
The Start
Our DC25 project started immediately after DC24. On the car ride home we started brainstorming bigger and better ideas for the badge. Many were rejected but after the response we got with our first badge, we were motivated to do the next time. We added two new members, @bitstr3m and @hyr0n1 to the team as well bringing our member count up to five.
After some discussion and false starts we determined our high level goals were to ditch Arduino, pay for assembly, produce a lot more badges, and improve badge to badge comms. Our first decision was on an MCU. After some encouragement from @rushan of DC801, we selected the BMD-300. This became the core of the badge and would be our development environment for the next 9 months.
The Hardware
BMD-300
We can’t say enough about how great this little module is. Based on the Nordic NRF52, it gave us plenty of head room flash-wise (an issue in our DC24 badge) and in ram to do everything we needed. DMA was simple and once we had it tuned properly the bling animations on the display looked silky smooth.
TFT Display
Without a flashy screen what good is bling? We did a group buy with DC801 on the Crystalfontz CFAF128128B. This is a 24-bit 128x128 TFT display with single backlight that can operate in 4-wire SPI mode. The BMD-300 is limited to an 8mhz SPI bus but through the blast processing magic of DMA our custom driver and graphics library netted us about 24 FPS.
LEDs
Let’s just put this out there, we hate WS2812B A.K.A. Neopixels. Never again. Sadly we had to fall back to these during prototyping due to our original choice, APA102 being unable to handle lead-free solder profiles. Next year we will work on something completely new for LEDs. On a high note, our custom WS2812B driver uses a SPI bus with DMA to communicate with the LEDs. Hackers gonna hack.
Voltage Regulator
Early in design we selected the PAM2301 from Diodes Inc. Very simple design, fixed voltage, and very reliable during prototyping. But this little part caused a lot of drama. Just as we placed the order for the first 396 badges, Mouser and Digikey got low on stock. We immediately bought all 450 we could find on Octopart and consigned them to Macrofab. Crisis averted. Then we decided to add another 100 badges and PAM2301 is now out of stock with a 6 week lead time 5 weeks before DEF CON. After plenty of datasheet reading we found the MCP1603LT from Microchip which only differed in the current rating, we directed Macrofab to utilize these on the white badges.
The Firmware
With the Nordic Softdevice S132 as our base, we continued by rolling our remaining OS and features. Nearly 11k lines of code. Here are the features we threw together.
Activation
We wanted to keep features secret until DEF CON, even more so we couldn't let the Kickstarter backers gain too much of an unfair advantage weeks ahead of time. To curb this, our badge leveraged a code system for unlocks and with that we implemented an activation code "RHAC6+7X” The instructions were simple: Scroll down the main menu to the “A” icon.
Bling
Blinky LEDs and animations galore. Just so there’s no confusion our definition of bling includes an animation displayed on the screen alongside an LED blink mode. With their powers combined...it is Bling. The main bling menu has modes devoted to our f1l7hy 400lb h4ck3r ph1l4n7hr0p157 Kickstarter backers, credits thanking everyone who supported us in this endeavor, as well as dozens of hand crafted blinkies to make u the center of attention. In addition, custom mode comes with 94 animations : 30 LED patterns, for 2,820 different bling modes. If that isn’t enough, import your own via Bring Your Own Bling (BYOB) by reading the log on our hackaday page.
Games
Our single player games included a clone of Ski Free, clone of Flappy, and a CHIP8/SCHIP Emulator supporting 64+ public domain ROMS (included)! Be sure to read the instructions before launching the game. We have no speaker, so instead of beeps we blink LEDs matching the foreground of the game color!
Nearby
Lists all nearby badges as well as IoT enabled Medea vodka bottles...Hack all the b00z3 drink all the things! (Yes it does hack bottles of booze)
TCL-ish
A scripting language we created (30+ commands) so you can control the hardware on the badge without recompiling. A full API is available on our hackaday page. Just throw together your own script and drop on the SD card.
