WPS PBC :
This is a feature of WiFi access-point which allows users to connect by simply pressing the button on the access-point.
But the problem with this method is that access-point does not have any control over which device gets the connection and 120 sec window makes it even worst.
VULNERABILITY:
If we have a device which always keep looking for access-point to have a active WPS session and try to connect to it before the intended device does.
HACK:
So we need a wifi device which should be small, cheep, low power, easy to get
Am I describing the ESP8266?
PROJECT:
IMAGINE!.. a ESP sticked underneath the table or chair with some chewing gum.
We have a ESP8266 running on a coin cell which wake up from sleep and does it's work and sleep again for 100 sec. once we got the connection we can mail the SSID and PASSWORD to someone who needs it (may be YOU). and disconnect before any one gets to know about it. :)
PROBLEMS: ( for HACKADAY coin cell challenge)
The esp needs around 80mA when running and the coman CR2032 (50mA max) can not provide that much ofcource there are other cells which can do that or just couple of CR2032 in parallel but then it violets the rules of "coin cell challenge"
my solution was to add a huge cap in circuit but no success ether
(all of this because i dint had other coin cell with me)
NEED HELP:
Great thing is the ESP supports the WPS PBC method but once you got connected there is currently no way to get the password out (at least i don't know)
good thing is that it should not be impossible because 'WINDOWS' can do that. so.......
THIS IS ILLEGAL
A little bit of Background:
As many of you already know that wifi access-point have these feature called "wifi protected setup" or simply WPS. The wps enabled system is 100% hack-able.
But what i did't know that there is actually two types of WPS systems
so called WPS PIN method and WPS PBC method which both of them work differently. Which i thought was same for quite a long time.
A couple of month back i was running 'wifite' on a mobile hotspot and no luck no matter how many or how long i tried. which was weird because I have successfully run a pixie dust attack on the successor of that device. well normally this happens the other way around.
And i tried WPA brute force also as most of time fail.
[at this time HACKADAY coin cell challenge was live]
Luckily one of my friend had this hotspot and i borowed it from him. and ofcourse i run the attack again, failed this time too
then i took a shortcut and tried to find WPS PIN in the settings page of that hotspot but i couldn't able to find the pin there obviously because there was no pin.
but the device itself had a button saying WPS, and which is also working. where is the pin then?
Then i realized that it is a WPS PBC not a WPS PIN.
 Sagar Naik
Sagar Naik


 Raymond
Raymond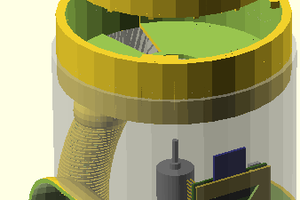
 bsutton
bsutton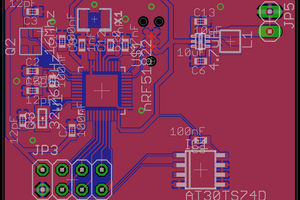
 Tim Wilkinson
Tim Wilkinson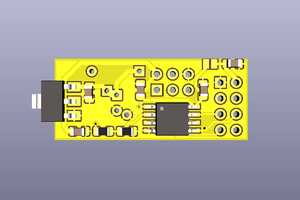
 Arya
Arya
How does it can be done in ESP8266 NodeMCU board?