-
Hacked Twitter Acc Analytics Page
08/04/2019 at 16:25 • 1 comment@hybridanalysis Scan of my un-private #hacked #iphone #twitter analytics page
Found malicious artifacts related to "104.244.42.195": ...
URL: https://cards.twitter.com/cards/18ce54xex7k/7ln6x (AV positives: 1/70 scanned on 07/06/2019 23:32:31)
URL: https://cards.twitter.com/cards/18ce54xex7k/7mgqd (AV positives: 3/70 scanned on 07/02/2019 22:48:09)
URL: https://cards.twitter.com/cards/18ce54wn2p4/7cafy/?m=transaction-ripple&v=037e3a4ea3ff&e=fprLiOGocypqNwuDLD0Y3UkWimTumGnvlTFjDDehDeo= (AV positives: 1/70 scanned on 06/29/2019 08:36:09)
URL: https://cards.twitter.com/cards/18ce54wwchl/7f5vs (AV positives: 1/70 scanned on 05/23/2019 20:35:53)
URL: http://104.244.42.195/ (AV positives: 1/67 scanned on 06/25/2018 21:56:33)
File SHA256: 2beaf5e42dc463c3efe701aa44938fffcfb988f640dc33f20a51394a32f16c15 (AV positives: 1/72 scanned on 08/04/2019 07:16:51)
File SHA256: 5d4a1f4b165af47f8a5e6e25995cd058b10454d7c13db48570ac276d2253d7e2 (AV positives: 1/72 scanned on 08/03/2019 09:07:36)
File SHA256: 1c83115e5d5e68cfcc20c0a9f2ca8ddad0262dcdc0ef11f93081d0eb31fba435 (AV positives: 1/73 scanned on 08/03/2019 10:48:20)
File SHA256: 2430f5bf5606dc7b782cd2fb4d6c3322b1937f88027192e2b59f05c680c7af03 (AV positives: 2/71 scanned on 08/03/2019 10:41:39)
File SHA256: 8f812113bff364868c9c46c96cac3c8fb96cc33c108f22a361c6a83de9897346 (AV positives: 2/72 scanned on 08/03/2019 11:04:14)
File SHA256: 7d419702a7732e34436c95e1d20a423871c27b69ec4830bb3d912a1146f9ef09 (Date: 03/21/2019 08:21:09)
Found malicious artifacts related to "172.217.4.195": ...
File SHA256: 1c8b03921bffc38281af823e7db17e0dbdfbafe39e7b1b96c0f43f2c7dd069be (AV positives: 58/72 scanned on 08/01/2019 21:34:14)
File SHA256: 6fb0ae3f351806fcc92d9d894f72fd2ea13831f8eb5e14e01a9969d5cf905992 (AV positives: 27/71 scanned on 07/18/2019 22:05:33)
File SHA256: 84bda664d4f6f5da6e06b43fc854123b7bb905c7a87eab7eb4d21c553f74eb8d (AV positives: 1/71 scanned on 07/12/2019 16:43:09)