Botnet

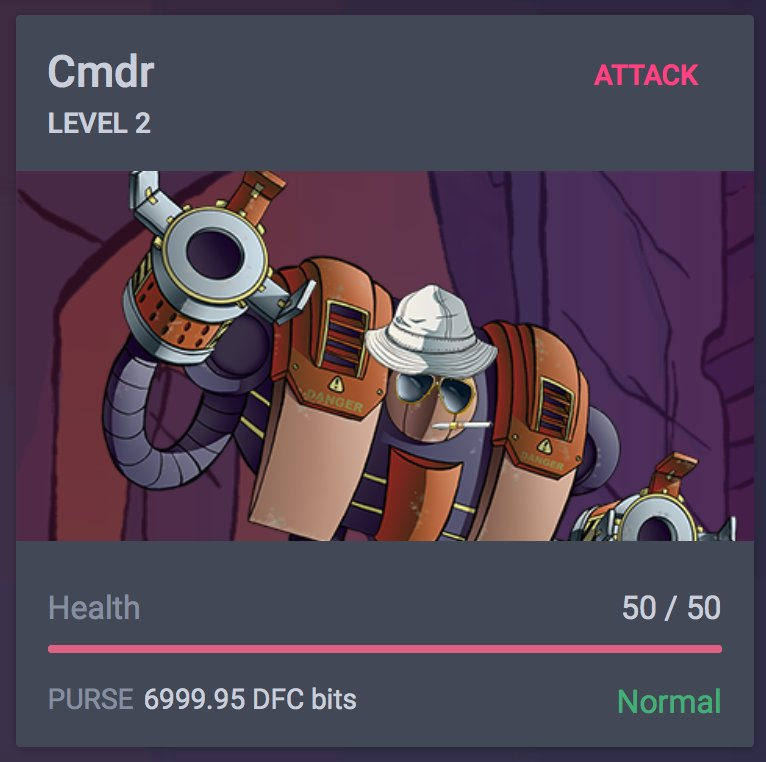
Our major feature that we held in secret until the week of DEF CON. The botnet game turned out to be extremely popular. This is from the insert card, in how we described it:
Congratulations you are the new grey hat sys admin of your very own badge! You must protect it from all the l337 hax0rs out there. To do this, it will cost you points.
*You earn points based on how many services you have accessible.
*You do NOT earn points for a service if it is blocked or disabled.
*You can spend points on enabling, disabling, and patching services.
*You can spend points on modifying firewall rules (allow/deny).
*You can spend points on research and upgrade of exploits.
*You earn experience (XP) when you successfully attack another badge. To attack another badge you must use an exploit payload on a service they have running, which isn’t blocked by the firewall.
*If you earn enough XP you will level up and perhaps unlock things…
There was an Android Smartphone App as well to provide console access to the badge, for lulz and to partake in BOTNET.
Perhaps you don’t like graphical user interfaces. Some of the botnet can be managed via terminal over bluetooth. Head to the Google Play store, search for “AND!XOR” and use the companion app. If you use iOS, the Nordic nRF Toolbox is “compatible” with its BLE UART applet. However it is verbose and buggy, you may have to force close. We recommend making friends with an Android user, find one and buy them a beer…
The terminal can be used for many lulz, utility functions on the badge, and modification of botnet services and firewall rules.
However, the badges were pushed out early before they could be fully secured... (CVE-AND!XOR-1337) All badges have a default root password. Sys-admins are advised to determine what that password is and change it ASAP! Otherwise malicious unauthorized users may log into your badge and modify services or firewall settings for the benefit of exploitation ;)
Oh yeah, we said it was a botnet. The hackers at AND!XOR have full command and control over all badges in our ad-hoc BLE mesh badge-net. We may send lulz, gifts, or unleash havoc. Depends on our level of drunkenness...
Sales
DEF CON sales were a circus. Going into DEF CON we decided to do guerilla sales around Caesars to give people and experience of being at the right place and right time. Sometimes solo, sometimes teaming up with @MrRobotBadge who also enjoys the trolling of peoples. This encouraged social engineering, got us a free glass of scotch, and a lot surprised buyers - “Oh you’re the AND!XOR guys! Got any badges?”. It also resulted in six hackers going into the pool...for 5 badges...in their clothes... and getting their daily shower – you’re welcome DEF CON. Just doing our part to assist with enforcement of the 3-2-1 mantra. @FTAlligator and Dennis Leeroye deserve a round just for their amazing swim race.

While we thought this would be a pinnacle of fun and lulz, sadly this tactic seemed to encourage stalkers when they couldn’t get badges. We were followed on several occasions, had knocks at the door of our room while trying to have some down time, and some other issues. We will handle things a bit differently next year to discourage this behavior. That being said, having so many guerrilla sales took away from our DEF CON experience.
