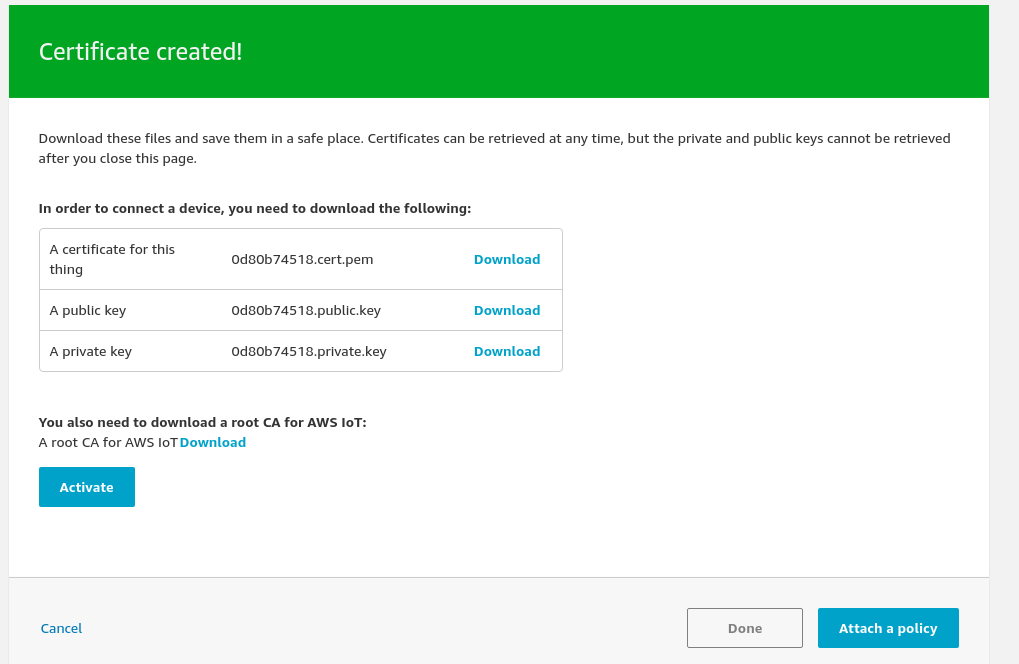
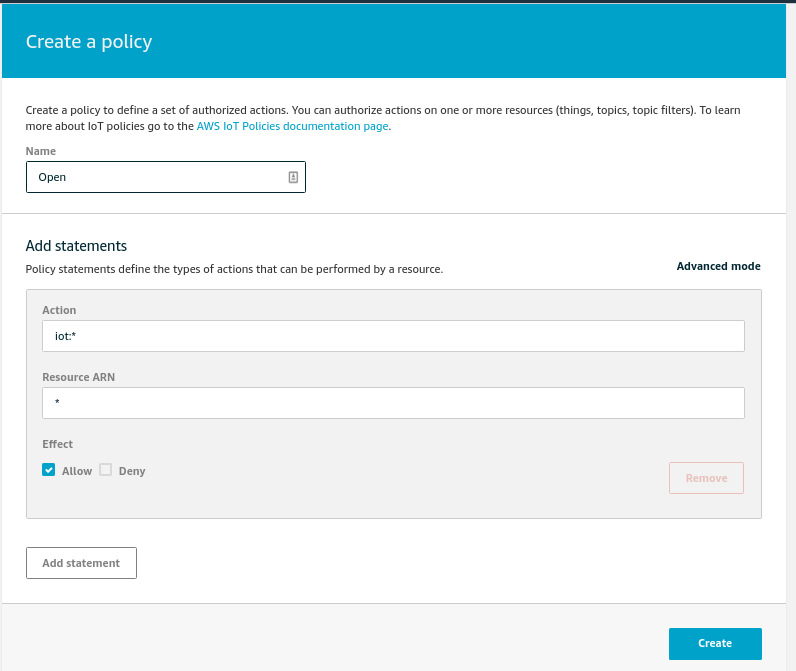
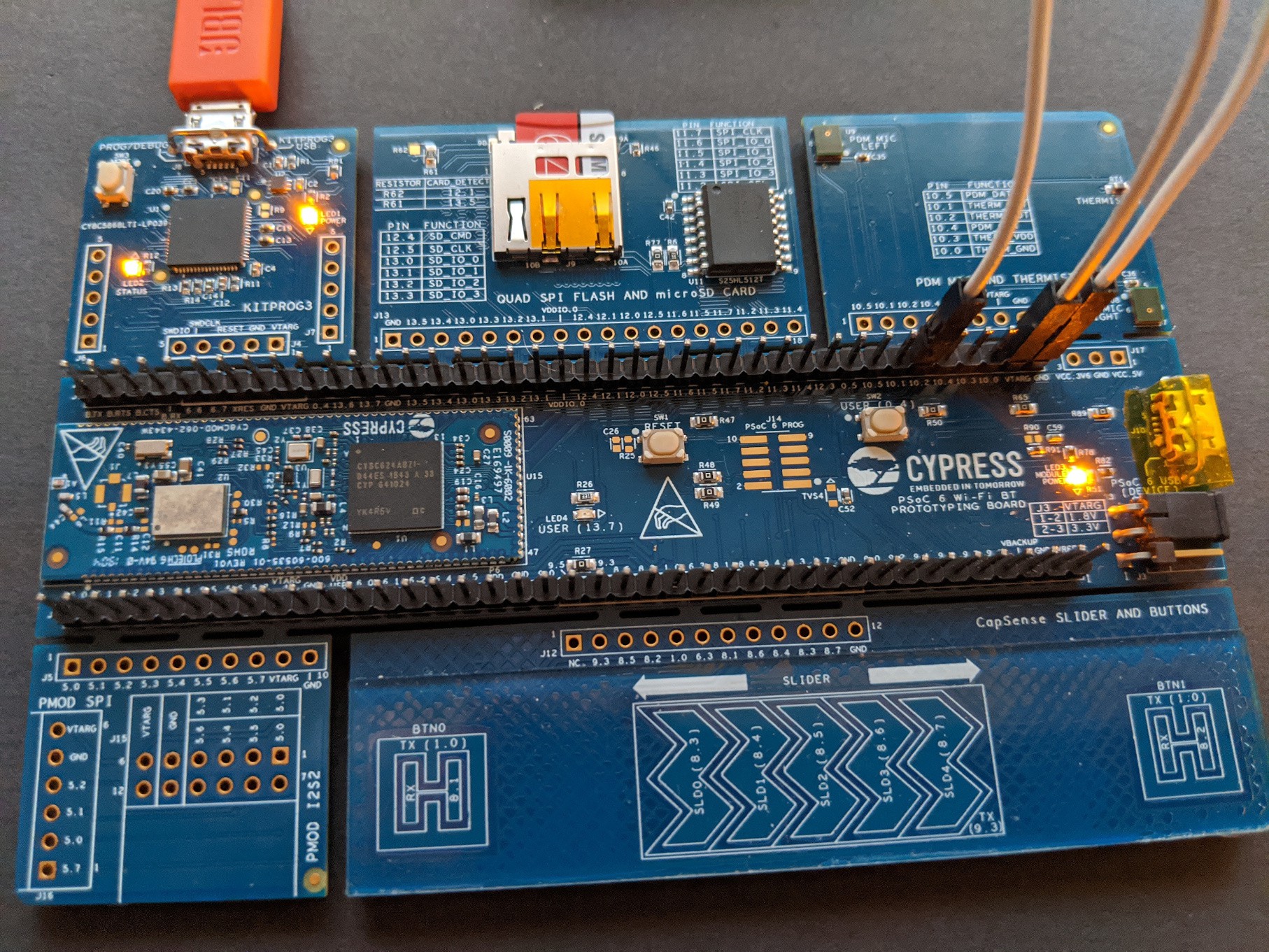
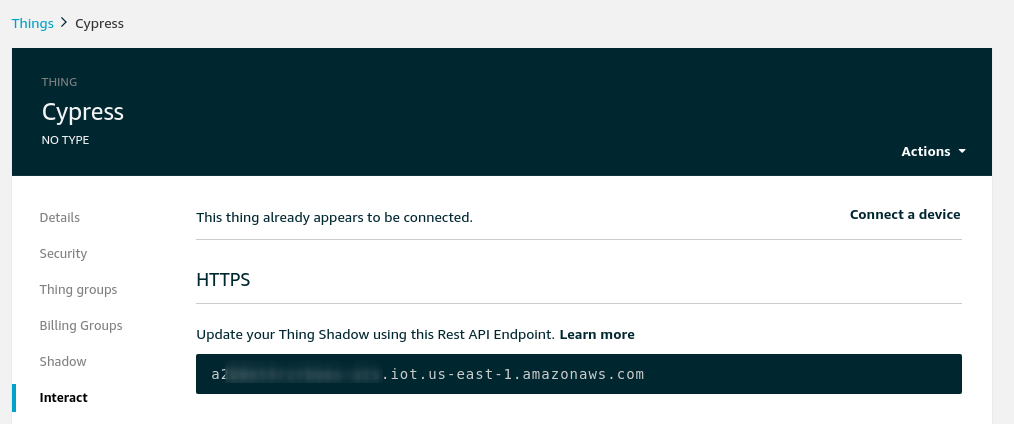
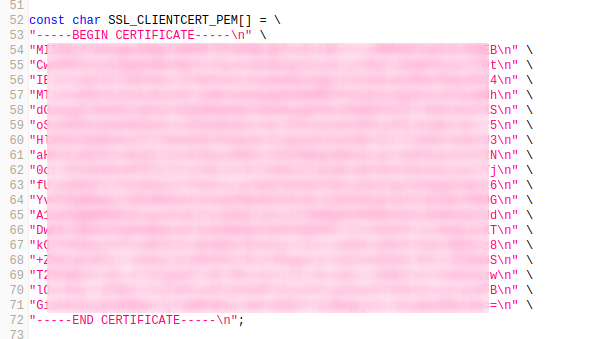
This project takes a look at using one of the two Cypress PSoC 6 wireless kits to connect to the AWS IoT cloud. Using MQTT with TLS, we then publish some data collected from a light sensor. The project goes step-by-step over getting AWS IoT set up (not an easy thing without instructions!) as well as modifying the example code Cypress provides to publish our collected data.
