Embedded HTTP server
The embedded HTTP server comes along with the following JSON formatted status pages (cnq-pico-ip is a placeholder for the real IP address):
http://cnq-pico-ip/getStatus.cnq - provides you with information about network/MQTT status, uptime, current time, firmware version
http://cnq-pico-ip/getSensors.cnq - outputs current sensor data (like temperature, rel. humidity, barometric pressure) along with a timestamp, RSSI, and battery status (in millivolts) for each sensor that sent radio messages to this gateway
The HTTP server runs on its own core on the RP2040 chip so it should work no matter what the other core is doing.
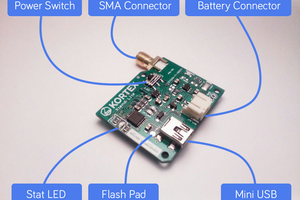
LEDs
The Rasperry Pico LED shows the MQTT connection status. It will turn green when an MQTT connection has been successfully established and turn off when the connection seems broken or when you unplug the network cable.
The TX LED will blink whenever a radio message is sent (e.g. to acknowledge a message).
The RX LED will blink whenever a signal is detected that is above the noise floor. If the RX LED is blinking all the time or if it seems to be constantly turned on, then this indicates that there is an interference in the proximity of the device. This can be a television, loudspeaker, a computer, a monitor or some network device, etc. interfering with the 868 MHz radio. To resolve this, you need more distance between the Canique Pico Gateway and the interfering device.
Robust!
If you enter wrong network settings on the HTTP settings page, you won't be able to access the HTTP page again, because the network won't be connected, right?
There's a simple solution to prevent you from locking yourself out: Keep the black button pressed for a minimum of 3 seconds, and the Canique Pico Gateway will restore factory network settings (DHCP).
Power efficient!
The RP2040 chip is sleeping whenever possible to save power. It will wake up on radio messages, MQTT keepalive pings or messages, DHCP or DNS timers, network link changes, HTTP requests or button presses.
Fast!
The complete startup of Canique Pico Gateway after connecting it to a USB power supply took less than 5 seconds during a test! This included: DHCP IP address retrieval, time synchronization via SNTP, DNS lookups, establishing a secure TLSv1.2 connection using the TLS-ECDHE-ECDSA-WITH-AES-128-GCM-SHA256 cipher and an MQTT connection.
The TLS connection alone has been established in roughly 1.2 seconds during that test.
Secure!
The supported TLS ciphers are restricted to only a few good ones to keep the connection secure. In a future firmware version TLSv1.3 support will be added. Note, though, that the ciphers currently used are also part of TLSv1.3.
If you specify an IP address as MQTT server, no TLS will be used. A plain TCP connection will be established. This is e.g. useful if your MQTT server is in the same local network.
TLS Compatibility
The TLS connection has been tested successfully with Canique Cloud and HiveMQ Cloud (free version).
The Pico Gateway firmware contains these root certificates by default:
Let's Encrypt ISRG Root X1 (Root Certificate, RSA 4096 bits, valid until 2035)
Let's Encrypt ISRG Root X2 (ECDSA P-384, valid until 2040)
Datasheet
Power consumption: 0.7W
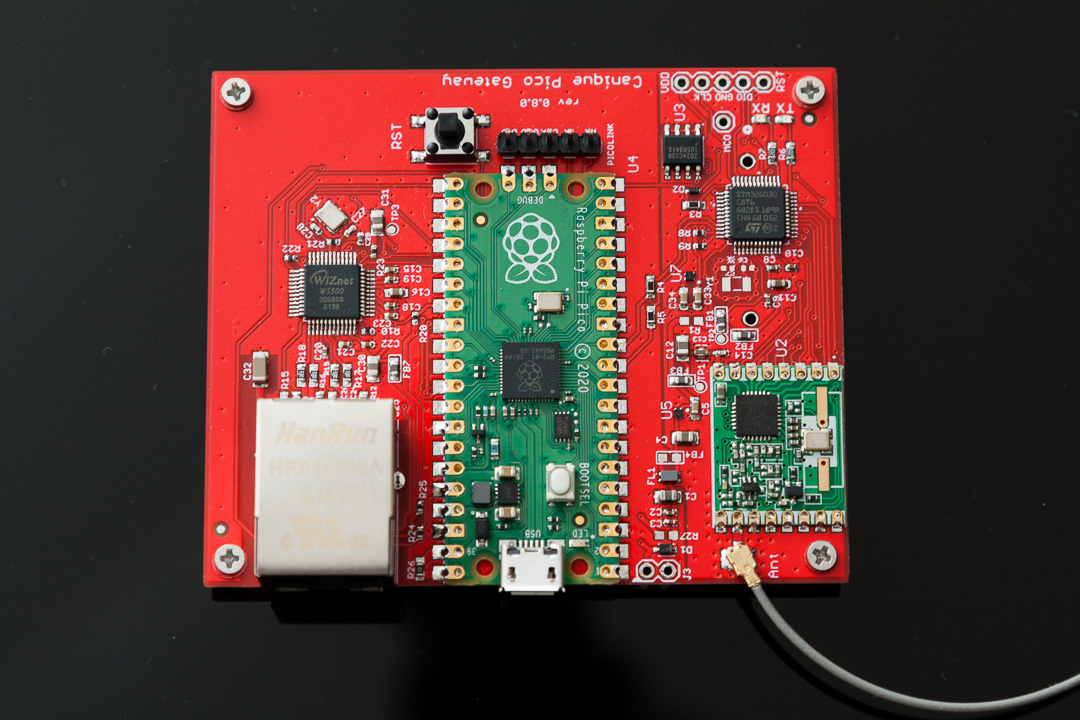
Interfaces
RJ45: used for DNS, DHCP, SNTP and TLSv1.2 connection to the MQTT server and for serving HTTP requests
USB for power supply and firmware updates
u.FL for 868 MHz antenna
Supported TLS versions: TLSv1.2
Supported TLS Ciphers:
TLS-ECDHE-ECDSA-WITH-AES-256-GCM-SHA384
TLS-ECDHE-ECDSA-WITH-AES-128-GCM-SHA256
TLS-ECDHE-RSA-WITH-AES-128-GCM-SHA256
Root certificates:
Let's Encrypt ISRG Root X1 (Root Certificate, RSA 4096 bits, valid until 2035)
Let's Encrypt ISRG Root X2 (ECDSA P-384, valid until 2040)
Supported MQTT version: 3.1.1
 canique
canique

 Amine Mehdi Mansouri
Amine Mehdi Mansouri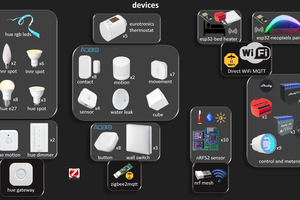
 Wassim
Wassim
 Ruslan
Ruslan
 Valent Turkovic
Valent Turkovic