Special thanks to Car Hacking Village and the goons for hosting us on Friday for our large sale. Crowd control was organized and we were able to avoid a total mob scene. Also big thank you to Hacker Warehouse for hosting us twice to troubleshoot and talk to badge holders.
Sponsors and Backers
A major change from our DC24 badge was financial help. This let us go so much bigger than before. Not only did our quantity nearly triple from 175 to 503 but the BOM more than tripled and prototyping costs grew as well. Big thank you to Phobos Group, Rigado, Boosters, Kickstarters, and two anonymous sponsors. We wouldn’t have been able to afford the project this year without your help.
Failures
What’s a DEF CON electronic badge without failures? In total we ordered 503 badges. 488 of those past our testing and were packaged up for sale, trade, or gifts. We were able to fix a good number of badges at the Hacker Warehouse booth and return them to action, but also swapped roughly 20 bad badges for good badges. At the end of the day we lost another 9 at DEF CON that could not be repaired bringing our total up to 24 failures or 4.8%. Our DC24 badge failure rate was roughly 20%, so a vast improvement. Good news though regarding some of the failed hardware, XenoGirl (Lisa Weeks) is working a project to upcycle some of them in to blinged out hand bags! Fashion Tech PCB Bling FTW!!!
BMD-300
The most common failure during production can be traced back to the BMD-300. We were unable to fix any but the best we can tell is solder did not reflow properly and caused a short somewhere under the module. Upon further inspection, the tolerances between traces and the pads underneath could have been better.
TFT
Given that the TFT ribbon bulges out slightly from the rear of the badge, we assumed the ribbons would catch and tear. We also assumed the displays would be damaged or cracked by bouncing around on peoples’ chests. For this reason we bought a lot of extra displays. In the end we didn’t have a single failure.
Buttons
At DEF CON buttons were the highest failure. Turns out giving hackers a badge with surface mount buttons is not a great idea. A good number sheered off but easy to replace with a steady hand. Only issue here is Macrofab’s buttons are white and we ended up with black. So there’s a slight mismatch.
MicroSD
Another common failure, but we anticipated this. We lost about a dozen SD cards during packaging and DEF CON just due to corruption. From personal experience we expected this and bought 600 MicroSD cards in anticipation. Additionally, we posted the SD Image to github early so badge owners could replace the card themselves.
Voltage Regulator
This one surprised us. The Microchip replacement voltage regulators on the white badges turned out to be a high failure item. As best we can tell a short causes them to let out magic smoke. Zapp spent most of his mornings replacing with spare PAM2301s. Saturday he replaced all white badges still on hand with PAM2301s to avoid future failures. We only saw one PAM2301 fail at DEF CON which is closer to what we expected.
Badge to Badge Comms
A little advertised feature between badge makers is a badge to badge comms spec that each group implemented. The spec based on BLE GAP Advertisements. While simple, it allows our badges to recognize each other amongst all the 2.4ghz traffic at DEF CON. In the AND!XOR badge, we had code to recognize Queercon, Crypto Privacy Village, DC801, and DC503. When a badge is detected a special hello animation is played for that group. During DEF CON we observed DC801 and our badge saying hello but did not get a chance to test with the other groups. We plan to build on the spec next year.
Botnet
The botnet game turned out to be extremely popular. It had several bugs when attacking other players but overall we received positive feedback from badge owners.
Command & Control (C2)
The C2 feature was intended to give the master (orange) badges command and control over all human badges by sending worms through the BLE network. At BsidesLV this feature worked perfectly. Command sequence numbers based on common time reference allowed us to run various bling and unlock avatars as planned. By the time we got to DEF CON the common time reference overflowed the 16-bit integer we were using to store it, oops. In the final firmware we fixed the overflow and randomized the C2 special bytes and regained control.
Then DC801 came along. We aren’t sure exactly how this happened, but it appears DC801 found our special bytes or were replaying advertisements with some fuzzing or overflow fix was still buggy. @miketweaver (DC801) may have even been exploiting our time sync somehow... Either way we struggled the rest of DEF CON to maintain C2 of the badges. Props to DC801 if they pulled this off. It was fun to talk about how we made a botnet out of conference badges, and oddly more fun to admit we lost control of it.
