-
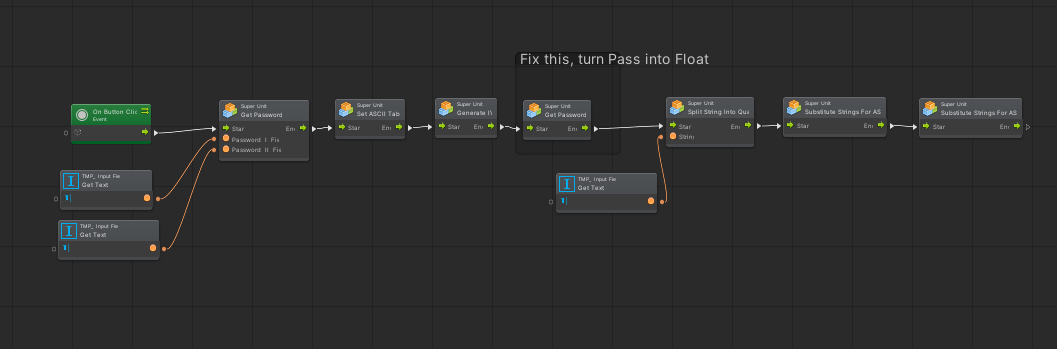
Mini Update - Organization
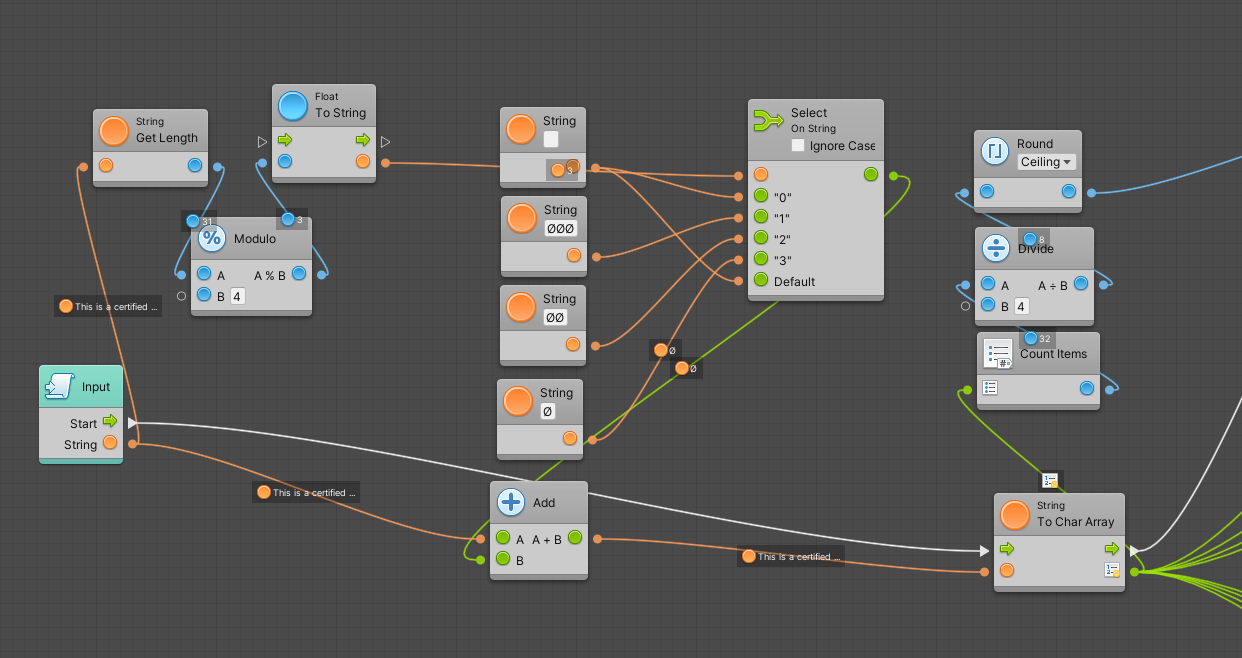
03/03/2022 at 13:52 • 0 commentsHave been working on finishing this sooner than later, organized and got in coroutine for faster speed. Whereas there was a noticeable lag before, the entire process happens within less than a second on a computer with a
- 12 Core 2.30GHz Intel Core i5-10500T and
- 16GB RAM
-
KGE Progress 1
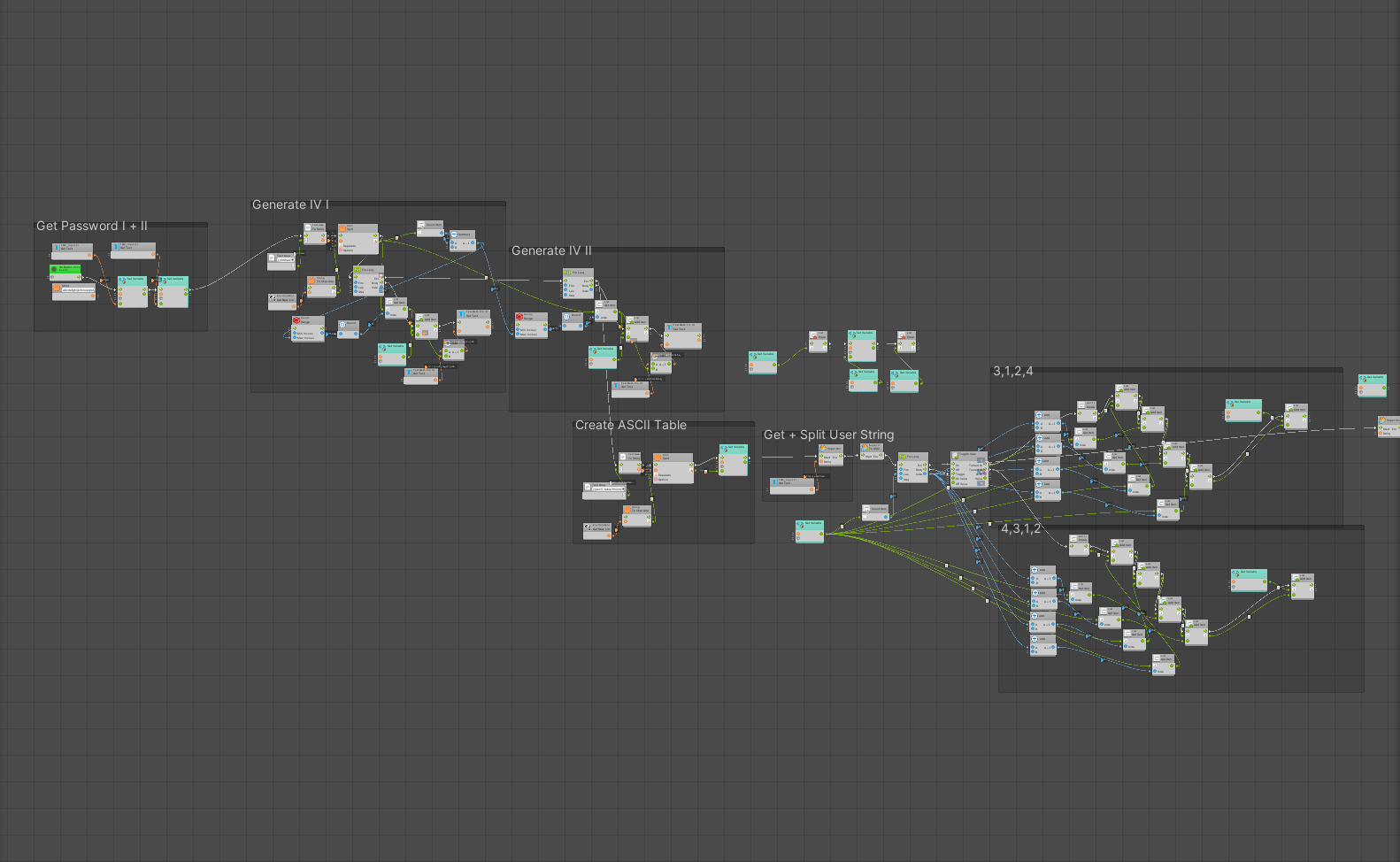
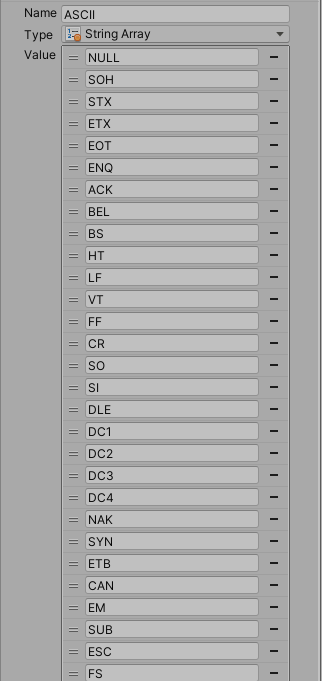
01/23/2022 at 00:43 • 0 commentsOverall, KGE has been created using Unity Bolt Visual scripting. I am going to change it to Python but i'll be using Bolt for now as it really helps with organizing things and even acts kind of like psuedocode.
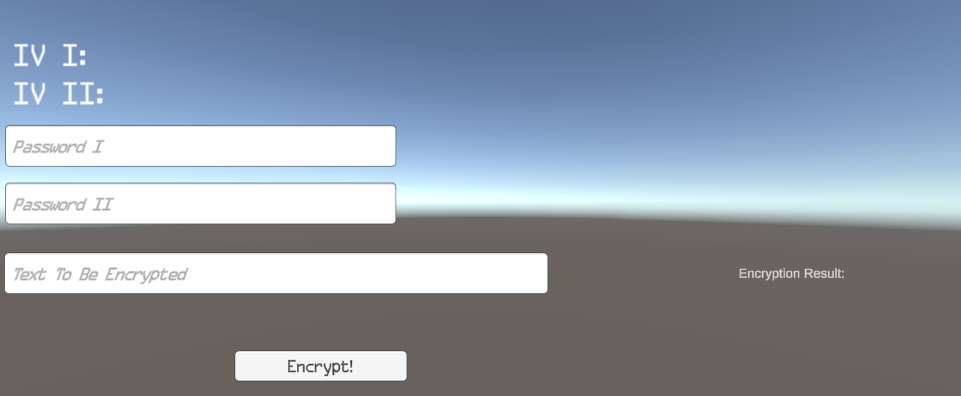
For now, the UI consists of 6 main elements:
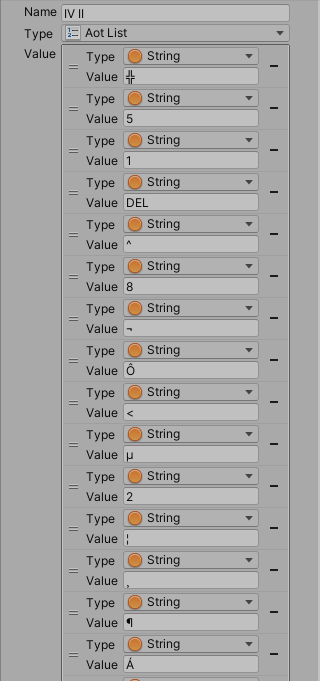
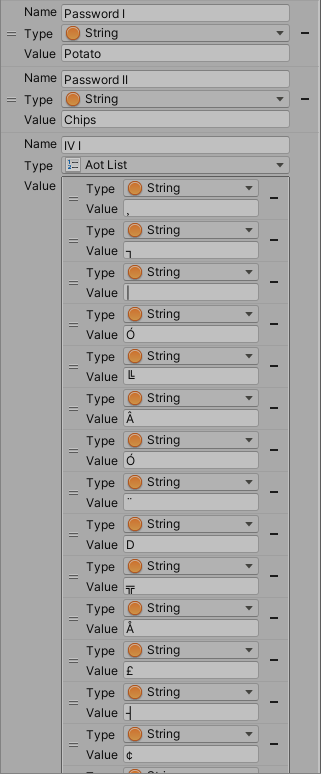