Cypress PSoC 6 and AWS IoT
A quick look at the new Cypress PSoC 6 boards and getting them connected to AWS IoT services
 Alexander
Alexander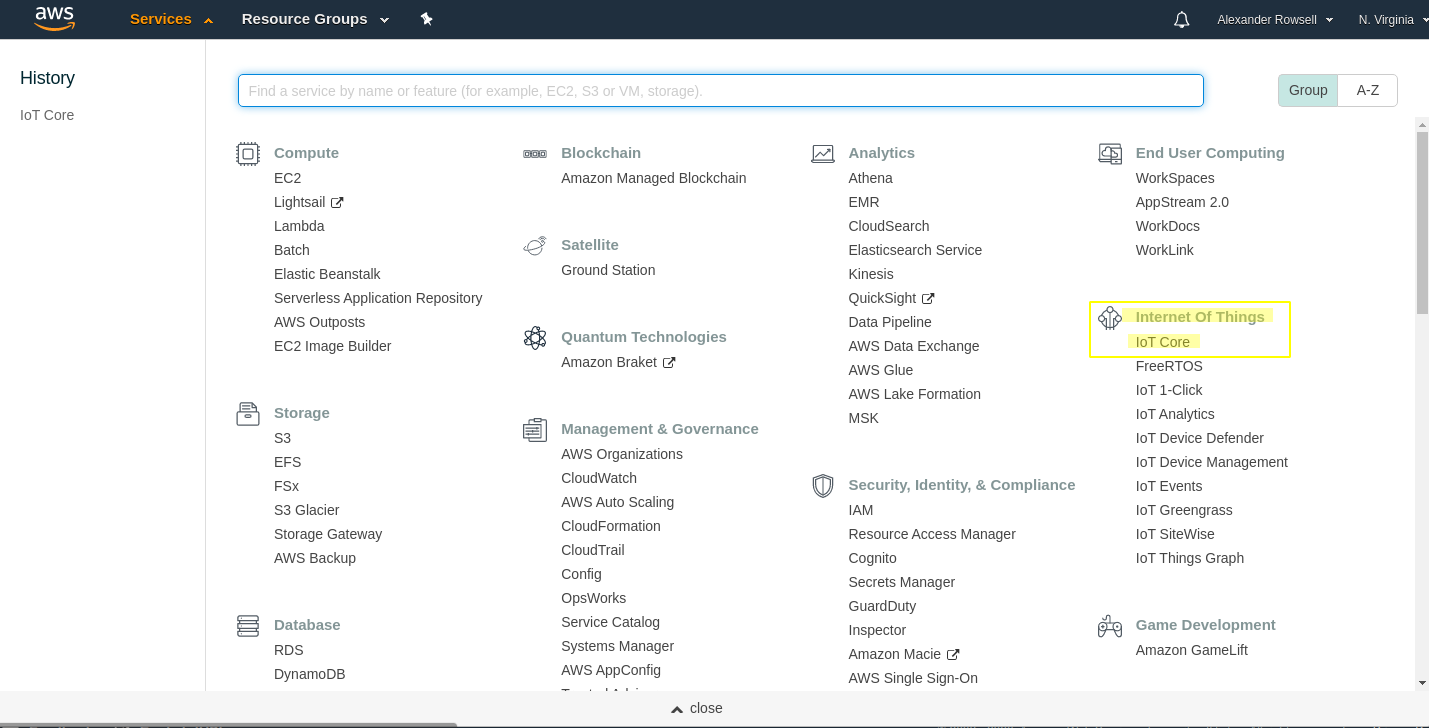




 Willem Jan Faber
Willem Jan Faber
 IoTool
IoTool
 JayeshRajam
JayeshRajam
@Alexander, Bigly Thanks!!! Saved me countless hours of reading and trial and error, I am publishing and subscribing, sending commands to my device via IoT Core!
William