71FFBB0371FF3C3F5FFE749DFE7E5A5BFAFFFFFFFDDFDAFAFFFFDFFBFEFFFFFFFFFFFFFFFDFFFFDFFBFFFFFFFFFF7F7B797A5A5BFA9FFFFFFFFFFDFD7F7C7FFC7EDFF3FEFFFFFFFFFFFFFEFEFEFEFEF999BD0DEF0E9F69FBD5F8FF1FF7FFFF1FF7FFDF01710BDF017123EEFFFFFFFFFFFFFFDFF7FFBFDE5B3FFF7300714B5D0971BDFFFFDFFF3F7FFF1EFFDFFFFFFFFFFFFFFFBFFFBBDCDF5B7A5AFFFFBA
71FFBB0371FFBC3F9FFB749DFE7E5A5BFAFFFFFFFDDFDAFAFFFFDFFBFEFFFFFFFFFFFFFFFDFFFFDFFBFFFFFFFFFF7F7B797A5A5BFA9FFFFFFFFFFD3DFC9C7EFC7EDFF3FEFFFFFFFFFFFFFEFEFEFEFEF999FF2DEF289F3A3BD0F8FF1FF7FFFF1FF7FF1F04710BDF01712368FFFFFFFFFFFFFFDFF7FFBFDE5B3FFF7F00714B5D0971BDFFFFDFFF3F7FFF1EFFDFFFFFFFFFFFFFFFBFFFBBDCDF5B7A5AFFFFBA
71FFBB0371FFFDE39FF2749DFE7E5A5BFAFFFFFFFDDFDAFAFFFFDFFBFEFFFFFFFFFFFFFFFDFFFFDFFBFFFFFFFFFF7F7B797A5A5BFA9FFFFFFFFFFD3DFF9CBFBC7EDFF3FEFFFFFFFFFFFFFEFEFEFEFEF9B9F94DBF5AE9FBBDDDF8FF1FF7FFFF1FF7FFDF07710BDF017123EEFFFFFFFFFFFFFFDFF7FFBFDE5B3FFF7900714B5D0971BDFFFFDFFF3F7FFF1EFFDFFFFFFFFFFFFFFFBFFFBBDCDF5B7A5AFFFFBA
71FFBB0371FF5D3F7FFA749DFE7E5A5BFAFFFFFFFDDFDAFAFFFFDFFBFEFFFFFFFFFFFFFFFDFFFFDFFBFFFFFFFFFF7F7B797A5A5BFA9FFFFFFFFFFD1DFB8C5FFF7EDFF3FEFFFFFFFFFFFFFEFEFEFEFEF9B9FAED75FAB4F9DDDCF8FF1FF7FFFF1FF7FF1F04710BDF017123DDFFFFFFFFFFFFFFDFF7FFBFDE5B3FFF7900714B5D0971BDFFFFDFFF3F7FFF1EFFDFFFFFFFFFFFFFFFBFFFBBDCDF5B7A5AFFFFBA
71FFBB0371FF3D3F9FF5749DFE7E5A5BFAFFFFFFFDDFDAFAFFFFDFFBFEFFFFFFFFFFFFFFFDFFFFDFFBFFFFFFFFFF7F7B797A5A5BFA9FFFFFFFFFFD5DF7AC46FF7EDFF3FEFFFFFFFFFFFFFEFEFEFEFEF9B9F86DEF29269CDFCE71FF1FF7FFFF1FF7FF9F07710BDF017123DDFFFFFFFFFFFFFFDFF7FFBFDE5B3FFF7F00714B5D0971BDFFFFDFFF3F7FFF1EFFDFFFFFFFFFFFFFFFBFFFBBDCDF5B7A5AFFFFBA
71FFBB0371FF1CE3BFF0749DFE7E5A5BFAFFFFFFFDDFDAFAFFFFDFFBFEFFFFFFFFFFFFFFFDFFFFDFFBFFFFFFFFFF7F7B797A5A5BFA9FFFFFFFFFFDBD18BC18BC7EDFF3FEFFFFFFFFFFFFFEFEFEFEFEF9997BCDEF894F4CDF1B71FF1FF7FFFF1FF7FFDF08710BDF01712368FFFFFFFFFFFFFFDFF7FFBFDE5B3FFF7300714B5D0971BDFFFFDFFF3F7FFF1EFFDFFFFFFFFFFFFFFFBFFFBBDCDF5B7A5AFFFFBA
71FFBB0371FFBC3F7FFF749DFE7E5A5BFAFFFFFFFDDFDAFAFFFFDFFBFEFFFFFFFFFFFFFFFDFFFFDFFBFFFFFFFFFF7F7B797A5A5BFA9FFFFFFFFFFDDDBFA85FFF7EDFF3FEFFFFFFFFFFFFFEFEFEFEFEF999FF8D75FF94F1DDD0F8FF1FF7FFFF1FF7FFDF01710BDF017123EEFFFFFFFFFFFFFFDFF7FFBFDE5B3FFF7500714B5D0971BDFFFFDFFF3F7FFF1EFFDFFFFFFFFFFFFFFFBFFFBBDCDF5B7A5AFFFFBA
71FFBB0371FFFD3FBFF6749DFE7E5A5BFAFFFFFFFDDFDAFAFFFFDFFBFEFFFFFFFFFFFFFFFDFFFFDFFBFFFFFFFFFF7F7B797A5A5BFA9FFFFFFFFFFD7DFCBC7EFC7EDFF3FEFFFFFFFFFFFFFEFEFEFEFEF9B9F86DEFA84F5CDF3371FF1FF7FFFF1FF7FFDF00710BDF01712334FFFFFFFFFFFFFFDFF7FFBFDE5B3FFF5100714B5D0971BDFFFFDFFF3F7FFF1EFFDFFFFFFFFFFFFFFFBFFFBBDCDF5B7A5AFFFFBA