IV I (The first randomly generated string of ASCII characters)
IV II (The second randomly generated string of ASCII characters)
Password I (The password a user sets)
Password II (The password a user, server or the hardware itself sets)
Text to be encrypted (The string a user sets, can be set in html-like format to support documents)
In this example, I set Password I, II and the Text to be Encrypted
Upon pressing Encrypt, the first thing that comes to note is the fact that both IVs are generated.
Unreadable, right? This is the point of these IVs in particular and the reason they look like this will be explained later in this update. For now, lets try to understand what happens behind the scene.
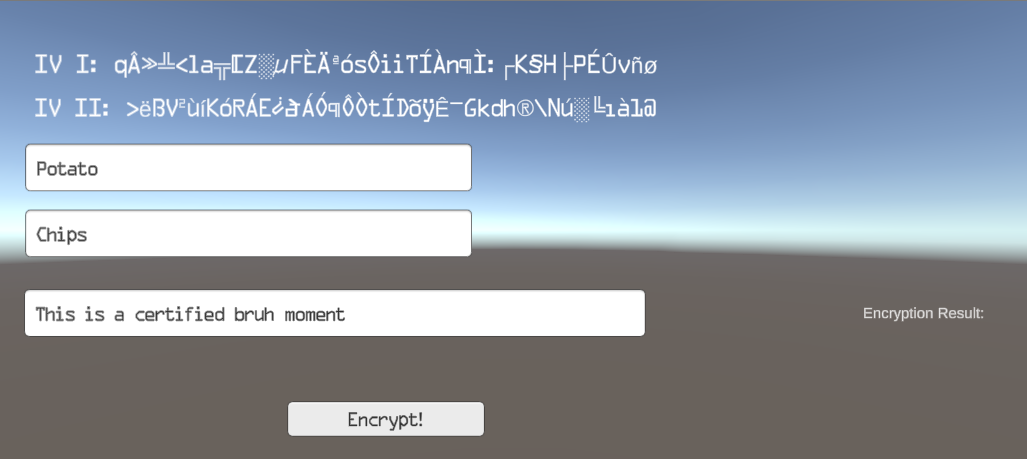
Now you may be thinking "Woah, that's a lot to unravel (or for some of you a little)!" However upon further inspection the system is both simple yet effective.