In conclusion…
This year we wanted to go big. We spent nearly a full year planning for the four days of DEF CON and managed to deliver on our original goals. Failure rates overall were much lower, we left Arduino in the dust with 11k SLOC of our own C code, and RF worked. More importantly, we reached out to the other badge makers and we worked together to get BLE interactivity between the projects, puzzles which spanned hardware, software, crypto, IoT, and wireless, even tie-ins with Coindroids. We hope in some way this badge helped in sparking conversations and getting people to visit villages they maybe hadn’t before, learn something new, or just have fun playing the BOTNET game with others. Meet people and make new friends. We were also able to auction a badge off and raise $2100, $1100 was given to the EFF and the rest we used to donate b00z3 across various DC parties. We missed you @lo57 , there's a drink waiting for ya at DC26! Big thank you to everyone at DEF CON this year, this made all the hours worth it and can’t wait to do the next badge.

Next Year
There’s still plenty to learn so we’re doing this again. We are in the idea gathering phase and starting with a blank sheet. We know LEDs will get a lot of attention this year as well as our manufacturing process to reduce failures and give us more time to enjoy DEF CON. In the next month or so we will start ordering evaluation kits, kick off artwork, and reach out to potential sponsors. #badgelife never ends, but we wouldn’t have it any other way.
DC25 Badge Spoilers: Easter Eggs, and Unlocks
Yeah, don’t read this section if you haven’t finished the puzzles on the badge. You could just dig through the source code and gerbers, but we do realize that many of you are lazy. If you are curious about your unlock status, just hit back from the main menu. The screen will display a schematic of the badge and each LED will light up for every unlock achieved, 15 in total. Some of the unlocks required physical proximity within some of the BLE Beacons, use an ubertooth or Nordic nRF Toolbox to broadcast ;)
Primary Unlocks
# | Mask | Name | Description | Unlock Method | Feature(s) unlocked |
0 | 0x0001 | Master | Master badge Unlock | Master badge connects to human to grant | Rager Mode |
1 | 0x0002 | Whiskey Pirates | Decrypt a code using WP VHS Badge | EPYPFMSK | Zero Wing Avatar |
2 | 0x0004 | CPV Unlock | Unlocked when near beacon A placed at CPV | Unlocked when near beacon placed at CPV. CORRECTION: It was left in Whintey's pocket during the con...so this is also known as the Whitney unlock. lulz | Major Lazer Bling |
3 | 0x0008 | Terminal HeMan | Unlocks HeMan Whats Up Bling | From BLE Terminal, type “Hey.” Complete the terminal chat of USER: HeyBADGE: Hey STUD! LOL j/k USER: Hey BADGE: What's going on?? ;) USER: Not much. Brb. | HeMan WhatsUp Bling |
4 | 0x0010 | Terminal Datetime | You hack too much time | From BLE Terminal, type “datetime” Change date < 1/1/1970 | Hackerman Bling |
5 | 0x0020 | Terminal Defrag | Maintenance Bling | From BLE Terminal, Escalate privleges and login as Scruffy Type “defrag” | Defrag Bling |
6 | 0x0040 | C2 Mass Unlock | Use botnet and C2 to mass unlock badges | Master badge enables mode, worm takes it from there | Zapp Avatar |
7 | 0x0080 | TCL unlock | Fix a TCL script to reveal a code | Mount that SD card and edit the file. Y_AN:LRN | Owl bling |
8 | 0x0100 | Base64 on back of badge leads to Twitter | https://twitter.com/mnccoenaqakbe has a pastepin link. Contains a file with: 3TNXFBBN | Illusion Bling | |
9 | 0x0200 | Seekrit Resistor | Set mask to 1 if GPIO is held low on start | Seekrit footprint on back with solder bridge or R | Trololol Bling |
10 | 0x0400 | Matt Damon | Simple unlock | DAMON | Matt Damon Bling |
11 | 0x0800 | CHIP8 #2 | Find random CHIP8 ROM that displays code | It’s one of the Pong Roms 7CA3FF1D (Yes Hyr0n coded up roms in an archaic ch8 language for your hacking pleasure) | Fry Avatar |
12 | 0x1000 | Scroll | Scroll beyond bottom of shouts | VN2D85FF | New Party Modes |
13 | 0x2000 | @securethisnow | Find Mr Bill (@securethisnow) whos beacon will unlock |
Beacon UUID | 5 levels and 1000 points. Mario animation? |
14 | 0x4000 | Business Card | Business card contains Base64 | YJ9XZHFA | More bender modes |
SD Card Unlock
There was an AES256 encrypted zip file on the SD Card, funstuff.7z. No you wont find a Weezer video on there, but there's just as good of stuff.
