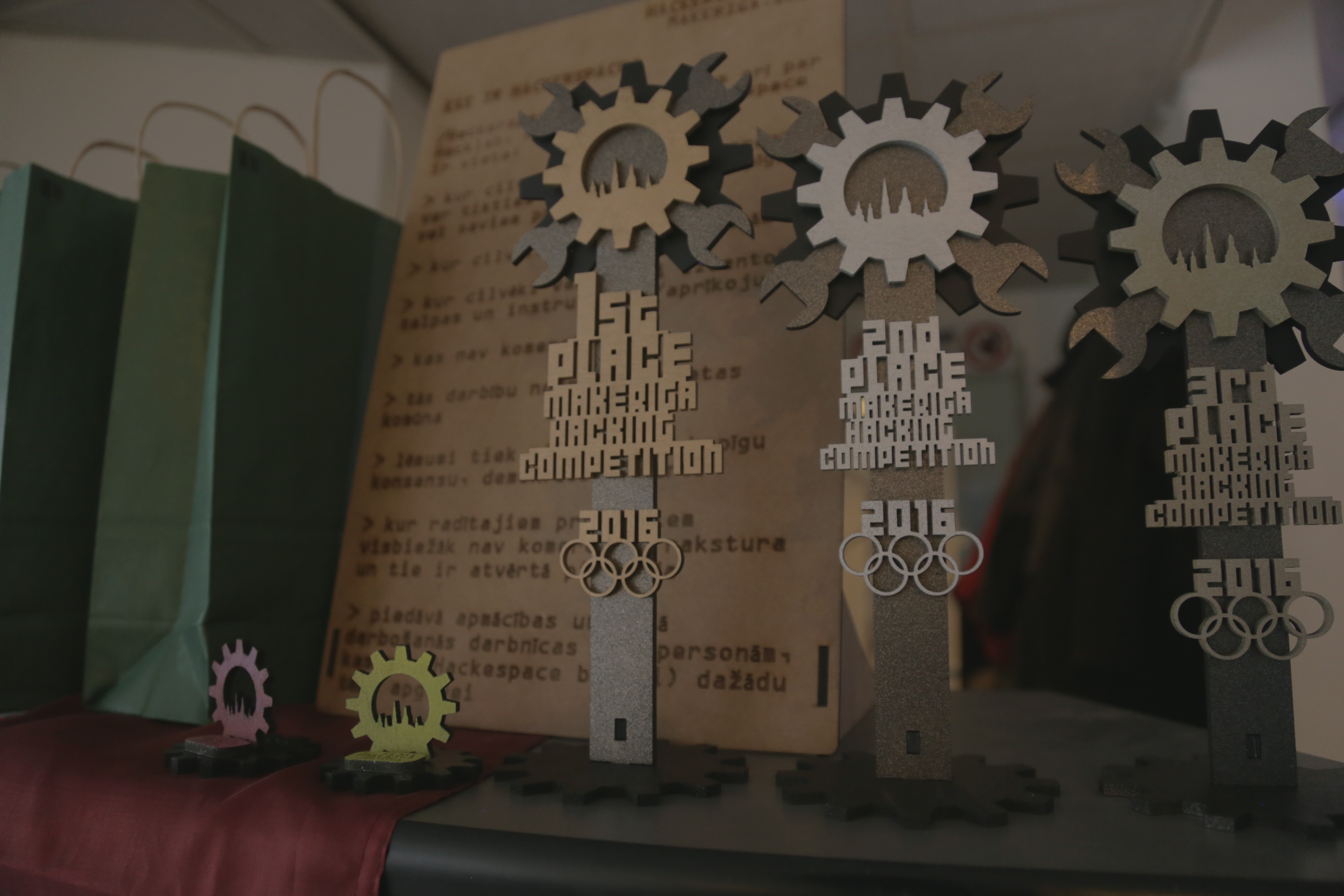
A year and a half ago, an event vaguely falling within the confines of the term "Hacking Olympics" was organized at the local hackerspace in Riga, Latvia. The event attracted give or take 15 people, everybody who attended and organised the said event had a lot of fun. It was determined to be repeated the following year.