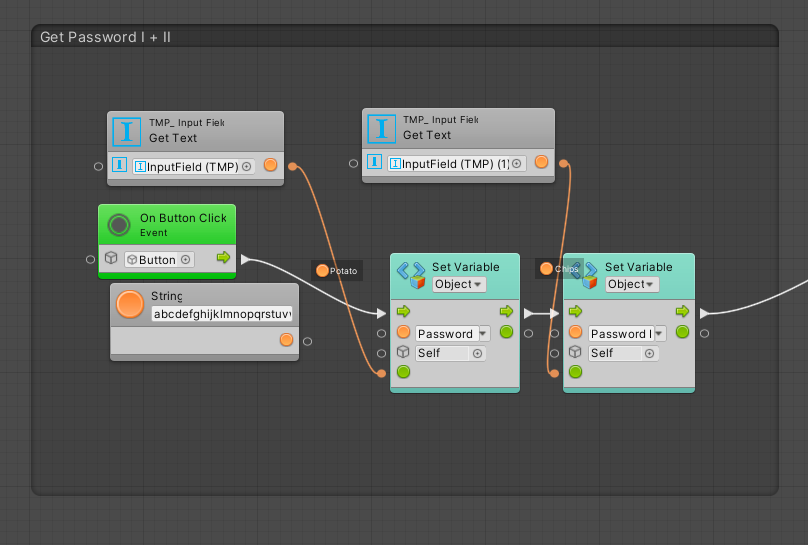
For starters, the text placed into the textboxes are turned into the variable. However, the way this text is taken can easily be changed as you see fit. Also ignore the string box, that is for me to use by the next update.
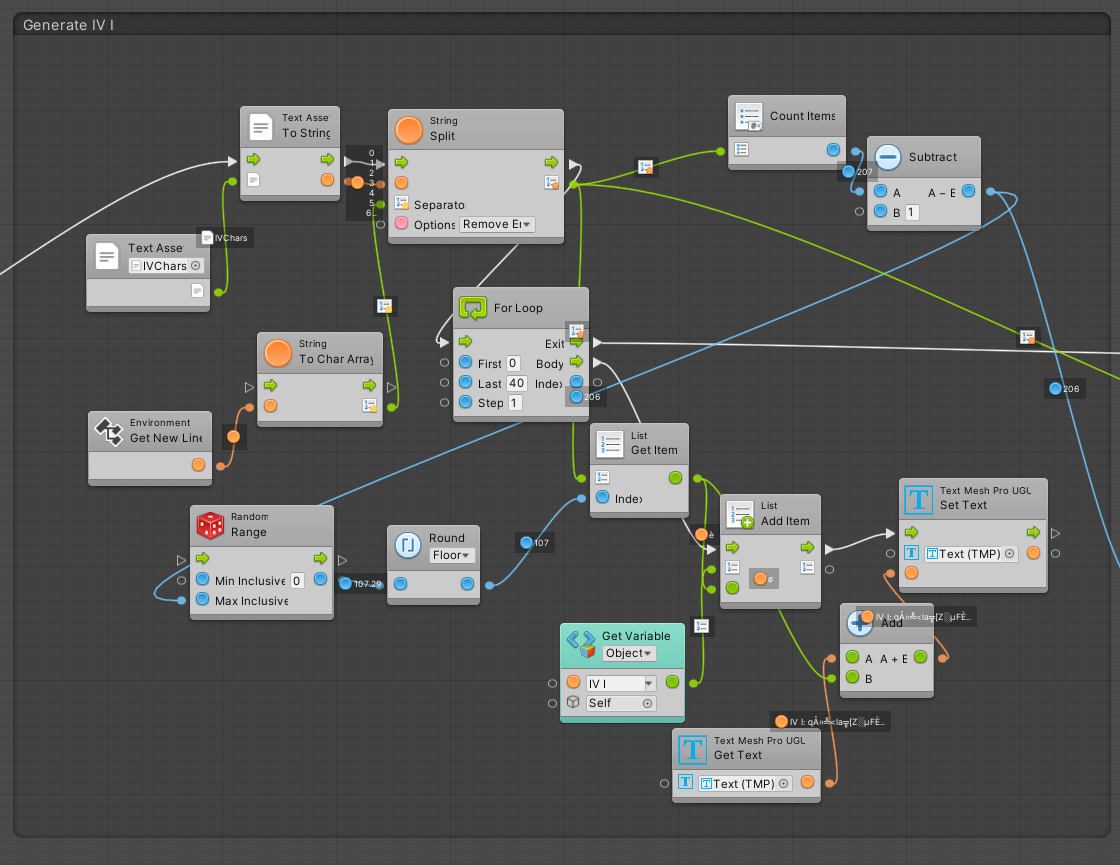
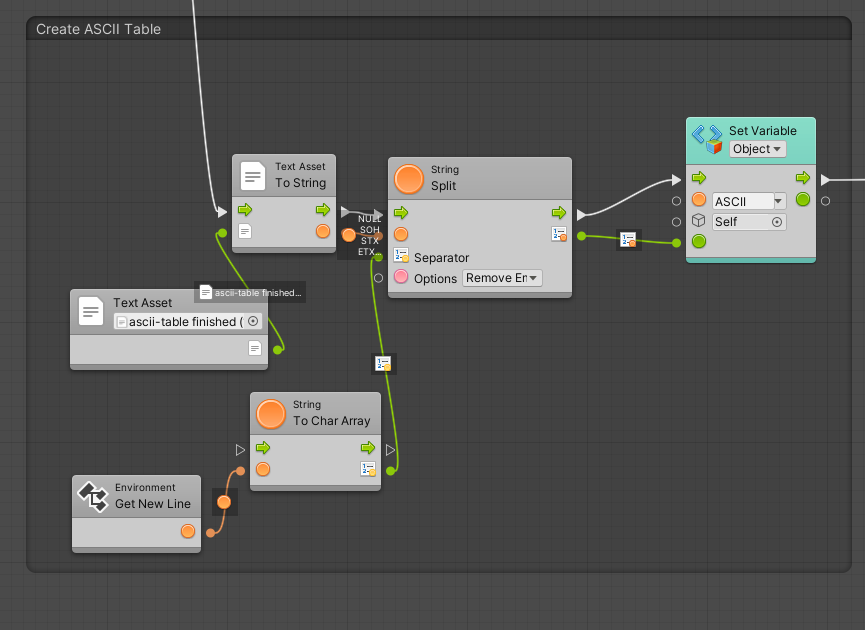
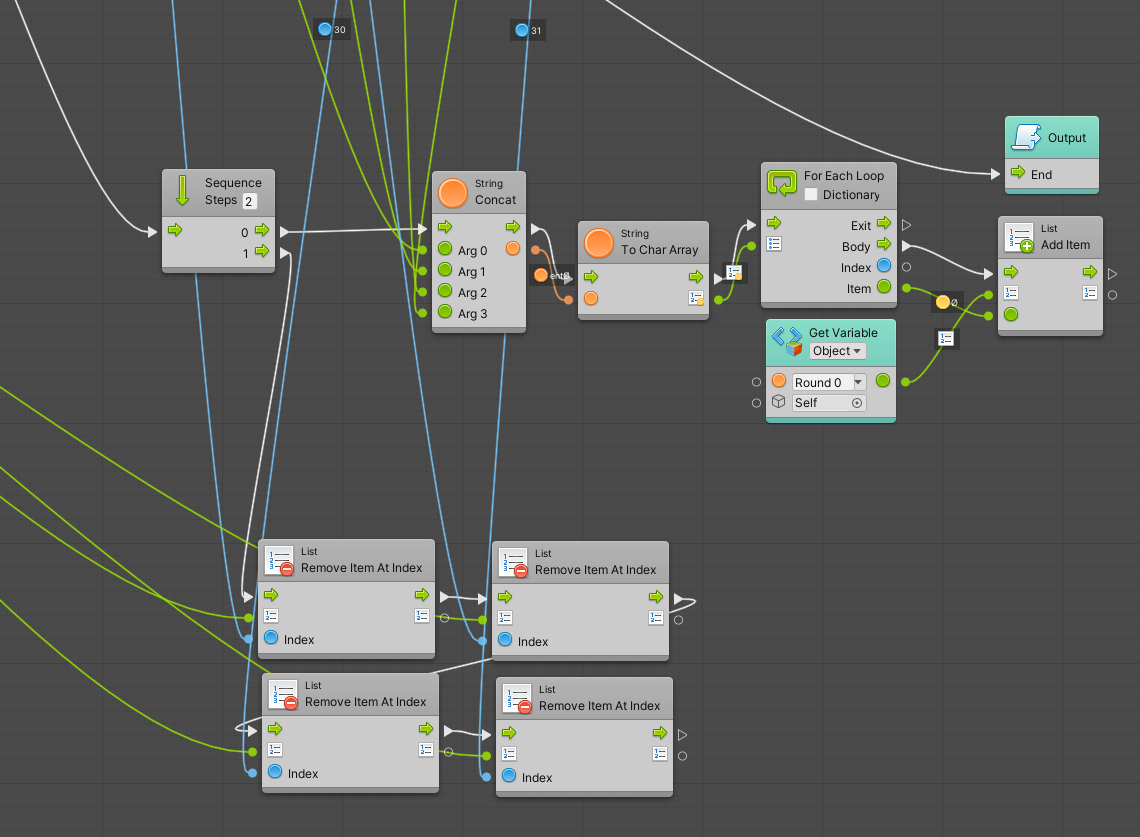
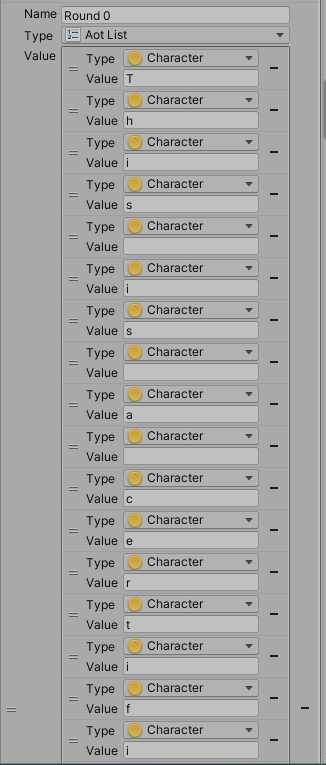
