CARDIS
As a reminder: I'm headed to CARDIS next week in Paris, so hopefully get a chance to meet some people in person!
Mooltipass
I had a few questions about if this project could attack the Mooltipass project. I haven't had a lot of time to look it over in detail, but the actual AES-256 implementation isn't too critical for that project. That's because the only time the key is in use is when you physically have the card inserted into the device - without the card the system won't be processing encryptions.
From a side-channel analysis perspective, attacking the Mooltipass main unit would be pointless. If you had physical access to tamper with the hardware, there is easier things to do. The real question is how secure is the Smart Card used for storing the secret key. This is something I haven't investigated... I know there was previously published attacks against these devices, see for example these slides and paper [2011], also this paper [2012] and this paper [2010]. I've barely had time to read those in depth, so will reserve any judgement until I've got more time! In the mean-time I ordered a bunch of the smartcards used by the Mooltipass to play with. The most likely scenario is that it's possible to break the card, but it takes long enough that you would (hopefully) notice it missing, and could invalidate the affected passwords. If someone really wanted to get your passwords they could always use a big wrench anyway, so it's all about managing the threat.
EDIT: Something else that's worth point out, is it's trivial to purchase smart cards with higher security levels. They are considerably more expensive than the ones being used in the Mooltipass, but if you really wanted to ensure your Smart Card is secure it's possible to do. This might require some work on both the smart card & the mooltipass itself, but one of the nice parts of open hardware is nothing is set in stone. If this was a commercial solution they would probably only ever support the one card, but you aren't locked in like that due to the open-source nature.
0.08 Release
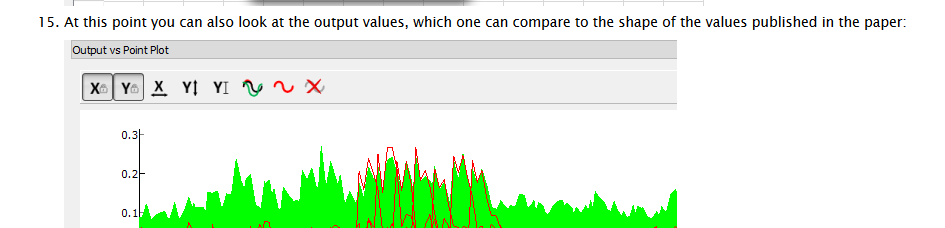
I pushed the 0.08 release. This includes a few goodies, the most interesting is a tutorial on replicating the XMEGA attack. It also includes some fixes for VISA-connected scopes along with documentation for them. That's all for now!
 Colin O'Flynn
Colin O'Flynn
Discussions
Become a Hackaday.io Member
Create an account to leave a comment. Already have an account? Log In.