If you wanted to crack an ecrypted 7z file...
$ sudo apt-get install rarcrack
$ rarcrack --type 7z --threads 12 funstuff.7z
// IT TAKES A WHILE TO CRACK UNLESS YOU USE YOUR GPU
// PASSWORD = 4Q$$
Lulz & Easter Eggs
Escalation of Privilege
Some of the unlocks required that you hack the badge through the terminal, to escalate privileges. This involved gaining access to the badge maintenance account (Scruffy), then digging through his shadow.backup file, to reveal the md5 of the root password. Scruffy is a horrible sys admin keeping his passwords in backup text files. We thought most people would have guessed the maintenance account password for scruffy (April did on day 0), but it appeared to be a puzzle the likes of which the world has never seen... so we released a hint:
Once you su to scruffy, one can finally “less shadow.backup”
#Backup for scruffy - root:ff24fefce7040369fd4fda33fd2d036d
Then you can finally escalate to root, which provided the ability to control the botnet from the console. Or more importantly, now that one knew the root password, they could backdoor into any badge which had not yet changed it and remotely modify their services and firewall settings <8
Coindroids
You know the skill-based blockchain game where droids run around attacking each other on-chain? That’s Coindroids. Their crypto game is rad. When we started talking about a way to get our two communities to to interact with one another, it came down to hiding a QR code on our badge while, in game Coindroids features, and Twitter to try and get them all to work together for the unlock. To find the QR code, go to our bling menu and play the Kickstarter Backer thank you credits. If you wait long enough until the credits have finished scrolling you will be flashed a QR code for about 300ms.
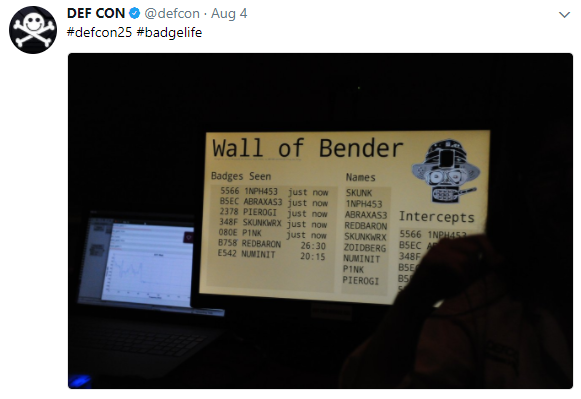
Wireless Village
So @abraxas3d & @MustBeArt created the Wall of Bender in the Wireless Village. It was a logger and display board for the badges. Three windows are displayed. A smaller window displays just the names and unique IDs of each and every badge advertisement received, in real time, even if they go by too fast to read. A bigger window displays the same information plus a time-since-last-heard indication, and smooth scrolls the entire stored list, after removing duplicates based on the BLE advertising address transmitted. In between, another smooth-scrolled window shows just the names received, regardless of which badge sent them. Very cool. They also brought some electronic RF wizardry device that spoofed badges at our backer meetup, tip of the hat you hackers!
 Hyr0n
Hyr0n
Discussions
Become a Hackaday.io Member
Create an account to leave a comment. Already have an account? Log In.
I loved these badges. They were so open and fun to mess around with.
You were curious what I was doing. It wasn't as exciting as I made it seem, as I was working on about a hundred other things at once this last defcon. I just followed you around for a good while, recorded a good bit of your traffic, and then replayed it randomly. I was also messing around with the bits randomly, and I guess one of them hit your timesync somehow. I had no idea what I was doing, only that when I did, it caused funny stuff to happen. I believe I was the only one messing around with it, as I'm sure someone much smarter than I could have done a lot more.
Thanks for making such cool badges! This was my first foray into BLE and I haven't slowed down since. Your badge made for great inspiration to learn more and do more hacking in the BLE realm. Hats off to you and the team for making defcon that much more exciting.
Are you sure? yes | no
Aww thanks Mike! Yes you did twiddle our magic bits the right way ;) But that was the point, make it open at a hacker conference and see what mischief people get into.
Are you sure? yes | no
Great write-up. I had a ton of fun with the badge this year and am happy to learn of the stuff I never figured out.
Are you sure? yes | no
<8 Thanks Mike! BTW that just reminded me to update the post and add the SD card unlock...
Are you sure? yes | no
Ha! I tried off and on to crack that but never got there. I have a very poor machine for cracking but it was still fun.
Are you sure? yes | no