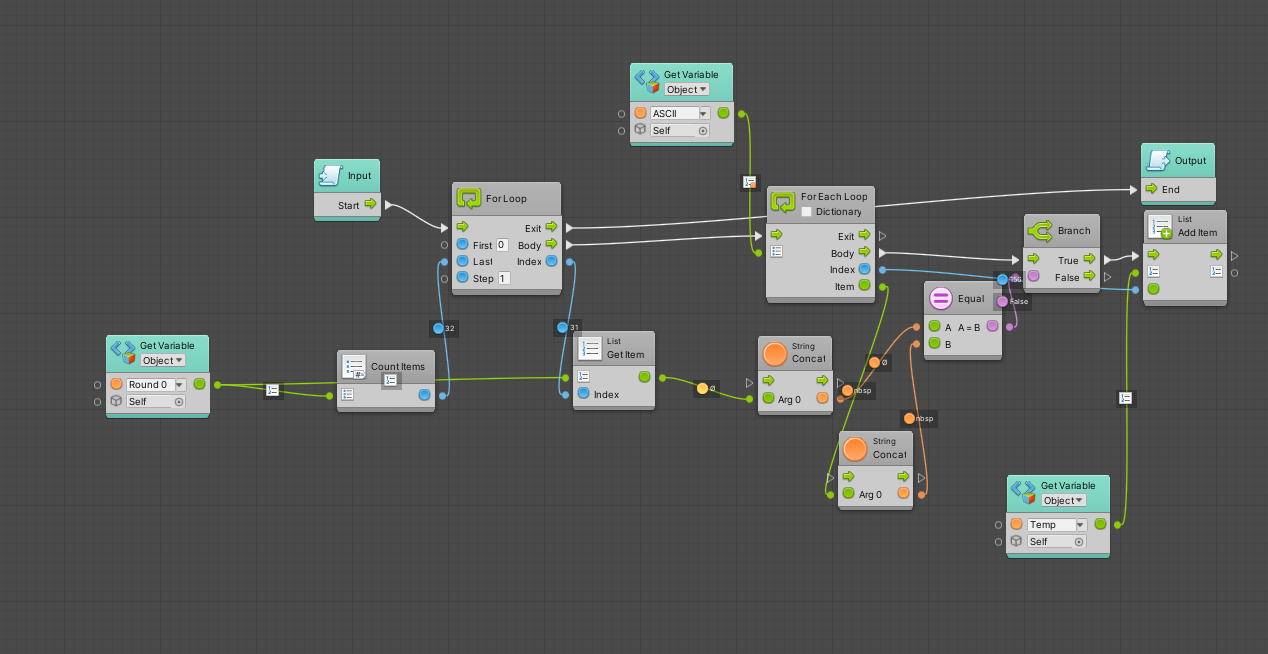
Next up, IV I and II is generated. IV I and II are very similar in generation so there is no need to post IV II. Essentially the program takes a file I created with each newline having a character from ASCII I want to use. Then, that is turned into a list in Unity. A random character is taken 40 times and upon completion the resulting string is turned into a variable.
