Step0: Find The Debug Serial Port
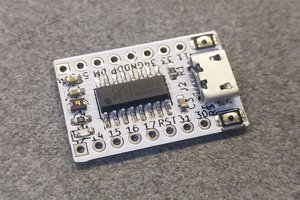
Except when your device runs a standard Android system so you can use ADB in that case, the debug serial is the only mean you can communicate with your device when hacking. Typically the pins of debug serial would have "TX" and "RX" marks around them, but some boards have no hint about this at all. This work may need some experience and patience. When you find it, you can connect it to your computer with an UART to USB converter. Set the baud rate of the serial console tool to 115200 and boot your device. Now boot up log should be printed if everything are done correctly.Step1: Retrieving script.bin From Your Device
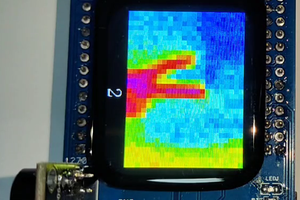
script.bin is a board-specific binary "configuration file" used by Allwinner-specific drivers in the kernel with information on how to set-up various devices, ports and I/O pins on boards with Allwinner SoCs. The corresponding human-readable file format is FEX, it is possible to convert .bin to .fex and back by using Sunxi-tools. [1]
script.bin resides in the bootloader partition of the ROM on your device. After being converted to its human-readable counterpart ("FEX"), you can gain much information about your board like the enabled peripherals and their corresponding pin assignments, yet it is not always accurate. When building your own kernel for your board, you will also need it as a reference when writing the device tree for mainline kernels, or use it directly for Allwinner customized kernels (aka legacy kernel), thus retrieving script.bin is essential for subsequent hacking. There are many approaches to retrieve script.bin from a board and most of them are described here, however, not all of them works for some specific devices, and if you have bad luck, just like my case in this board, non of these approaches works at all. That is not a common case, so try the methods that are most convenient for you in that link first. My suggestion is to use the sunxi scriptextractor tool but it requires you to compile the tool first.References
- [1]Script.bin
 SdtElectronics
SdtElectronics
 kingham xu
kingham xu
 Gergely Imreh
Gergely Imreh