Here's an interesting update - I've just done some glitch attacks against a Raspberry Pi running a stock Linux kernel. I haven't done anything too interesting beyond just proving it works, but there's a lot of useful points you could glitch away. Basically I programmed a raspberry pi with this little chunk o code:
int main(void){
int i,j,cnt;
while(1){
for(i=0; i<5000; i++){
for(j=0; j<5000; j++){
cnt++;
}
}
printf("%d %d %d\n", cnt, i, j);
}
}Which if is working normally should print out "25000000 5000 5000". But by inserting glitches into the power lines of the chips (glitching done with a MOSFET crowbarring the 1.2V supply right at the underside of the BGA to GND), which gives you a power like this:

You can get incorrect results! Here's a print-out where I insert such a glitch event:
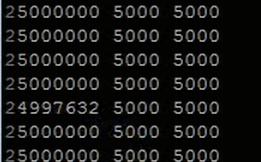
This simple code was chosen since it's easy to insert glitches 'anywhere'. You don't need to go out of your way to determine exact moment of glitching. Note that the glitches are not resetting the system or causing it to crash, or even crashing the specific code. They are just affecting a few instructions such that it counts wrong! If that count is part of something like a bounds check that means you could overwrite an array.
Anyway see the video for more details:
 Colin O'Flynn
Colin O'Flynn
Discussions
Become a Hackaday.io Member
Create an account to leave a comment. Already have an account? Log In.