71FFBB0371FF7C3F9FF9749DFE7E5A5BFAFFFFFFFDDFDAFAFFFFDFFBFEFFFFFFFFFFFFFFFDFFFFDFFBFFFFFFFFFF7F7B797A5A5BFA9FFFFFFFFFFDFD7F7C7FFC7EDFF3FEFFFFFFFFFFFFFEFEFEFEFEF999BD2DEFA89F1A3BD6F8FF1FF7FFFF1FF7FF9F01710BDF01712334FFFFFFFFFFFFFFDFF7FFBFDE5B3FFF5700714B5D0971BDFFFFDFFF3F7FFF1EFFDFFFFFFFFFFFFFFFBFFFBBDCDF5B7A5AFFFFBA
71FFBB0371FF3C3F7FF4749DFE7E5A5BFAFFFFFFFDDFDAFAFFFFDFFBFEFFFFFFFFFFFFFFFDFFFFDFFBFFFFFFFFFF7F7B797A5A5BFA9FFFFFFFFFFD7D31BC2FFF7EDFF3FEFFFFFFFFFFFFFEFEFEFEFEF9997BEDEF6F4F3FDF67F1FF1FF7FFFF1FF7FFDF03710BDF01712368FFFFFFFFFFFFFFDFF7FFBFDE5B3FFF5B00714B5D0971BDFFFFDFFF3F7FFF1EFFDFFFFFFFFFFFFFFFBFFFBBDCDF5B7A5AFFFFBA
71FFBB0371FF1CE37FF3749DFE7E5A5BFAFFFFFFFDDFDAFAFFFFDFFBFEFFFFFFFFFFFFFFFDFFFFDFFBFFFFFFFFFF7F7B797A5A5BFA9FFFFFFFFFFD7DFEBC30BC7EDFF3FEFFFFFFFFFFFFFEFEFEFEFEF9B9798DEF4E26AFDF57F1FF1FF7FFFF1FF7FF9F0D710BDF01712334FFFFFFFFFFFFFFDFF7FFBFDE5B3FFF5D00714B5D0971BDFFFFDFFF3F7FFF1EFFDFFFFFFFFFFFFFFFBFFFBBDCDF5B7A5AFFFFBA
71FFBB0371FF7D3FBFF0749DFE7E5A5BFAFFFFFFFDDFDAFAFFFFDFFBFEFFFFFFFFFFFFFFFDFFFFDFFBFFFFFFFFFF7F7B797A5A5BFA9FFFFFFFFFFD1DFB8C5FFF7EDFF3FEFFFFFFFFFFFFFEFEFEFEFEF9B9FACDEF894F4CDF1B71FF1FF7FFFF1FF7FF5F02710BDF017123DDFFFFFFFFFFFFFFDFF7FFBFDE5B3FFF5D00714B5D0971BDFFFFDFFF3F7FFF1EFFDFFFFFFFFFFFFFFFBFFFBBDCDF5B7A5AFFFFBA
71FFBB0371FFFFE3BFF2749DFE7E5A5BFAFFFFFFFDDFDAFAFFFFDFFBFEFFFFFFFFFFFFFFFDFFFFDFFBFFFFFFFFFF7F7B797A5A5BFA9FFFFFFFFFFD5D7A2C7AFC7EDFF3FEFFFFFFFFFFFFFEFEFEFEFEF999FFEDEF8926CCDF0B71FF1FF7FFFF1FF7FF9F00710BDF017123DDFFFFFFFFFFFFFFDFF7FFBFDE5B3FFF5B00714B5D0971BDFFFFDFFF3F7FFF1EFFDFFFFFFFFFFFFFFFBFFFBBDCDF5B7A5AFFFFBA...
WIERD PROTOCOL
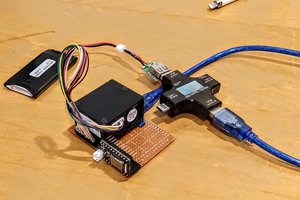
Trying to communicate with a device with an undocumented protocol
 Gabriel
Gabriel


 parasquid
parasquid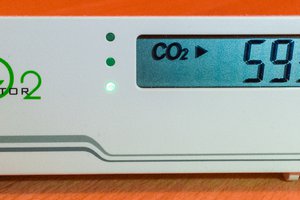
 Henryk Plötz
Henryk Plötz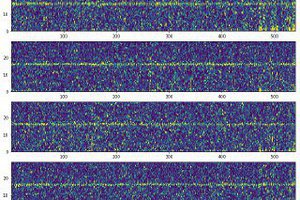
 Konstantin D.
Konstantin D.
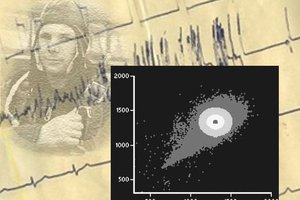
Two additional thoughts - 1) have you looked at the signal[s] with a scope to see the bit rate and if the framing is correct? 2) what happens if you swap the A & B lines for the RS485 - I've seen that sort of weirdness when I had them reversed when working with Modbus & other RS485 stuff. All the "FF' char is what you would see if the device is pausing between char & the polarity is inverted.