File SHA256: 4de062a251b1b38575f8e815823b27f05e8a8eba69aec44b89bfa5a88155c747 (AV positives: 48/74 scanned on 07/02/2019 21:52:48)
File SHA256: 3ad692ef350cbbbd5779cf0f86e714f9378b54c8361f2aa99dcbe704daa164f7 (AV positives: 53/70 scanned on 06/10/2019 22:40:21)
File SHA256: d9ae1d7a3953510c6a9f6e66365385da974fd8a7e7a16068333d0afd01497b4c (Date: 03/01/2018 13:38:56) -
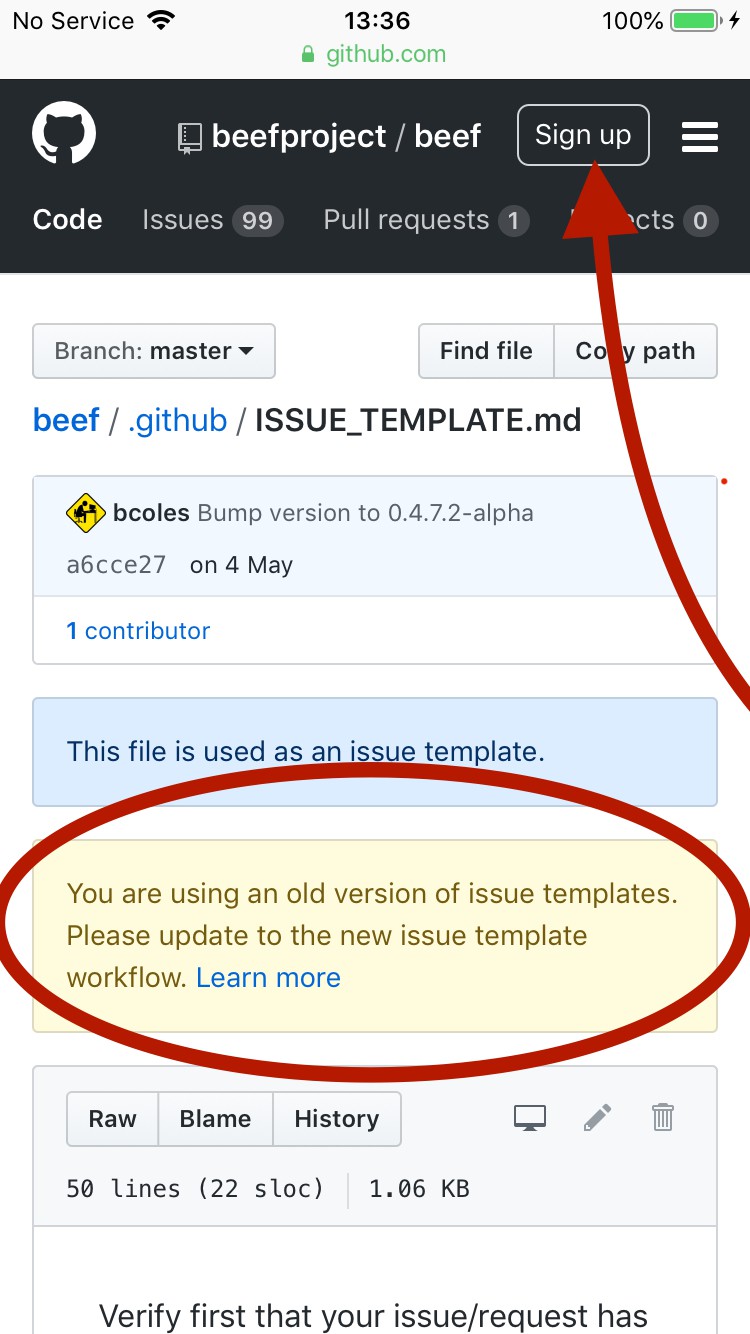
Seems I have BeEF, on an iPhone? as thats all i have
08/04/2019 at 13:03 • 0 commentshttps://github.com/beefproject/beef/commit/1583a10a5a02f3162c9ab7482ab27e813f0abec7#diff-bc67b952e8a9350e40576fa30cdf717c
![]()
core/main/router/router.rb
@@ -1,136 +1,136 @@
Why GitHub?
Enterprise Explore
Marketplace
Pricing
Search
Sign in Sign up
beefproject / beef Code Issues 99
Watch 372
Insights
Star 4,416
Fork 1,061
Browse files
... 11#
... @@ -1,62 +1,59 @@
2 2
3 3
4 4
55#
6 6 77
# Copyright (c) 2006-2019 Wade Alcorn - wade@bindshell.net
# Browser Exploitation Framework (BeEF) - http://beefproject.com
# See the file 'doc/COPYING' for copying permission
# BeEF Configuration file
beef:
version: '0.4.7.0-alpha'
# More verbose messages (server-side)
debug: false
# More verbose messages (client-side)
client_debug: false
# Used for generating secure tokens
crypto_default_value_length: 80
# Credentials to authenticate in BeEF.
# Used by both the RESTful API and the Admin interface
credentials:
user: "beef"
passwd: "beef"
# Interface / IP restrictions
restrictions:
# subnet of IP addresses that can hook to the framework
permitted_hooking_subnet: "0.0.0.0/0"
# subnet of IP addresses that can connect to the admin UI
#permitted_ui_subnet: "127.0.0.1/32"
permitted_ui_subnet: "0.0.0.0/0"
# slow API calls to 1 every api_attempt_delay seconds
api_attempt_delay: "0.05"
# HTTP server
http:
debug: false #Thin::Logging.debug, very verbose. Prints also full exception stack trace.
