The main reasons for this project are:
- I'd like to implement VLANs for security/isolation
- I'd like to be able to VPN into the system remotely
I recently upgraded my current router/AP (Linksys EA6350) to the latest firmware, but despite having newly added VLAN support, it's so minimal and contrived that it feels like more of a pain in the ass than it should be. The documentation also doesn't make clear whether or not I can implement VPN on a VLAN or if it has to be on the default VLAN. In any case, it's annoying at best and I'd like to learn how to implement these things closer to how they would be done in a production/commericial/enterprise environment.
I'm hoping I can still repurpose the Linksys to be a standalone/bridged AP, via VLAN. Fingers crossed, but who know.
As a challenge I'm setting a $60 parts limit for the final implementation. If I spend more, the parts must be immediately reusable in nature (for example, I always need/prefer USB flash drives for storing local installs).


 Keri Szafir
Keri Szafir
 Nolan McCulloch
Nolan McCulloch

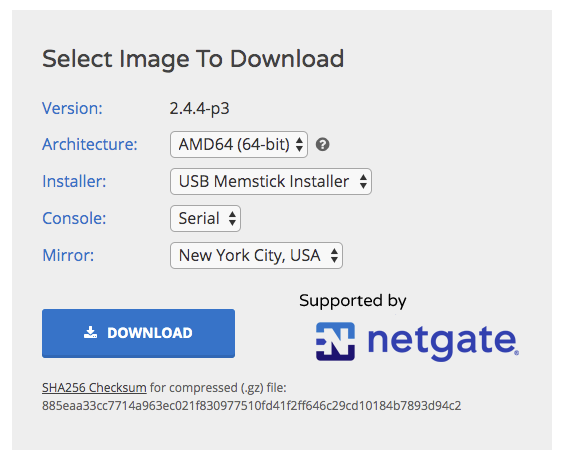
I just remembered something I had to do with my old Atom. For older machines, it's frequently necessary to install pfSense 2.3x and upgrade to 2.4.
Check the important information section of the release notes:
https://www.netgate.com/blog/pfsense-2-4-0-release-now-available.html
Older versions of pfSense can be downloaded here:
http://linorg.usp.br/pfsense/downloads/