I am guessing that is probably running Linux.
The CPU is a Cirrus Logic EP9302 ARM9 SoC
Flash: Cypress S29GL256P 256Mb (32 or 16MB - need to check if 16 or 8 bit mode)
RAM: Micron 48LC16M16A2 256Mb DRAM
EEPROM: 25P05VP
Interfaces include:
1 Ethernet
2 serial ports, one configurable as RS422/RS485 isolated or RS232. The other is RS232 only.
8 programmable discrete inputs
1 relay output
Expansion boards available to add more inputs and outputs
ARM JTAG header
Option 1 and Option 2 headers (for the expansion boards)
2 additional DISPLAY headers, I am assuming to run additional matrix boards.
The display appears to be handled by a Xilinx FPGA with no configuration rom on the board, so it must be loaded at run time.
The SoC also has two USB host ports available, but they are not being used.
I have mapped out the JTAG header
12 pin SMD pads
| 1 | Prst | 2 | Vdd |
| 3 | GND | 4 | Trst |
| 5 | GND | 6 | TDI |
| 7 | GND | 8 | TMS |
| 9 | GND | 10 | TCK |
| 11 | GND | 12 | TDO |
I have scanned for all open ports on the ethernet interface and only port 80 (the webserver) and port 4001 (labeled as binary interface in the configuration screen.)
The manual states that there is a bootloader mode activated by setting DIP switch 8 to the OFF position. You then use serial port 1 and a tool supplied with the display (I didn't get a CD)
I have tried tapping in to the serial port to look for any activity in both boot-loader and normal mode. No activity present.
 Retroplayer
Retroplayer
 Colin Maykish
Colin Maykish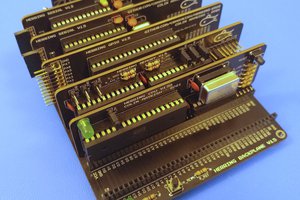
 Ken Yap
Ken Yap
 Plasmode
Plasmode
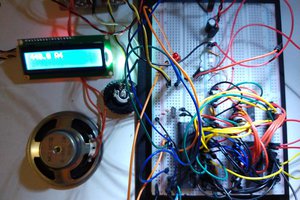
I know this is a long time later, but some possibly useful other designs to use as a reference are the Olimex EP9302 development board and the TS-7300 from technologic (https://www.embeddedarm.com/products/TS-7300)
They provide full linux development environments and all the tools needed for those specific boards.
Cheers,