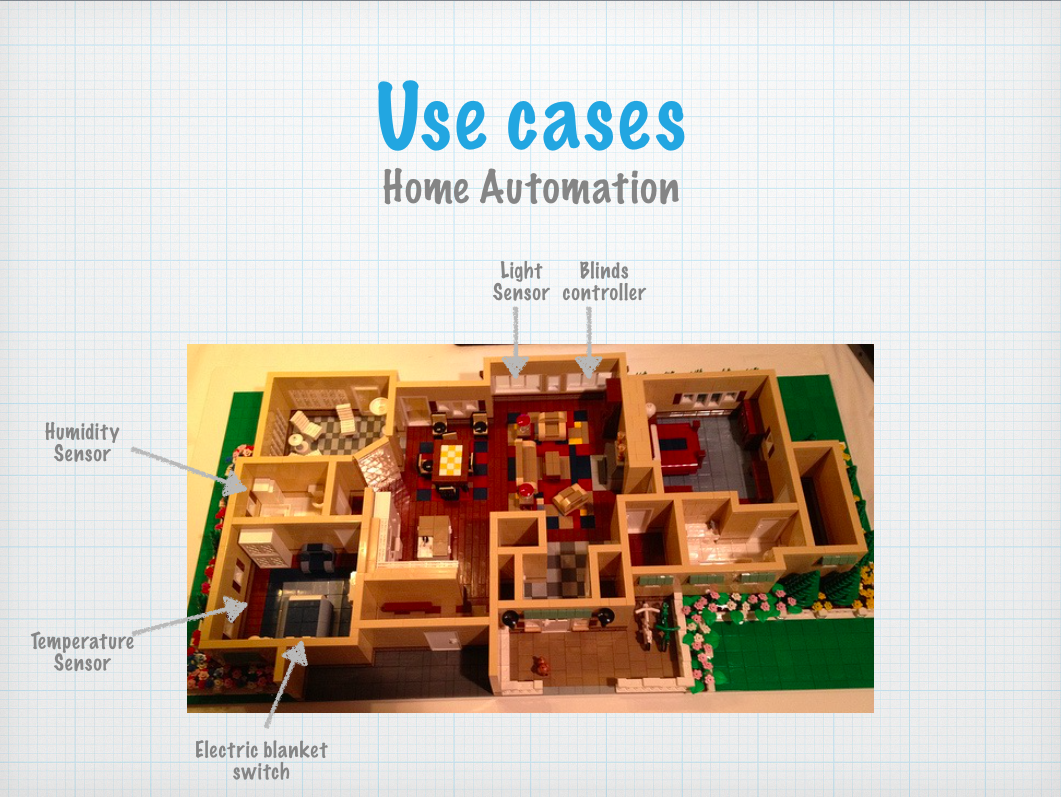










 pastcompute
pastcompute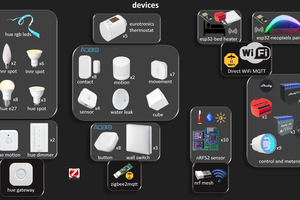
 Wassim
Wassim
 Nuri Erginer
Nuri Erginer
Some of the work I've been doing for a similar project, but for atmega328 and RFM69 (Although I've been meaning to try porting to NRF) may be useful here.
I have power save beacon mode,over the air pairing like Bluetooth, 64 bit timestamps for the message ID that give you time sync to within millisecond as part of the replay protection, ultra low power beacon frames(I'm aiming for under 10uA, with the ability to wake a device up within a minute), a gateway (Currently requires a Raspberry Pi or other computer, and is integrated with my Kaithem framework,but I'll probably make a standalone version eventually).
My overhead is fairly high, but not too horrible, 12 bytes for the less-secure RT frames, 25 bytes for the full packets with 8 byte MACs, and 9 bytes for a beacon frame, in addition to the low level preamble and sync word(6 bytes for RT, 8 bytes for everything else).
Packet size also doubles if the signal gets too weak, because there's a header bit that will turn on a Golay code to correct errors and give you about 30% more range, it can correct 3 out of 24 bits.
In practice I don't think that's as much of an issue because of the automatic TX power control algorithms to keep from crowding the airwaves.
I also have mesh network support planned for one or two hops, I'm hoping I can just use a heuristic and repeat anything weaker than -55db, unless we see a very strong copy of it while waiting a random time to send it. I think that should be fairly efficient with bandwidth.
What I don't have is an application layer, just a pipe to send raw messages. I'd really like to define a standard way to read, write, or request registers so things could be truly plug and play though.
https//github.com/EternityForest/SG1