DRM-114 allows both public (broadcast) and private messages to be exchanged with other DRM-114 badges optically. It is entirely open hardware and almost open firmware (keep reading for why).
The messages are encrypted with AES-128, with a (pseudo-)randomly chosen key for every message. The key is sent along with the message, but the key is protected with a proprietary key protection algorithm that is not open-sourced. The key protection mechanism is a trade secret and acts as an "effective access control mechanism" as defined by the DMCA, and thus reverse-engineering it is a violation of US Federal law. The entire project's source code (including a software AES ECB, OFB and CMAC implementation) is open-sourced, with the sole exception of the file that provides the key protection function.
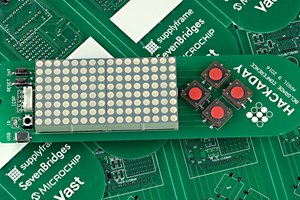
This is an SAO that adheres to the v1.69bis SAO standard and the host badge must provide the functionality of a dumb terminal over the two GPIO pins. The device has a traditional async serial terminal for user I/O and a second for the infrared port. The controller is the ATXMega32E5. Its XCL module is used for the UART dedicated to the IR I/O. The XCL modulates the serial output with a 36 kHz square wave (so a 0 is represented by 36 kHz pulses and a 1 is represented by the LED being off). The IR UART output goes to a MOSFET driven IR LED directly, and an IR receiver provides decoded (that is, the 36 kHz modulation removed) serial back. The IR receiver module is a "side look" version, and the IR LED is mounted on a right angle to direct the energy out the edge parallel to the receiver. In use, a user would hold the badge horizontally somewhat like a remote control.
The UART dedicated to the user terminal is line based and has a simple ">" prompt to start with. Three commands are recognized, each starting with "/" (somewhat like IRC of old). "/name name" sets the name of the badge for receiving private messages (nothing will be done to prevent multiple badges having the same private name and receiving the same messages). "/talk name" sets the destination badge name and will change the prompt to "name>" "/talk" by itself reverts to the broadcast message mode (to all badges). "/help" or "/?" prints out help. Any other line of text is taken as a message to transmit to the appropriate destination. The message is formatted with the target name and the message text and a new random message key is generated. The key is used to generate a CMAC over the plaintext, and then a random IV chosen and the plaintext and CMAC is encrypted. The key is then altered by the key protection method. The final message consists of the protected key, the IV and the ciphertext (which includes the CMAC).
The message is sent with a DLE type protocol. A start-of-frame is sent, followed by the message and an end-of-frame. Both the start and end byte-pairs start with the same introduction byte. If that byte appears organically in the message it is repeated. The receiver always restarts reception when it receives a start-of-frame and submits the accumulated frame whenever it receives an end-of-frame (with some added protection against buffer overrun, of course).
Properly received messages are displayed by sending a carriage return (without a linefeed), then printing the message and then a CR-LF and then re-printing the command prompt and any text already entered.
For best range, the IR LED needs about 80 mA of current. This seems like a lot, but remember that it's modulated with a 36 kHz square wave, so the duty cycle is at most 50% when it's sending a 0 bit and the pulses are quite short (13 µs). But because the current draw is so high, we can't directly drive it from the controller. So an N channel MOSFET is used as a low-side switch (this allows the controller logic to be positive - high for LED on). The badge also sports a visible LED, which is blinked when an "attention" message (either...
Read more » Nick Sayer
Nick Sayer

 Voja Antonic
Voja Antonic
 charliex
charliex
 Amos
Amos
The DMCA has exemptions for education, so if someone simply wants to know how it works and then publish their findings then it's legal.