This year the event was organised again and we just want to spill the beans and let you replicate the recipe on how to create an event that brings together the local community for an awesome, fun filled weekend. As opposed to the previous years' event we had attracted 38 participants and 32 challenges to solve. The previous year we had only 23 challenges IIRC.
The format seems to be working well and we suggest that every hackerspace around the world tries to organize one such event at least once a year. Depending on what the expected skill level of the attendees is- try and limit the number of relatively "simple" challenges or categorize the winners. It's pretty easy to organize if everyone pitches in a few hours of their life to make it happen.
To encourage the attendees to compete, try and get some cool prizes. This year we got some pretty cool wireless tech from Ubiquiti and gift cards from Ian and Jin from dangerousprototypes.com . Some other companies helped us as well, by keeping us fed or entertained.
Most likely every hackerspace can find a like minded company (or a manager in one) to give some cool stuff or service to win. It doesn't hurt to ask, you know?
What kind of challenges did we set up for the contestants?
- Lockpicking and solving wire&metal puzzles
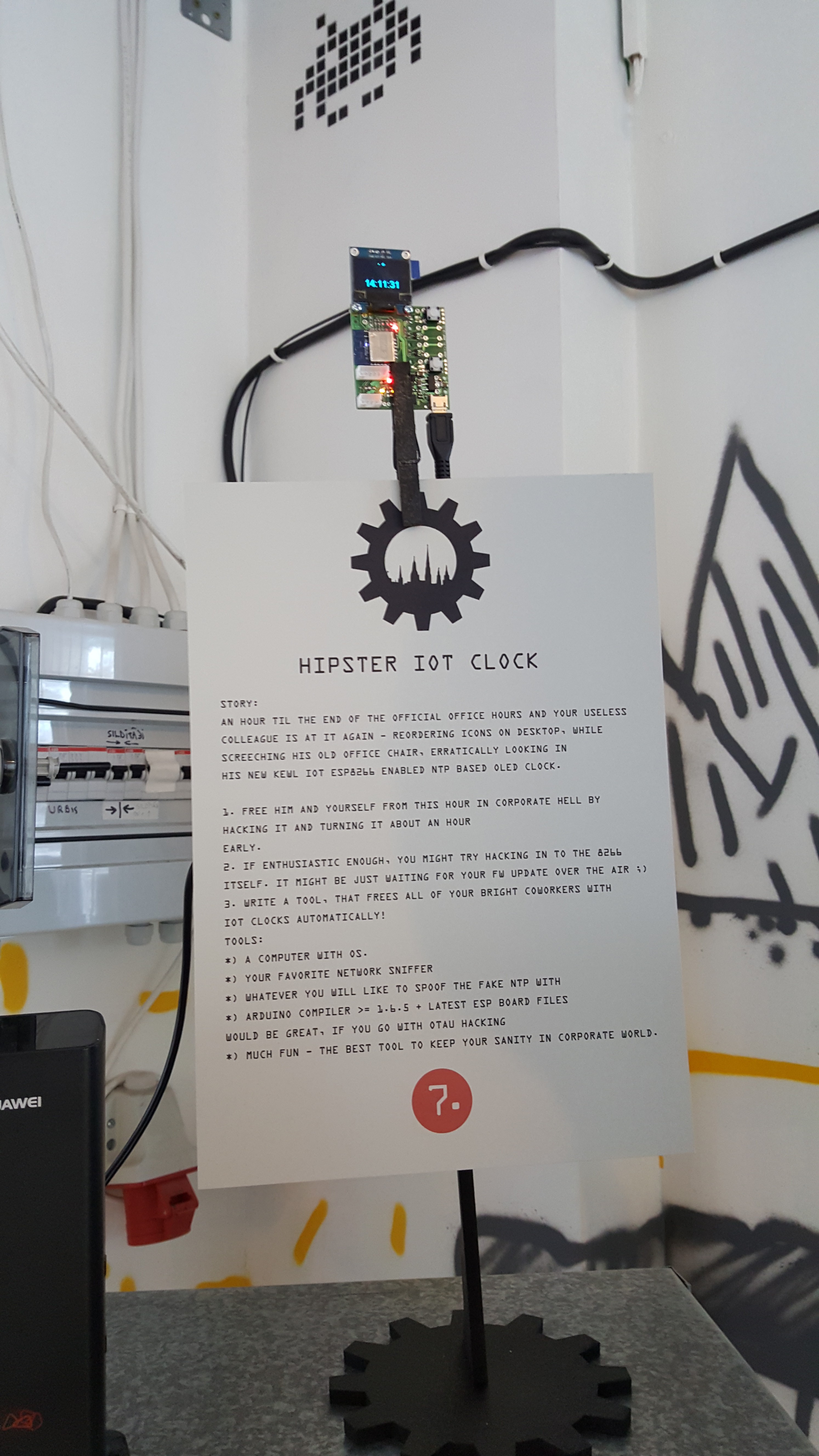
- Binary (.EXE and .JAR) cracking
- Exploiting various vulnerabilities
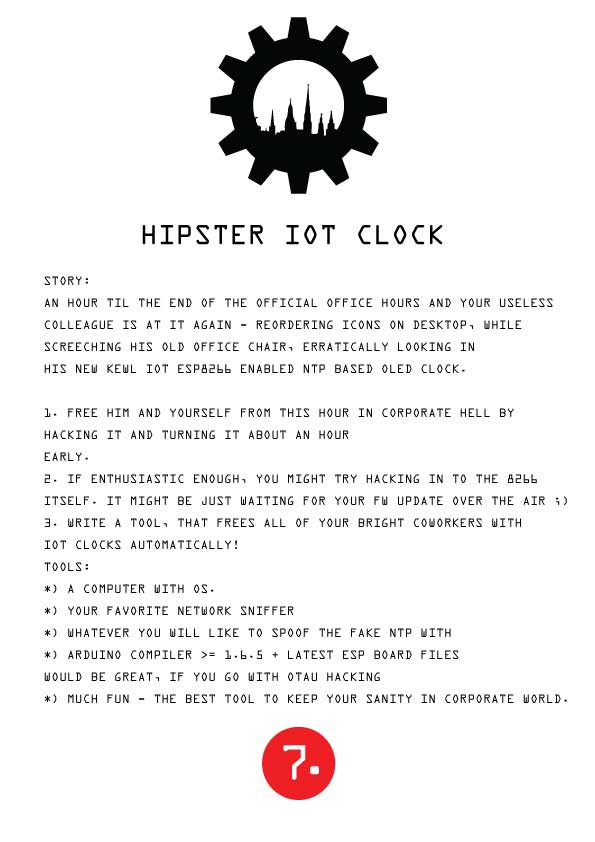