A file with each newline having an ASCII character is used to create a list and turned into a list, which is saved as a variable.
Now this system is saved within a "Super Unit" (think of it like a container for code which allows you to put a chunk of it into one box instead of being strung out on the main dashboard). Let's investigate this further.
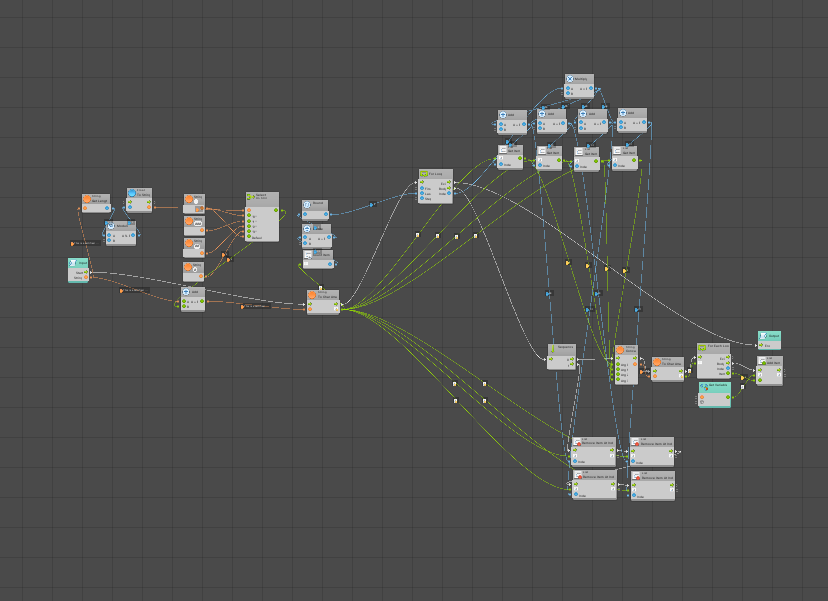
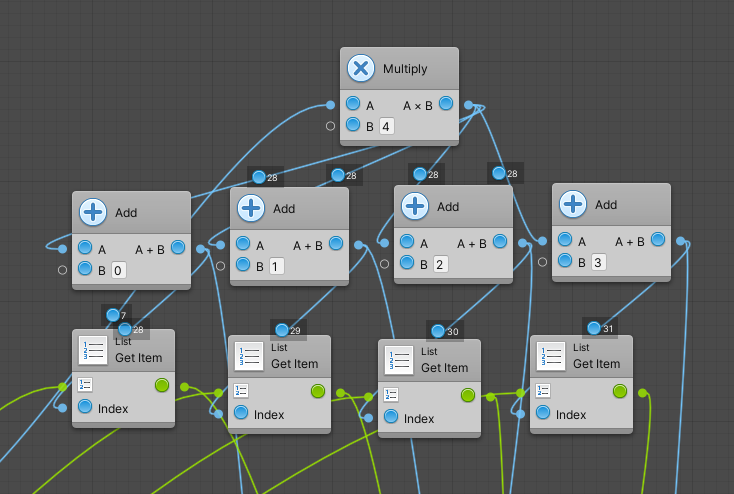
For starters, the User String length is divided by four. If not enough characters exist for four, the null sign is added to a pairing until there is enough for four. All characters are then put into a list.
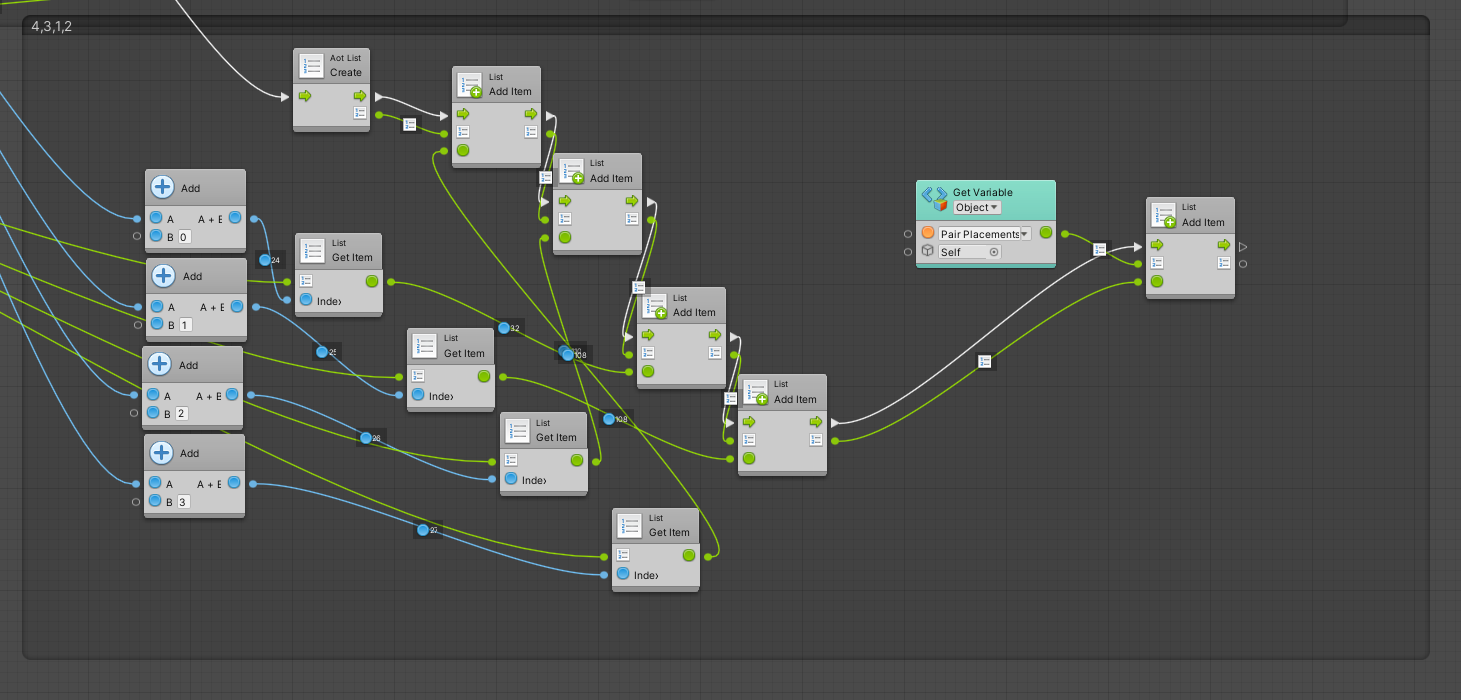
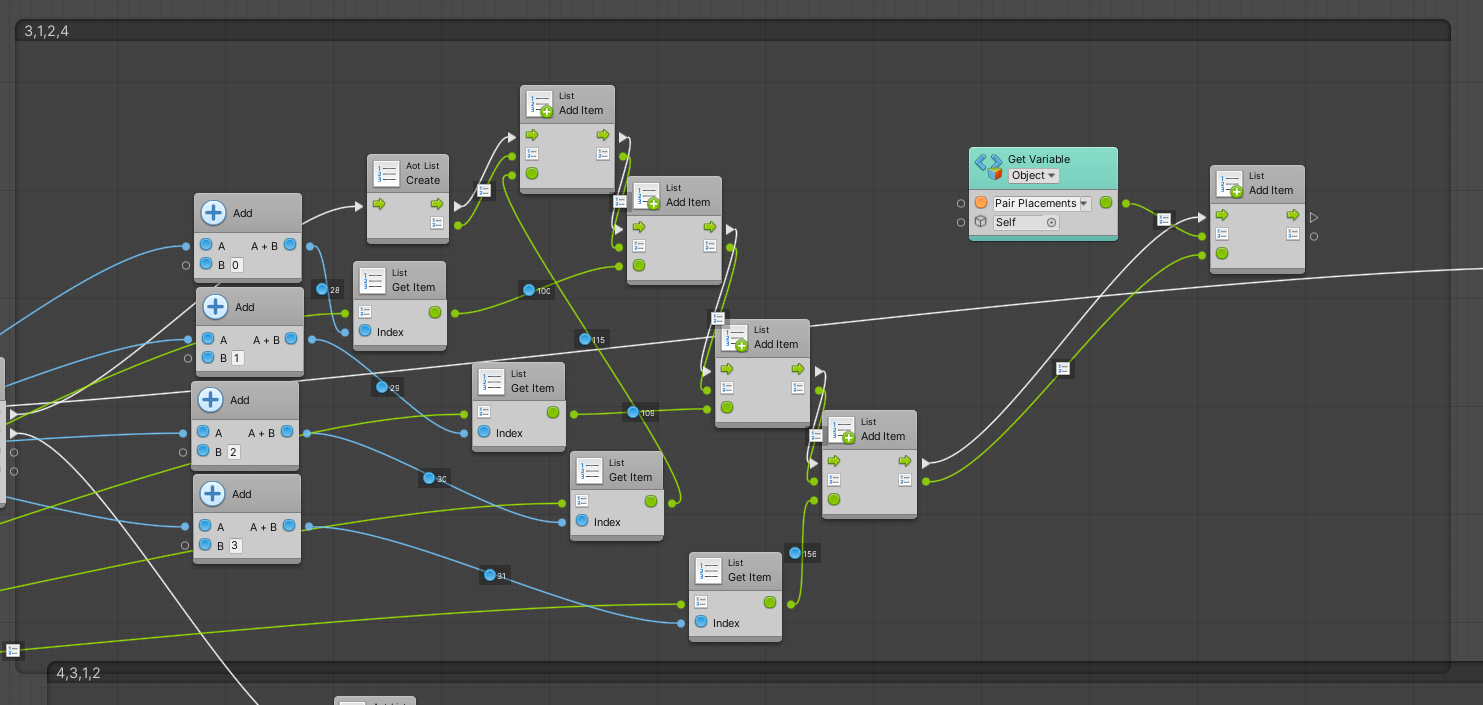
Next, the entire thing goes through a loop. The loop increases by four (and for those unaware, lists start at 0 in programming) like 0,3,7,11 and during each jump the number, +1, +2 and +3 of the list number is used as what number item to check in the character list. That is taken and added to a list.
*Simply showing as explained above*
Another Super Unit is used now. However, each character is turned into the ASCII value representation of itself and turned into a new list.
Now that we have left both of those Super Units, we are looking at the toggle value option. Essentially we are trying to reorder and organize the list of ASCII characters in a way that can be undone later.
