Defensive mode - Defensive mode protects the end user from the spoofer by disconnecting the user's system from the network. This mode also alerts the user by an audio message as soon as spoofing is detected.
Offensive mode - Offensive mode disconnects the user's system from the network and further kicks out the attacker by sending De-authentication packets to his system, this doesn't let him reconnect to the network until the program is manually reset.
Active Scan - Use when your system is left idle most of the time. Active scan is most efficient method to protect you system and the network from ARP-spoofing incidents.
Passive Scan - Use when your system is busy transferring data through the network. Passive scan is efficient in for constant data transfering devices as your device and the network would be secured from ARP-spoofing incidents without compromising the speed or the network bandwidth.
Records-
The program creates a log file (/usr/shARP/)containing the details of the attack such as the attackers mac address, mac vendor, time and date of the attack.
We can identify the NIC of the attackers system with the help of the obtained mac address. The whole program is designed specially for linux and is written in Linux shell command (bash command). In the offensive mode the program downloads an open-source application from with the permission of the user namely aircrack-ng (if not present in the user's system already). Since this is written in python language, you must have python installed on your system for it to work. Visit https://www.aircrack-ng.org for more info.
Edits -
If you wish to get an audio alert please download espeak otherwise comment out those lines in the source code.
Note -
- I won't suggest using this software over wired connections, especially in offensive mode as it might cause network instability.
- Use the offensive mode only with the NICs that supports monitor mode.
- Offensive mode does DOS attack on the ARP-spoofer. So use Offensive mode only after making sure that you have appropriate right over the network and the devices connected to it and make sure that doing so is legal in your Country/State.
 Abhijit Menon
Abhijit Menon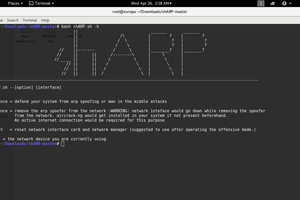

 Gibberfish
Gibberfish
 Andrew Green
Andrew Green