A Hardware Hack Chat with Bunnie Huang
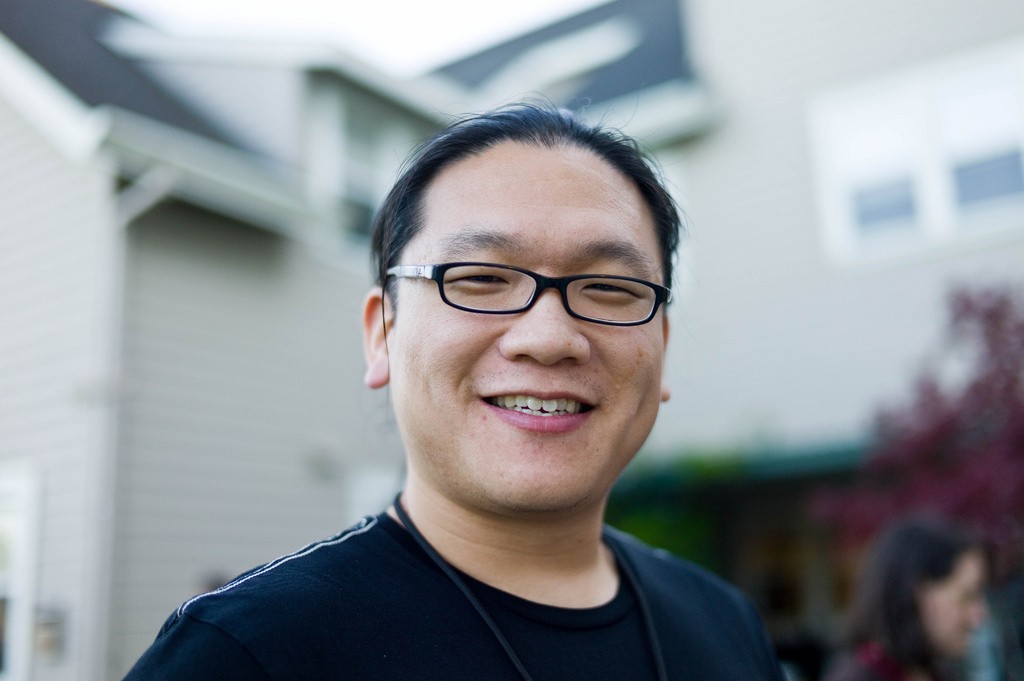 Bunnie Huang is a legend. He’s not just a hardware hacker: he’s a hardware creator, author, and one of the most outspoken folks sharing knowledge and experience from the world of electronics design and manufacturing.
Bunnie Huang is a legend. He’s not just a hardware hacker: he’s a hardware creator, author, and one of the most outspoken folks sharing knowledge and experience from the world of electronics design and manufacturing.
Back in February, Hackaday.io had the honor of hosting a hack chat with Bunnie, where the Hackaday.io community could ask him whatever questions they wanted. We thought the result was interesting enough to bring the conversation outside of the chat window. We’ve cleaned it up a bit (and rearranged replies to account for inevitable chat question/response asynchronicity), but the following is a short summary of the event:
Introspection Engine and Playing the Monitor
Bunnie’s latest projects include Love to Code and NeTV2, but the one that has garnered the most attention is Introspection Engine, a device he’s working on in collaboration with Edward Snowden. Its goal is to help dissidents in high-risk situations know if their communications are being monitored.
Bunnie: Introspection is based on a K22F kinetis CPU and an ICE40 FPGA. The idea is to create a solution which is resistant against state-level adversaries to report if a phone is being monitored. The system reports to its own UI. That's pretty fundamental. The idea is you don't trust or respect third party user interfaces and you really want to be able to validate the entire path from signal to UI.
So, the basic architecture is to find points in the phone which are absolutely, at a physics level, essential for transmitting radio data. Then, we monitor that. If those become active and for some reason we're told they are not supposed to be active, then we know we're probably compromised. So, we have our own separate processor to implement a UI on a separate screen.
At first, just knowing that you’re being monitored doesn’t sound very useful, but it’s important to keep in mind the greater context that information gives you. The more information you have, the better equipped you are to make good decisions about what to do next.:
Bunnie: The idea is that you can know definitively *if* you are being monitored. From that point, you can make the decision to reveal whether or not you know you are being monitored. Consider the fact that if you are being monitored. It's a strategic advantage to be aware of the monitoring and "play the monitor."
Gonkai Engineering Culture
Being a hardware developer, Bunnie has immersed himself in the Chinese hardware ecosystem. In 2013, Bunnie coined the term “gongkai” to describe the ecosystem that has evolved around the open-but-not-quite-open-source sharing of hardware designs (confidential or otherwise) that happens regularly in China. This loose attitude toward sharing IP and documentation has lead to a thriving ecosystem of constantly evolving hardware that’s much cheaper than anything you can buy in the West. Of course that begs the question: Can the West adopt that culture?
Bunnie: I feel that honestly, most likely it will not. The reason I think gongkai won't make it to the West isn't because of physics or language. The major reason is that the Western IP fundamentals were drafted in an era where the Internet did not exist.
For example, when you refer to a cat meme, you don't ask who owns the copyright to the image of the cat. You just feel somehow empowered to "steal" the image originally took and imbued with a copyright by US law and to remix it with a clever subtitle.
In the Gongkai system, we go beyond cat memes to e.g. hardware memes, people feel empowered to remix hardware ideas in the same way that people might remix a cat meme but without attribution to the original photographer of the cat meme.
In the West, we tend to embrace the idea of “open” design through the ethos of Open Hardware and Open Source. You can use open schematics from Adafruit and Sparkfun, open libraries from Arduino, and share your own designs under open licenses, but Bunnie notes that...
Read more »

It's amazing that you got bunnie to come in for a hackchat! Very excited!