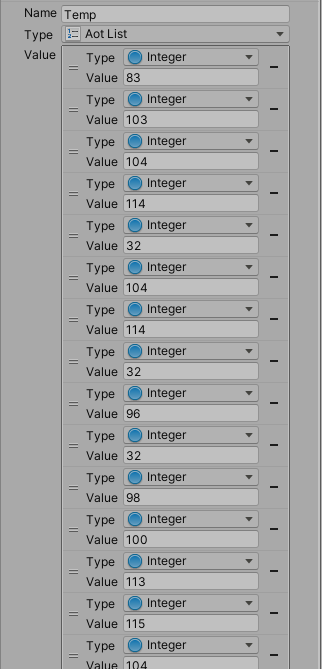
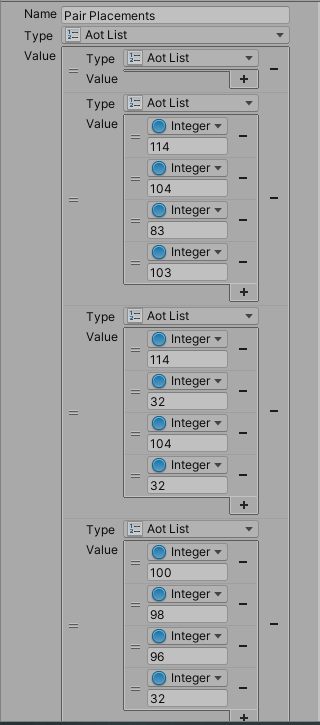
Within these two, the variables switch between organizing the ASCII character values to groups of four and to 3,1,2,4 and 4,3,12. This will be expanded on later for more organizing patterns. However, this system will next add the values of IV and Password together before adding, subtracting, multiplying and dividing to each value in the list to obfuscate it.
Now, this has to be done 20 times with being able to undo it with the proper variables. I also want to make the system more advanced later by obfuscating the system further at this stage. I do not feel it is enough yet.
-
How And Why Does KGE Work?
11/04/2021 at 19:09 • 0 commentsEncryption
- Generate 2 IVs and 2 Passwords
- Generate Math Modules w Quadratic Function (v1.2)
- Get User String
- Split User String
- Byte Substitution
- Obfuscate
- Split Results
- Switch Pair Placements
- Obfuscate
- Repeat 7-9 20 times
- Turn Results From All Rounds Into List Of ASCII IDs VIA Password/IV Based Polynomial Equation (v1.2)
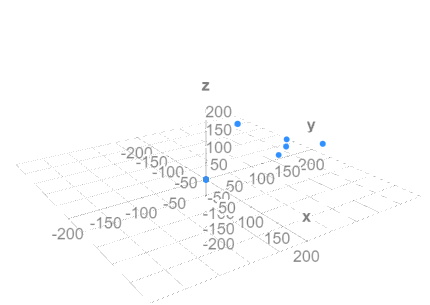
- Put All Points Into Trios (X,Y,Z) And Order Using Artificial Sequencing Order (1, 2, 3 is now 11, 24, 50) (v1.2)
- Use Hyperboloids Generated Using Both IVs As Compression References (v1.2)
- Add Dummy Points Using IVs (v1.2)
For reference, v1.2 is when most of this really is done! V 1.0 and 1.1 are viability tests!
