FelinityVM is a new virtual machine designed with the following goals:
-Simple to implement
Simplicity can be a vague concept to specify, so to clarify what that means for this project: someone familiar with computer architectures should be able to code at least a rudimentary implementation inside of a week. Of course more advanced optimizations may take longer to research and implement, but from an operational standpoint, it should be that easy to create a new VM according to this specification from scratch. This helps not only to propogate the usage of the VM to embedded developers who are under tight time restrictions, but also helps prevent the many problems that come from the same code base being ported over and over. If the VM is simple enough to rewrite from scratch in a way that is integrated into your project and system design, why wouldn't you do that instead of taking a machine that was meant for another system and cramming it onto a new one, adding band-aid after band-aid until it finally works. Now there will be good implementations available for most major systems so reimplementing from scratch will not be the norm for most application developers, but having that as an option frees programmers from worrying about a particular implementation restricting what they can do with their application.
-Well documented
A lot of VMs or software in general these days is "code first document later," this project is more about creating a specification that can be easily implemented on any system than about a specific implementation. Although several reference implementations will be available along with implementations for most major architectures including X86_64, ARM, etc.
-Powerful yet small instruction set
The CISC instruction set used for this VM gives power back to the programmer making assembly writing intuitive and fun by having only a small number of instructions that can do more than most large instruction sets. I don't know how many people still write assembly for modern architectures, I'm sure there are quite a few, but personally I find it to be a rather tedius experience, and I'm sure I am not the only one. The reason for this is that people are not meant to write assembly most of the time, the architectures today are bloated full of niche operations and complex operand formats that are supposed to be optimization tools for the way that higher level languages need to generate assembly. But assembly can be made much easier and far more entertaining if the instruction sets are not geared toward compilers. Thats not to say that the FelinityVM instruction set does not take into account the work that compilers need to do or that compilers should not be written for the VM, but merely that it is designed so that those optimization tools are elegant features; core to the design rather than side features tacked on after-the-fact that add convolution to the rest of the architecture.
-Doesn't take away from native features
Most VMs like to abstract you from your native environment which is good because you want code to be portable, however sometimes you want to take control of specific elements of a native environment. The solution in other VMs such as Java is to write native code for that system, then write some more native code to act as an interface between the VM and the native code you just wrote thus creating messy layers of calls to do what you want. FelinityVM allows access to native memory, system calls, and even native processor registers all from within the VM. Furthermore, since these types of accesses are all primitives within the vm they are easily disabled when a sandboxed environment is needed. This gives FelinityVM the flexibility to behave as a sandboxed machine when running untrusted applications, as a microcontroller VM allowing the same code to run across all sorts of uController manufacturers with only minimal changes to runtime selection of registers, and as a full fledged bare-metal VM capable of implementing...
Read more » aaron
aaron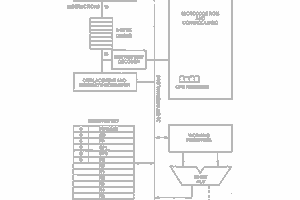
 Keith
Keith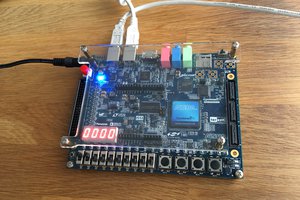
 ErwinM
ErwinM
 Yann Guidon / YGDES
Yann Guidon / YGDES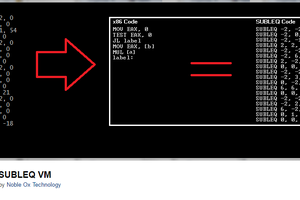
 agp.cooper
agp.cooper