Samy Kamkar will host the Hack Chat on Wednesday, March 25, 2020 at noon Pacific Time.
Time zones got you down? Here's a handy time converter!

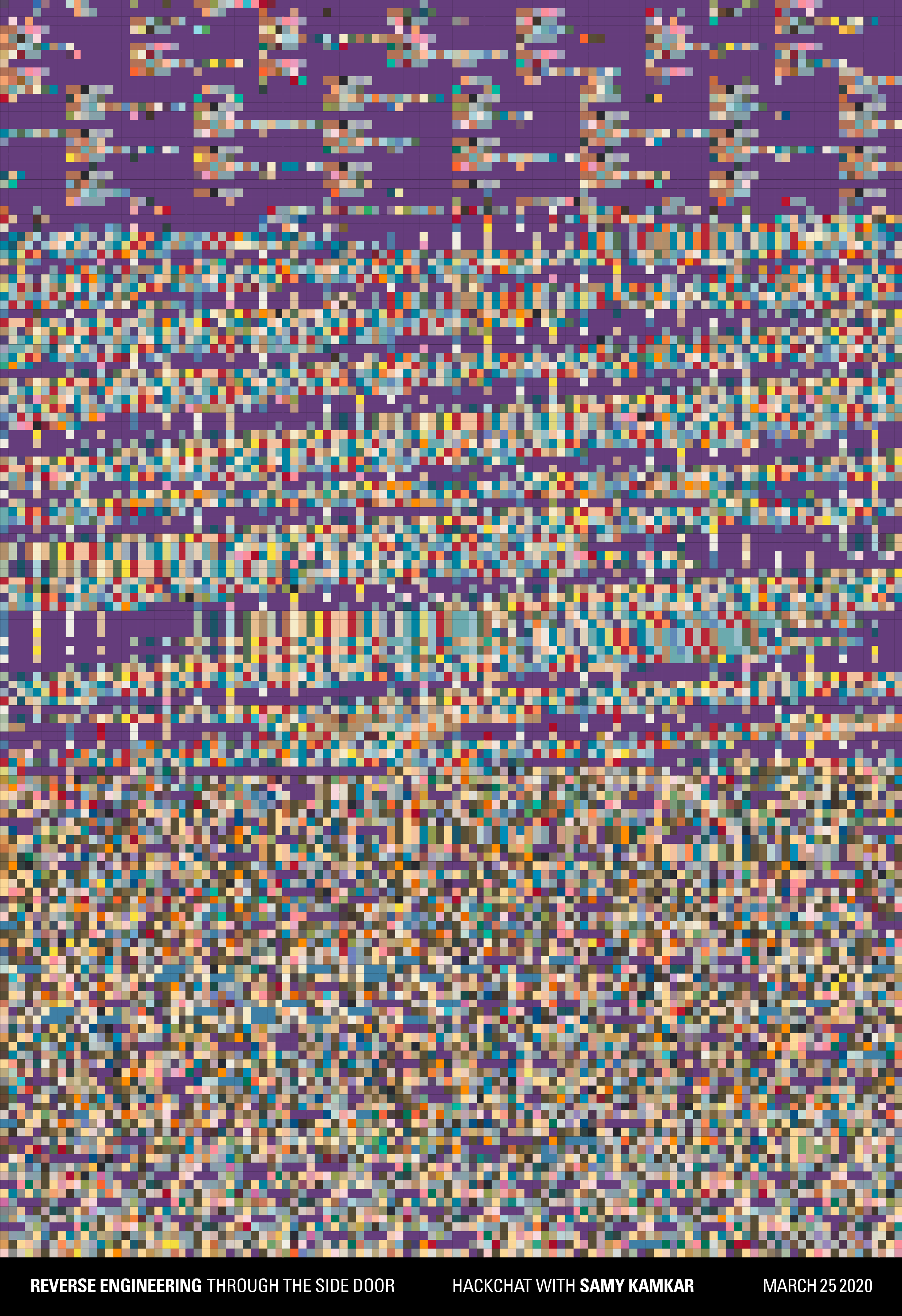
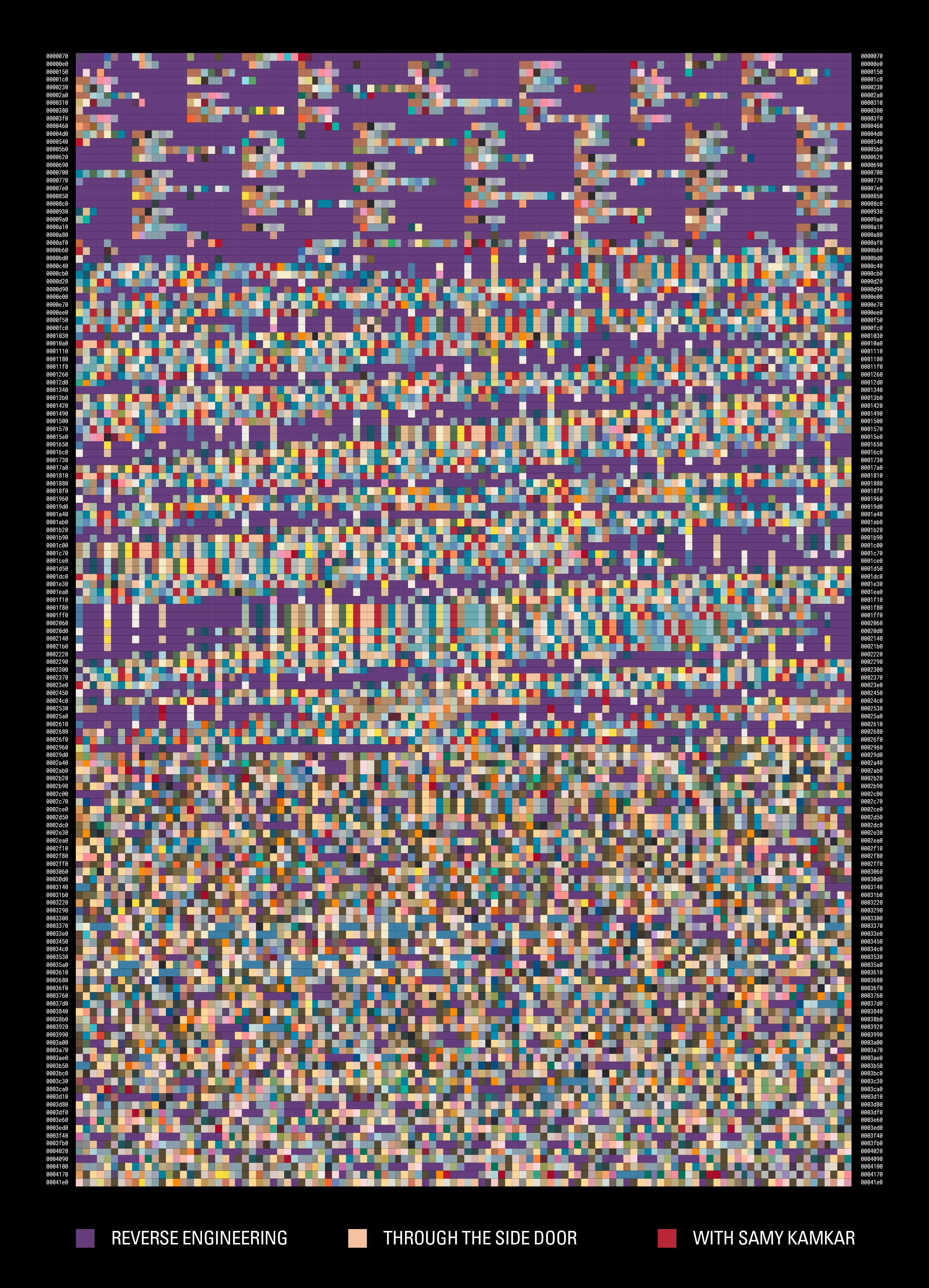
In the world of computer security, the good news is that a lot of vendors are taking security seriously now, and making direct attacks harder to pull off. The bad news is that in a lot of cases, they're still leaving the side-door open. Side-channel attacks come in all sorts of flavors, but they all have something in common: they leak information about the state of a system through an unexpected vector. From monitoring the sounds that the keyboard makes as you type to watching the minute vibrations of a potato chip bag in response to a nearby conversation, side-channel attacks take advantage of these leaks to exfiltrate information.
Side-channel exploits can be the bread and butter of black hat hackers, but understanding them can be useful to those of us who are more interested in protecting systems, and certainly for our reverse engineering efforts. Samy Kamkar knows a thing or two about side-channel attacks, so much so that he gave a great talk at the 2019 Hackaday Superconference on just that topic. During that talk, he teased a few uses for side-channel attacks in reverse engineering, like figuring out how to not spend a couple of hundred bucks to replace your chip-enabled car keys when you lose them.
Samy will "extend and enhance" his Superconference talk by going into more detail on SCAs and their practical applications. It's all white-hat stuff, of course; we're the good guys here, after all. Join us and learn more about this fascinating world, where the complexity of systems leads to unintended consequences that could come back to bite you, or perhaps even help you.



 If I had it to do over again, pen testing would be my thing
If I had it to do over again, pen testing would be my thing




sounds wonderful