- Cracking wireless networks and spoofing ARP/DNS/NTP/etc.
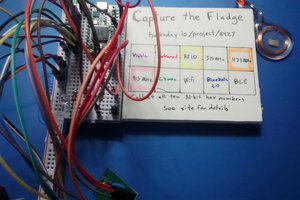
- Intercepting and decoding RF transmissions
- Speed typing on either PC keyboard or typewriter
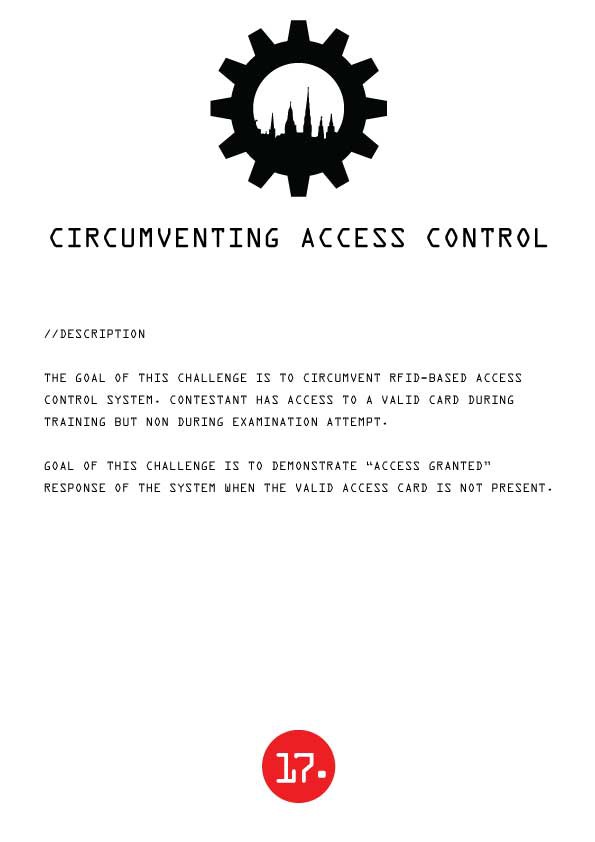
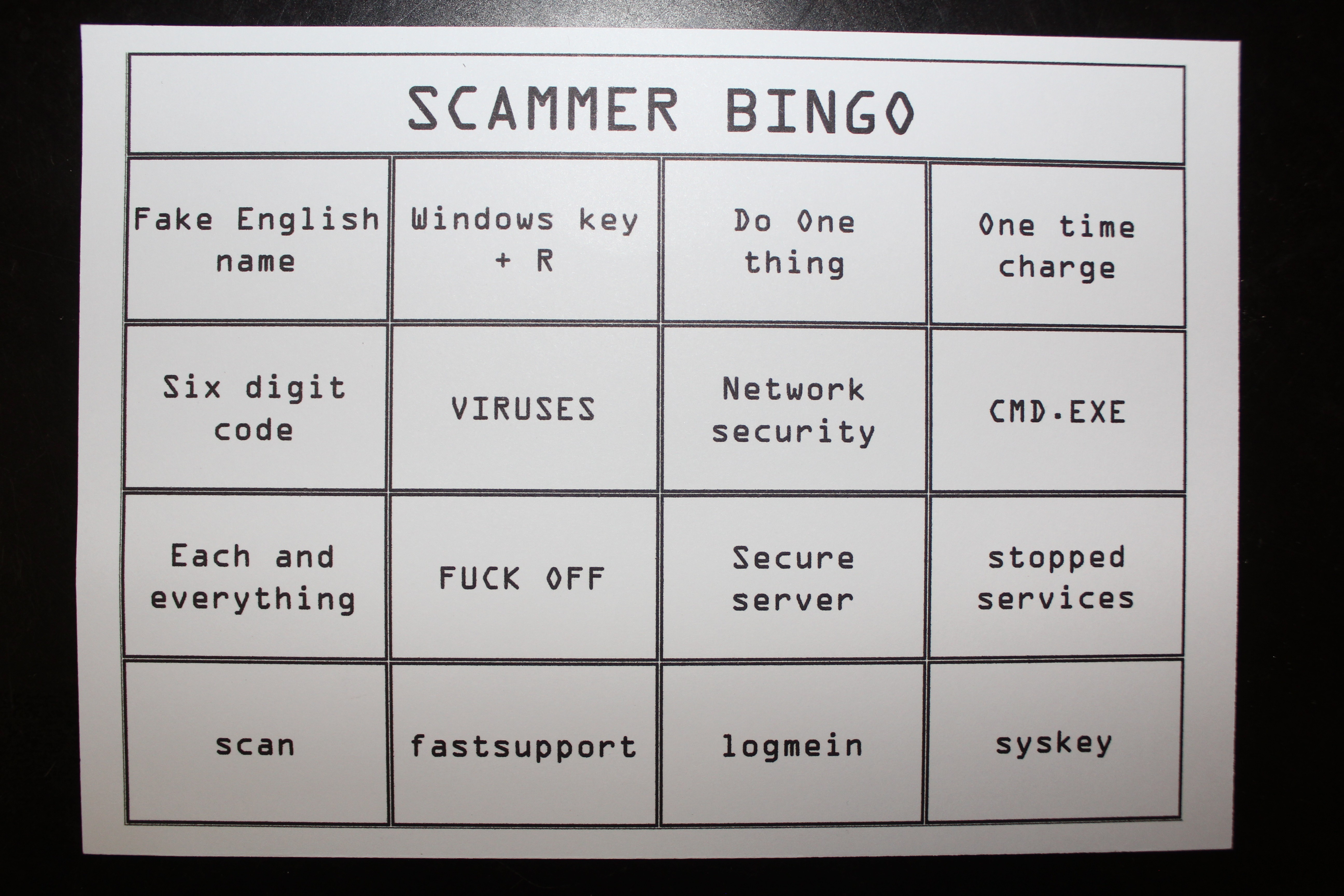
- Social engineering and circumventing tamper-proof tech
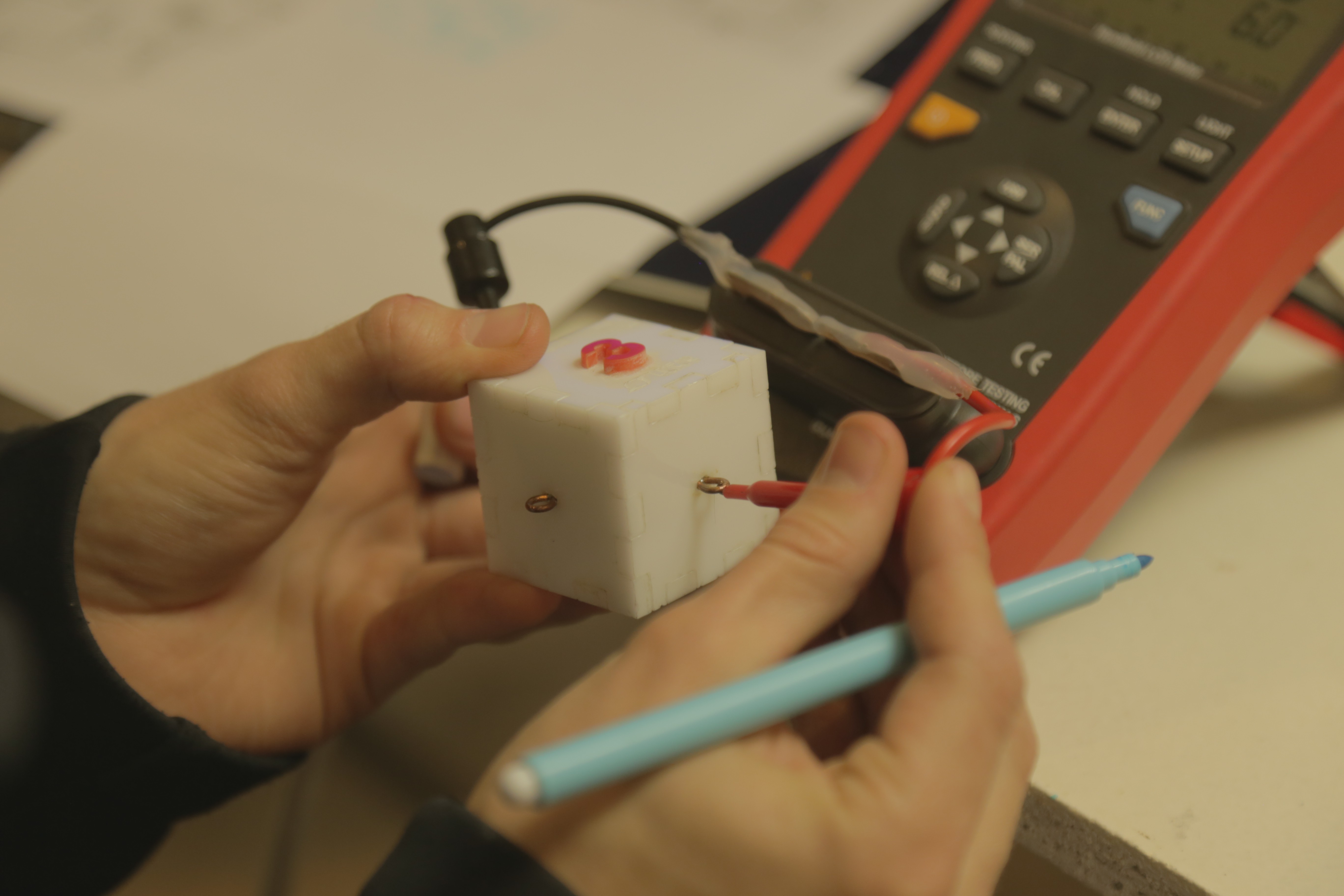
- Circuit reverse-engineering
- Decoding simple ciphers and steganography
Proceed to the work-logs to read more!
