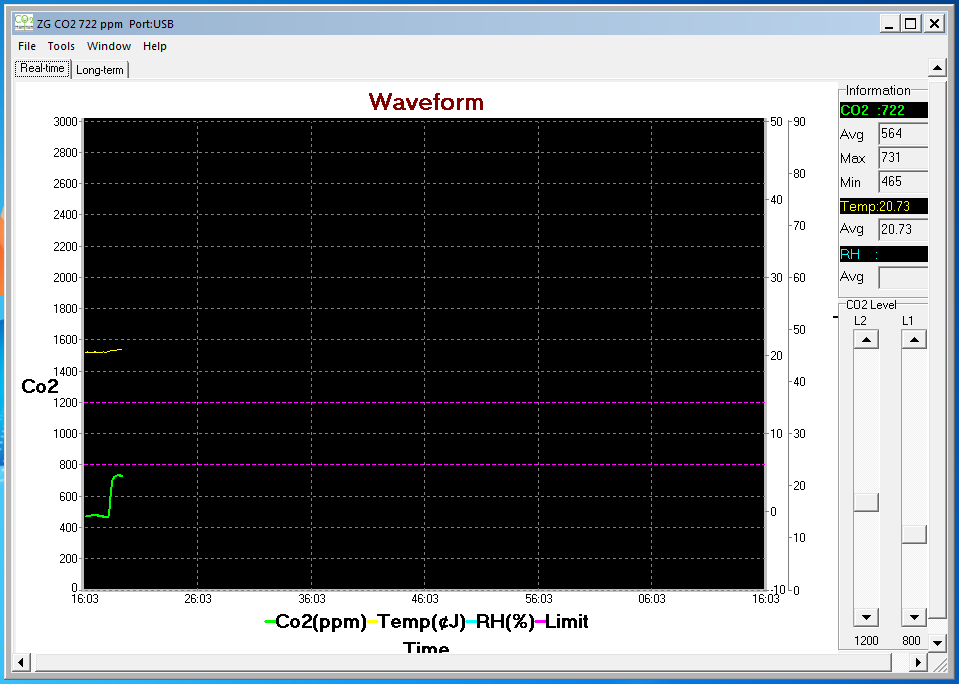
Contrasted with, f.e. CO, monitoring CO₂ seems to be tricky. Most devices in a reasonable price range will only give you a qualitative output: "good"-"bad"-"worse". And even getting this rather restricted kind of data into a computer for logging (and eventually: actions of the home automation system) leads to device prices at ~120€ and well above.
Recently a friend tipped me off to a device (also on amazon.de) that is almost cheap (80€) and actually gives you a CO₂ readout in ppm! Now all I need is to whack at it to get the data into a computer.
 Henryk Plötz
Henryk Plötz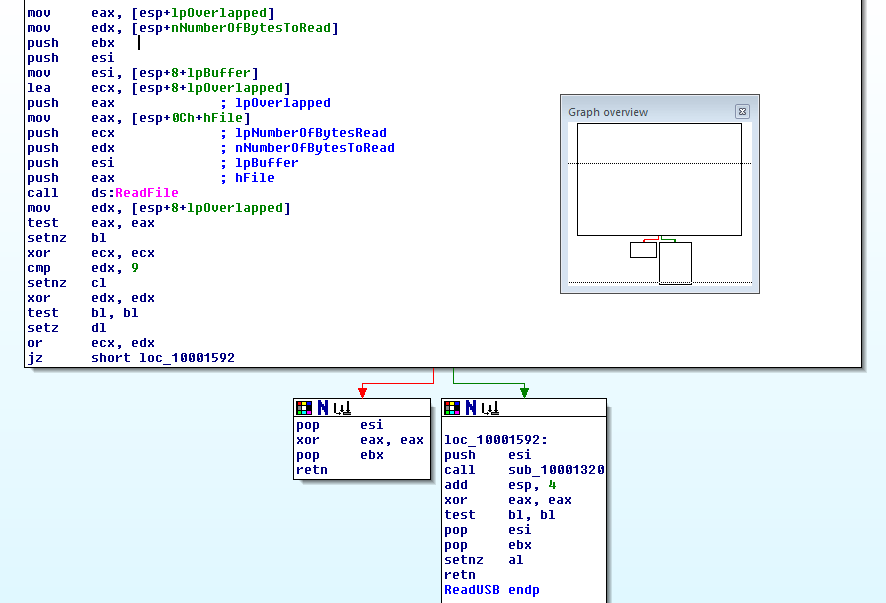









 Marcrbarker
Marcrbarker
 Jacob Sayles
Jacob Sayles
Tiny python app that allow get metrics in console:
https://gist.github.com/GennadySpb/5adddfcf5a45a96956ba73854b419b07