Let's talk about hardware switches, advertising profiles and side-channel leaks. ZeroPhone is different from many smartphones in that the GSM baseband is separate from the CPU, so there's no proprietary code running on the CPU that comes from the GSM modem manufacturer. The communications happen through UART and are controlled by and directed through open-source software.
I sometimes got questions about hardware switches. It's a niche but nice feature - not only it's the ultimate power consumption decreasing mechanism, it's also a way to ensure the radio-enabled components can't work when you absolutely don't want them to work - for privacy and safety. ZeroPhone is using off-the-shelf GSM modules - and they have an inner CPU which runs some kind of firmware, and that firmware running on the modem can make it transmit, even though you might not be telling it to transmit. We can implement software kill switches, but maybe the software itself is going to have bugs? The simplest and most powerful "just make sure it's off" hack is cutting the VCC line to the modem, ensuring it doesn't work at all and thus doesn't have the ability to transmit when you want it turned off.
One more reason for that - what if the GSM modem firmware is malicious? We don't know, SimCom doesn't provide much of source code and SDKs, and one of the modem batches they send out could be programmed with a firmware that's slightly different from the widely-used firmware, with some *extra features*. Can we *trust* the modem? No, not really.
So, current ZeroPhone boards have solder jumper pinouts. Those solder jumpers are shorted by default, but you can cut them and solder a switch to the pads, so you could interrupt power to some peripherals. Currently, the only peripheral that has a jumper is SIM800 modem, though - it's the only peripheral it actually makes sense to limit. The ESP-12 that is used for WiFi (though is entirely optional) can also have this kind of switches, but I didn't add them because of routing difficulties - the power track is in the center of the front board. Furthermore, we control the CH_PD GPIO on ESP-12 module anyway, so we can enable/disable the ESP8266 inside by holding the GPIO low or high, both reducing the power consumption and making sure there can be no transmissions (I guess we could also wire a FET in parallel to that signal, just to be sure).
However, there are still problems with the power cutting approach. People usually will still keep the GSM modem powered on because they will actually want to stay accessible to others, to be able to receive calls, SMSs and whatnot. Even when not expecting any calls, or even not wanting to receive any, many people will forget that. So, the advantage of cutting power may be lost - this is a problem, and one that could possibly be solved by using reminders, GSM activity monitoring... Or maybe, even geolocation - basically, trading off privacy for privacy. =D
There's also this thing that keeps popping up once in a while (and it was mentioned in ZeroPhone survey responses a few times) - "using speakers as microphones, and vice-versa". While it works physically, I assume that even the proof-of-concepts would mostly affect the chipsets on modern x86 motherboards, where audio is re-routable from path to path. Even then, I don't think it has a chance of going through amplifiers - so speakers are out of question (and headphone jacks might just have an amp hard-wired instead of having switching logic, though I'm not sure it's not always like that). Realistically, Van Eck phreaking is a much biger potential problem. Will we have speaker and microphone switches on ZeroPhone, though? Yes, see below.
There's a more important thing. It's more important because people haven't yet heard about it as much.
It appears that, in smartphones, app-embedded advertising can use smartphone speakers to transmit data that's modulated by ultrasound. that allow the advertising networks to merge advertising profiles from different devices. Advertising networks can target their advertising much better once they know which devices belong to which people. There's this obvious principle that says "if the devices are near each other most of the time, they probably belong to the same person". This is one of the methods you can use to make cell tower-based tracking easier, and it seems it's used by advertisers nowadays - with ultrasound.
Say, you have 2 phones, one is for private information and one is for work information. If an advertising network can link them together, with all the data they can collect on you from both phones, they can know more about you and target you better (in work matters, this could be disastrous for both you and your work). Also, let's say you install some free app on each smartphone - and it's possible you'll install free-as-in-beer app, with some kind of ad network bundled in. If you permit it to access your microphone, you'll never know when and what is it that it listens for.
The ad networks use two approaches. First - they use ultrasonic-range overlayed sound in TV transmissions, so that it's possible to both link devices (given the transmissions are unique each time, this is a matter of statistics), as well as know what you're watching. Second thing - they use permanently-installed beacons in locations like restaurants and shops, both as parts of customer loyalty programs and, I assume, for general data collection - I'm sure no data collected is ignored.
Of course, for that you need to have some apps installed, those that use the advertising networks that employ ultrasound-based tracking. Chances are you don't, but the technology seems to just start becoming popular, so we don't know where it takes us - and it's better to be cautious.
Some more information - the paper and some Google links
- The paper - released in 2017 (seems so from filename), but mentions of this technology can be dated even to 2016
- Hackaday.com - "ULTRASONIC TRACKING BEACONS RISING"
- "uXDT & Audio Beacons - Introduce your Paranoia to your Imagination"
- "Silently Tracking Users With Ultrasonic Beacons"
- "234 Android Applications Are Currently Using Ultrasonic Beacons to Track Users"
- The company that does this - Wikipedia
Talking more about ultrasound - what else is there that we don't know? Maybe some devices, even while not compromised, emit some kind of ultrasound tones due to their inner workings (say, inductors), and the compromised devices have some kind of profiles that link tones to devices? What if there could be such a profile for ZeroPhone? That wouldn't be the end of the world, but that would suck.
