BADGE HARDWARE SPECS
- We'll get there...
Note: Prototype displayed ...
BADGE FUNCTIONS
- We'll get there...
WHO:: We are 5 dudes from California with backgrounds in HW and SW engineering. We enjoy building and hacking things for fun. AND!XOR pronounced..."AND-NOT-EX-OR"...
WHAT:: We built a hackable, open badge for use at DEFCON 26 in Las Vegas and any other conferences in the future. The badge also serves as a dev board for hardware developers of any experience level from novice to expert sorcerer.
WHY:: The purpose is to put some really awesome hardware around the necks of a bunch of hackers and see what they come up with. We hope to encourage others to make use of the badge and come back with their own flavor in years to come, AND to promote embedded development across the community.
HOW:: Pure internet science. We've developed algorithms which calculate the spin rate of cat quarks for generating our ssh keys at a rate of (P+9)/((# of blackberry users)^2), where P is the probability that a cat will leave a house when a door is opened for them.
WHERE:: Caesars Palace, Las Vegas
WHEN:: Aug 9th - Aug 12th, 2018
EXTRAS:: We are spending our free time and money outside of our busy work schedules to develop this from 3 separate locations across California. So we are definitely open and encourage feedback, suggestions, and features to be added onto the badge. If you complain that there are not enough blinky's happening then you are welcome to build your own. Feel free to Leave your comments below if you have questions, concerns, comments, philosophical statements, haiku's, or send us a tweet...that works too.
Twitter:: Check out AND!XOR, our official twitter account on twitter for daily and often hourly updates of the badge process.
 Zapp
Zapp

 Each block is multi-purposed. In the components list all available blocks are listed, of these several of the 3-bit and 4-bit LUTs could be repurposed into CNT blocks.
Each block is multi-purposed. In the components list all available blocks are listed, of these several of the 3-bit and 4-bit LUTs could be repurposed into CNT blocks.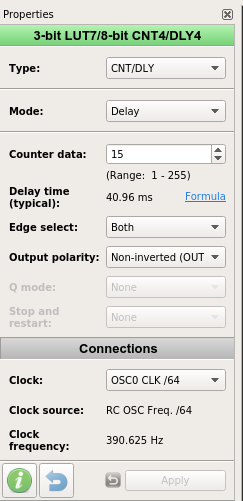 The trick to button debouncing is to measure the delay the button stays low. In this case I fed in OSC/64 to get a 390.625 Hz frequency. The counter counts 15 ticks and is helpful enough to provide a typical delay time of 40.96ms, a healthy debounce delay. Note the Non-inverted(OUT) which will send a low signal after 40.96ms (button is connected to GND).
The trick to button debouncing is to measure the delay the button stays low. In this case I fed in OSC/64 to get a 390.625 Hz frequency. The counter counts 15 ticks and is helpful enough to provide a typical delay time of 40.96ms, a healthy debounce delay. Note the Non-inverted(OUT) which will send a low signal after 40.96ms (button is connected to GND).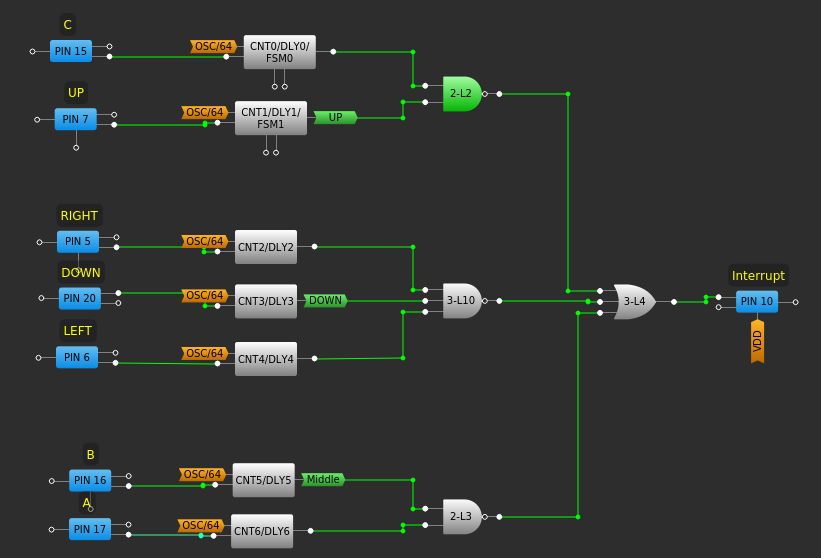







 Benchoff
Benchoff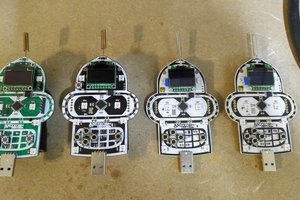

 awkward intelligence
awkward intelligence
Will this badge support custom bling like the Bender S Thompson badge? If so, same steps to create?