Decryption
- Generate Math Module
- Remove Dummy Points Using IVs In Equation
- Input IVs To Hyperboloid Equation And Calculate Original Points
- Get Artificial Sequencing Order And Organize Points
- Turn IVs and Passwords to Polynomial Equation To ASCII IDs and Turn Variables To Characters
- Use IVs And Password to Unobfuscate
- Switch Pair Placement
- Concat Pairs To Single String
- Repeat 6-8 20 times
- Use IVs and Passwords to Unobfuscate
- Generate Byte Substitution Chart VIA Password+IVs
- Get String From 10 and Decrypt
Equations Used
To be listed later
There are many things that KGE does which makes it hard for even quantum computers to decrypt the password without the proper information. Computers are able to decrypt data because what they commonly do is run over every possible combination. Quantum computers can go over more combinations at an extremely fast pace compared to standard computers. However, KGE creates so many variables (IV, IVII, Password, Password II, Math Module, Dummy Points, Etc.) the amount of possibilities possible not only make it super hard for a computer to churn out all of the pieces to make sense together but there are multiple possibilities with one possibility, making the Quantum computer less capable of telling if a certain password out of a range is correct.
Biggest Problem:
- The Math Module System still isn't completely solid, as in While 1+1 = E, E-1 might not be 1. I want to change the Math Module Equation to switch the way it works so that it makes more sense at the theoretical level.
-
How Does KGE Work? (With Example) (OLD/OUTDATED)
11/01/2021 at 14:54 • 0 commentsThis is an overview of the layout in which KGE works.
- Get User String (Round 0)
- Split String Into Pairs
- If Not Enough Then Add Specially Made Character Which Is Deleted During Decryption
- Use Byte Substitution
- Switch User Strings To IDs and Find Replacement Term For Each Key
- To Find Replacements For Each Key, Use Cipher w=x^n+(y*n^2)/Y, where w is the first character to the new key, x is the first old character key, y is the second old character key and n is the second new character key, obtained from n=(round*y/x)^2, where the round is 100 at 0 and 1 at Round One, 2 at Round 2, etc. N is then divided by 220 (Cipher Only Allows 33-126, 128-255)
- This Equation Will Likely Be Changed
- Always Round To Zero
- Switch Pair Placement
- Get IV I if Round is 0 or Even and IV II if Round Is Odd
- Split To Pairs
- Change Order By First Pair To Last, Last Pair To Third and Fourth Pair To 6th, Then Flip All Characters For Next Loop
- Turn To IDs and repeat 256*x until the ID is reached, always round
- Obfuscate (Start Of Round 1-20)
- Get First 5 ID Pairings, for each pair, add the pair second to it, subtract the pair third to it, divide the pair fourth to it and multiply the pair fifth/password pieces relative to it. Treat as if string loops twice (makes more sense in example). Reference by IDs, not actual text.
- Get Result From Obfuscation And Split
- Always split into threes and use special character when needed, Just Reference The Example
- Switch Pair Placement
- Get IV I if Round is 0 or Even and IV II if Round Is Odd
- Split To Pairs
- Change Order By First Pair To Last, Last Pair To Third and Fourth Pair To 6th, Then Flip All Characters For Next Loop
- Turn To IDs and repeat 256*x until the ID is reached, always round
- Obfuscate
- Get ID Pairings, for each pair, add the pair second to it, subtract the pair third to it, divide the pair fourth to it and multiply the pair fifth to it. Treat as if string loops twice (makes more sense in example). Reference by IDs, not actual text.
- Repeat Steps 2 then 6 - 8 20 Times (End Of Round 1-20)
- Turn End Result Into List of IDs In List (Start Of Round 21)
- Always in trios, if number is missing y/z value, use 0 and 0.
- Pair All Strings (Threes) And Graph All Points
- Find All Possible Paths Between All Points Given, Adding An Artificial Range
- Use First IV character at Round 20 as x asymptope, use First IV II character at Round 20 as y asymptope, use Last IV I Character at Round 20 as Domain Minimum and Last IV II Character at Round 20 As Range Minimum. Remove Domain and Range if needed.
- Get Intersection Points and Reference Degree Of “Father” Line Within Key
- Cipher All Reference Points Using IV I and II as well as Password I and II
- Add Dummy Points Using Parabolic Area And Cone Area Equation.
Example (Not Made To Fit Math IRL, Visual Example):
IV I and IV II
- mRxL6X3Rc2xWO1BNd3sY
- ihcqh4LMCWg0wDtPm05F
Password I and II
- Go Mets, Oh Yeah
- Get A Home Run, Baby
- “Sword Art Online”
- Sw or d_ Ar t_ On li ne
93
94
95
96
97
98
99
100
93
xx
xx
xx
xx
xx
xx
xx
xx
94
xx
xx
xx
xx
xx
xx
xx
xx
95
xx
xx
xx
xx
xx
xx
xx
4m
96
xx
xx
xx
xx
xx
xx
xx
xx
97
xx
xx
xx
xx
xx
xx
xx
xx
98
xx
xx
xx
xx
xx
xx
xx
xx
99
xx
xx
xx
xx
xx
xx
xx
xx
100
xx
xx
xx
xx
xx
xx
xx
xx
w=x^n+(y*n^2)/Y, n=(round*y/x)^2
X = 100
Y = 95
Round = 100
N = (100*95/100)^2
= 9025/220
=41
N=41
W=100^41+(95*41^2)/95
=15
(Create Better Equation, Do by 256 for special equation?)
4. xL6X3Rc2xWO1BNd3sYmR
xL6XsY3Rc2xWO1BNd3mR
xL6XsYc2xW3RO1BNd3mR
Rm3dNB1OR3Wx2cYsX6Lx
5.
IV Pair (ID)
Add
Subtract
Divide
Multiply
Multiply
mR
xL
6X
c2
3R
Password Piece
xL
6X
3R
xW
c2
Password Piece
6X
3R
c2
O1
xW
Password Piece
3R
c2
xW
BN
O1
Password Piece
c2
xW
O1
d3
BN
Password Piece
1pv7eeuc926
6. 1pv 7ee uc9 26-
7. mRxL6X3Rc2xWO1BNd3sY
xL6X3Rc2xWO1BNd3sYmR
xL6XsY3Rc2xWO1BNd3mR
xL6XsYc2xW3RO1BNd3mR
Rm3dNB1OR3Wx2cYsX6Lx (End Result)
8.
