Workshop Details:
In this workshop, attendees will work on a breaking into a real-life example of encrypted 3D-printer firmware. We will do it together, step-by-step, each time running a small snippet of code inside a Jupyter notebook. We'll try many different approaches: frequency analysis, known-plaintext attacks, floating point interpolation, and even use our knowledge of the ARM architecture to defeat the chiper! We will use tools like Matplotlib and SciPy, and give you a framework you can use in your next reverse-engineering challenge.
Instructor: Uri Shaked
Uri is the co-founder of Wokwi, a platform for teaching Arduino, IoT, and Electronics. He co-organizes the IoT Makers and JavaScript Israel meetup groups. He also regularly blogs about his maker projects, which combine web technologies, electronics, 3D-printing, robotics, and neuroscience. Uri is a recognized Google Developer Expert for Web Technologies and Firebase.
 Lutetium
Lutetium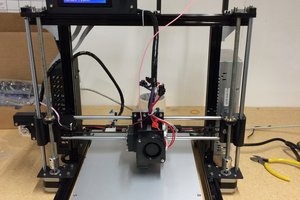
 dar.ryl
dar.ryl
 jon.knutton
jon.knutton
 paul hardin
paul hardin
 Fiberpunk
Fiberpunk