host: "0.0.0.0"
port: "3000"
# Decrease this setting to 1,000 (ms) if you want more responsiveness
# when sending modules and retrieving results.
# NOTE: A poll timeout of less than 5,000 (ms) might impact performance
# when hooking lots of browsers (50+).
# Enabling WebSockets is generally better (beef.websocket.enable)
xhr_poll_timeout: 1000
# Host Name / Domain Name
# If you want BeEF to be accessible via hostname or domain name (ie, DynDNS),
# set the public hostname below:
#public: "" # public hostname/IP address
# Reverse Proxy / NAT
# If you want BeEF to be accessible behind a reverse proxy or NAT,
# set both the publicly accessible hostname/IP address and port below:
#public: "" # public hostname/IP address
#public_port: "" # public port (experimental)
# Web Admin user interface URI
web_ui_basepath: "/ui"
# Hook
hook_file: "/hook.js"
hook_session_name: "BEEFHOOK"
session_cookie_name: "BEEFSESSION"
# Allow one or multiple origins to access the RESTful API using CORS
# For multiple origins use: "http://browserhacker.com, http://domain2.com"
restful_api:
allow_cors: false
cors_allowed_domains: "http://browserhacker.com"
# Prefer WebSockets over XHR-polling when possible.
websocket:
enabled
# Copyright (c) 2006-2019 Wade Alcorn -...
Read more » -
Seems I have BeEF, on an iPhone? as thats all i have
08/04/2019 at 13:03 • 0 commentshttps://github.com/beefproject/beef/commit/1583a10a5a02f3162c9ab7482ab27e813f0abec7#diff-bc67b952e8a9350e40576fa30cdf717c
core/main/router/router.rb
@@ -1,136 +1,136 @@
Why GitHub?
Enterprise Explore
Marketplace
Pricing
Search
Sign in Sign up
beefproject / beef Code Issues 99
Watch 372
Insights
Star 4,416
Fork 1,061
Browse files
... 11#
... @@ -1,62 +1,59 @@
2 2
3 3
4 4
55#
6 6 77
# Copyright (c) 2006-2019 Wade Alcorn - wade@bindshell.net
# Browser Exploitation Framework (BeEF) - http://beefproject.com
# See the file 'doc/COPYING' for copying permission
# BeEF Configuration file
beef:
version: '0.4.7.0-alpha'
# More verbose messages (server-side)
debug: false
# More verbose messages (client-side)
client_debug: false
# Used for generating secure tokens
crypto_default_value_length: 80
# Credentials to authenticate in BeEF.
# Used by both the RESTful API and the Admin interface
credentials:
user: "beef"
passwd: "beef"
# Interface / IP restrictions
restrictions:
# subnet of IP addresses that can hook to the framework
permitted_hooking_subnet: "0.0.0.0/0"
# subnet of IP addresses that can connect to the admin UI
#permitted_ui_subnet: "127.0.0.1/32"
permitted_ui_subnet: "0.0.0.0/0"
# slow API calls to 1 every api_attempt_delay seconds
api_attempt_delay: "0.05"
# HTTP server
http:
debug: false #Thin::Logging.debug, very verbose. Prints also full exception stack trace.
host: "0.0.0.0"
port: "3000"
# Decrease this setting to 1,000 (ms) if you want more responsiveness
# when sending modules and retrieving results.
# NOTE: A poll timeout of less than 5,000 (ms) might impact performance
# when hooking lots of browsers (50+).
# Enabling WebSockets is generally better (beef.websocket.enable)
xhr_poll_timeout: 1000
# Host Name / Domain Name
# If you want BeEF to be accessible via hostname or domain name (ie, DynDNS),
# set the public hostname below:
#public: "" # public hostname/IP address
# Reverse Proxy / NAT
# If you want BeEF to be accessible behind a reverse proxy or NAT,
# set both the publicly accessible hostname/IP address and port below:
#public: "" # public hostname/IP address
#public_port: "" # public port (experimental)
# Web Admin user interface URI
web_ui_basepath: "/ui"
# Hook
hook_file: "/hook.js"
hook_session_name: "BEEFHOOK"
session_cookie_name: "BEEFSESSION"
# Allow one or multiple origins to access the RESTful API using CORS
# For multiple origins use: "http://browserhacker.com, http://domain2.com"
restful_api:
allow_cors: false
cors_allowed_domains: "http://browserhacker.com"
# Prefer WebSockets over XHR-polling when possible.
websocket:
enabled
# Copyright (c) 2006-2019 Wade Alcorn - wade@bindshell.net...
Read more »
My Pages
Things I've Built
Sadly none all my domains remain in hacker hostage
Thanks to exceptionally poor service from 1and1
Projects I Like & Follow
Share this profile
ShareBits
Become a Hackaday.io Member
Create an account to leave a comment. Already have an account? Log In.
 Lutetium
Lutetium Elliot Williams
Elliot Williams