IV Pair (ID)
Add
Subtract
Divide
Multiply
Multiply
mR
xL
6X
c2
3R
Password Piece
xL
6X
3R
xW
c2
Password Piece
6X
3R
c2
O1
xW
Password Piece
3R
c2
xW
BN
O1
Password Piece
c2
xW
O1
d3
BN
Password Piece
9.
bwt1dj1WB6oXAUfAKOxL guL4bkjGw7IyONSgeTOX ZmcCirx9YMPHMPUkMMVw Cftq6hlcEcAUS1aBTDM8 jpU7brH3dc671ObDHg7m IFp3pxtIyEnvgNxu2XL2 psBgSD6QtGozZBWfiPjK icRm9zTfPz4kqshyhRyU sGnYb3VkCv7oaggnQsi1 Aw78vfDHgexHJzsBwMy7 Pshd5gHwU9bDskWd24AQ ADbA69aS15ZVdYjnFWpY VXVro3daBwd87QgvpVGR 7r1lA7DvPHKnJcolhben JjO8dwWmIUNLftzgnLyd 3jv8m5cHtdjei6GXHiKn KKGujZ4b4f7iugch4nX4 EkM2AxWnaggkJB4AEDsc v5orF35MB9UPm5ZoBusO jf0QA2IvNrquIxmr1Fjh
10. 98 119 116 49 100 106 49 87 66 54 111 88 65 85 102 65 75 79 120 76 10 103 117 76 52 98 107 106 71 119 55 73 121 79 78 83 103 101 84 79 88 10 90 109 99 67 105 114 120 57 89 77 80 72 77 80 85 107 77 77 86 119 10 67 102 116 113 54 104 108 99 69 99 65 85 83 49 97 66 84 68 77 56 10 106 112 85 55 98 114 72 51 100 99 54 55 49 79 98 68 72 103 55 109 10 73 70 112 51 112 120 116 73 121 69 110 118 103 78 120 117 50 88 76 50 10 112 115 66 103 83 68 54 81 116 71 111 122 90 66 87 102 105 80 106 75 10 105 99 82 109 57 122 84 102 80 122 52 107 113 115 104 121 104 82 121 85 10 115 71 110 89 98 51 86 107 67 118 55 111 97 103 103 110 81 115 105 49 10 65 119 55 56 118 102 68 72 103 101 120 72 74 122 115 66 119 77 121 55 10 80 115 104 100 53 103 72 119 85 57 98 68 115 107 87 100 50 52 65 81 10 65 68 98 65 54 57 97 83 49 53 90 86 100 89 106 110 70 87 112 89 10 86 88 86 114 111 51 100 97 66 119 100 56 55 81 103 118 112 86 71 82 10 55 114 49 108 65 55 68 118 80 72 75 110 74 99 111 108 104 98 101 110 10 74 106 79 56 100 119 87 109 73 85 78 76 102 116 122 103 110 76 121 100 10 51 106 118 56 109 53 99 72 116 100 106 101 105 54 71 88 72 105 75 110 10 75 75 71 117 106 90 52 98 52 102 55 105 117 103 99 104 52 110 88 52 10 69 107 77 50 65 120 87 110 97 103 103 107 74 66 52 65 69 68 115 99 10 118 53 111 114 70 51 53 77 66 57 85 80 109 53 90 111 66 117 115 79 10 106 102 48 81 65 50 73 118 78 114 113 117 73 120 109 114 49 70 106 104
11. ((6 Point Example)
There are more steps to be added but a Github Repository will soon be opened with an example made using Unity Bolt and a Python Pipeline!
-
Introduction: What is KGE and How Does It Work?
11/01/2021 at 12:46 • 0 commentsKGE (Or Kinda Good Encryption) is an experimental encryption system designed to help with encrypting against Quantum Computer and Computer Farms. To understand how this all works, let's say you're sending a message to your friends Dave and John.
You, Dave and John are absolutely cracked at Apex Legends but they continuously get 1k less damage to you so you decide to tell them to switch to a new legend before a tournament begins.
If you use a Cipher such as AES, the data is properly obfuscated using a Password and IV and is sent to Dave and John, who can use a password and IV to decipher the message you sent, which explains that a Revenant, Pathfinder and Ash team (or The Metal Men) is superior due to Dave's ability to take good sniper shots but needing to change position every minute or so to reach higher ground and John's ability to hunt then push teams really hard for short periods of time.
However, your nemesis Matthew wants to find out your secret plan so that he may sabotage you in a long Twitter rant saying that those three legends are broken and should be banned on competitions. He somehow intercepts the message you sent and gets the ciphertext as well as the IV (which is usually not bothered with being too protected). He plugs it into his quantum computer and starts churning numbers, needing the password to decrypt the message.
Does the quantum computer send a qubit to the server, representing every possible password?
No, the internet can't send qubits (yet) and even then, developers should be smarter than to allow qubits for a login system.
Does the quantum computer compile a huge list of possible passwords and allow you to press a collapse to correct option?
Not that simple my friend.
Instead, what the password does is allow for more answers to be tested at a faster pace. It uses algorithms such as Shor's or Grover's Equation to basically increase the possibility of an answer at either an exponential or quadratic rise. if a standard computer took 10 milliseconds to try a password and there were 16 characters with One Trillion Possibilities, it would take at least 3,168,876 years to try every possible password, which is longer than Matthew's lifespan. However, a Quantum Computer allows this to be done in much less time, taking what may be a few days compared to the alternative. This gives Matthew the power to try every single possible password in just a matter of days.
What KGE attempts to do is increase in the number of possible answers and combinations to the point that attempting to use any sort of decryption system seems pointless.
In extremely bare terms (which are expanded on the Encryption Steps Post), an IV and IV II is randomly generated, while two passwords are made from the user. The result is turned into a group of points, with details from the IV being used to create several points and ranges on a 3D graph. These points then are added into a third IV, which requires the first and second IV and the first and second password to use. This is used to tell the decryption process which points to look at and in which order. What makes this better is the fact that this does snot use conventional math. As an example, while 1+1 may be 2, the system may decide that 1+1=@, which is better explained within the next log.
This adds in many more variables not present before and even if you were to use a Quantum Computer to attempt to find the password, there are many more things that you must account for now such as how the basic math system works and what points on the graph is real/fake. Also due to the high placement of numbers and special characters there are many more combinations compared to a regular system.
Now, when Matthew decides to attempt a decryption using the Quantum Computer, not only does he have to go through what is a much higher number of possible combinations, he also has to get all possible math modules following the basic laws of mathematics and go through each one with each possibility to see if it matches. Finally, he has to determine which points of combinations are real and fake to get the value of Round 20. This makes Encryption borderline impossible for standard computers to decipher in our lifetime and (hopefully) very hard for quantum computers to decrypt.
 WalkerDev
WalkerDev