With Raspberry Pi audio done as it's done now - with PWM - there's background noise, and I guess that noise could have its own profile. So, if a ZeroPhone audio output is connected to some kind of speakers, it's possible that some software could determine its presence in the room (that's excluding the obvious "scan for Raspberry Pi MAC addresses" part.) Is it realistic? I don't know. Is it addressable? I think so, I should receive simple audio output filter PCBs tomorrow, so we'll see.
... Anybody interested in making a Pi-based spoof ultrasonic beacon that transmits garbage? =D
 Arya
Arya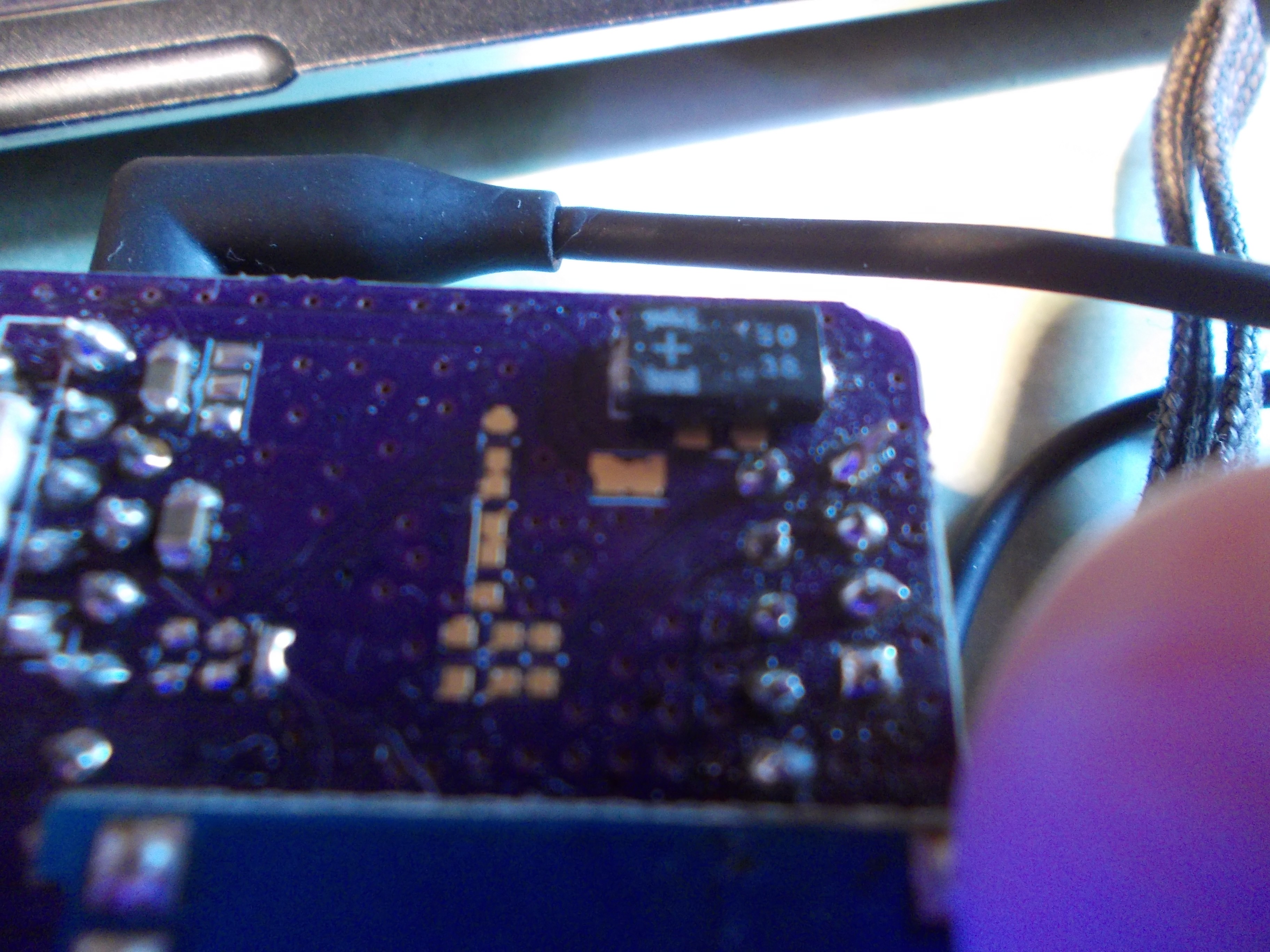
Discussions
Become a Hackaday.io Member
Create an account to leave a comment. Already have an account? Log In.