 Arya
Arya





 #frustration
#frustration  #success
#success 
 Some young visitors
Some young visitors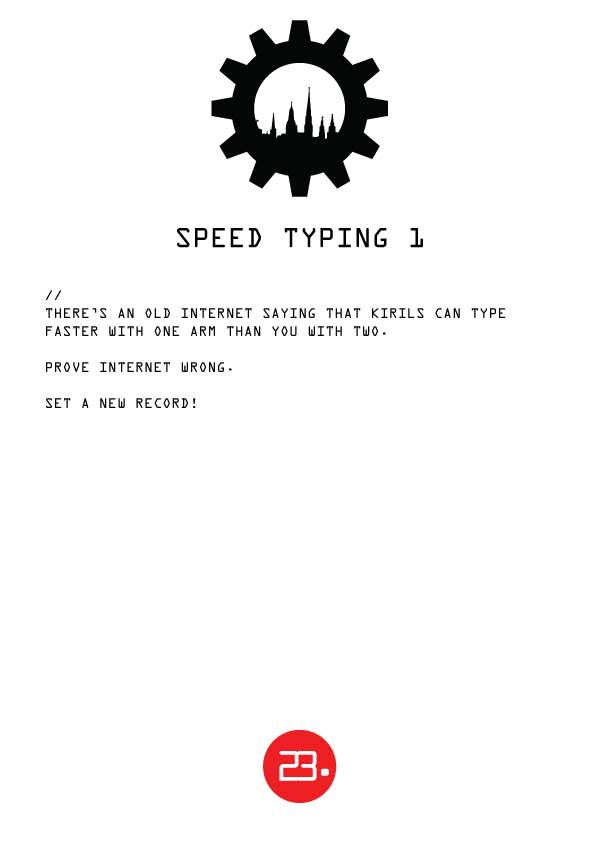
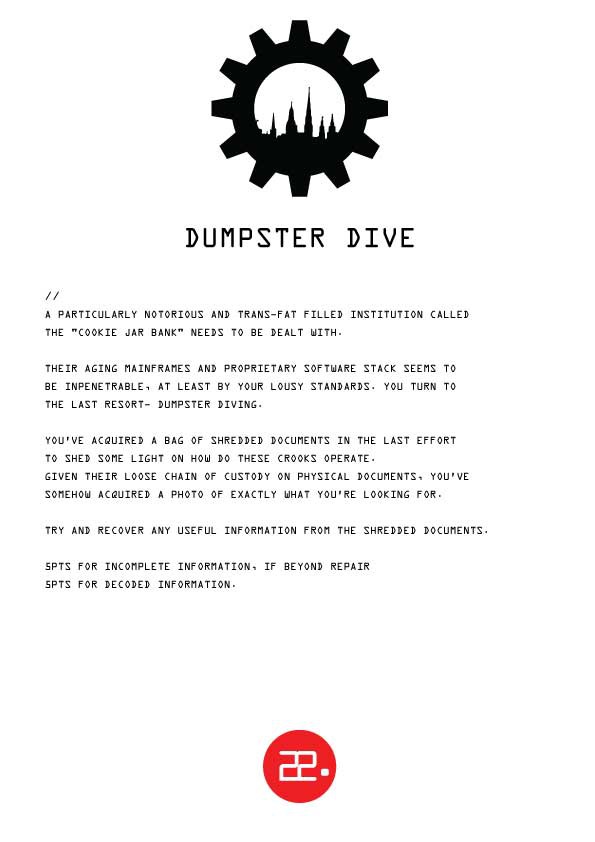
 Pictured: a template of the page we had, one of bags with paper that was supplied to people and two successful attempts at solving this.
Pictured: a template of the page we had, one of bags with paper that was supplied to people and two successful attempts at solving this.
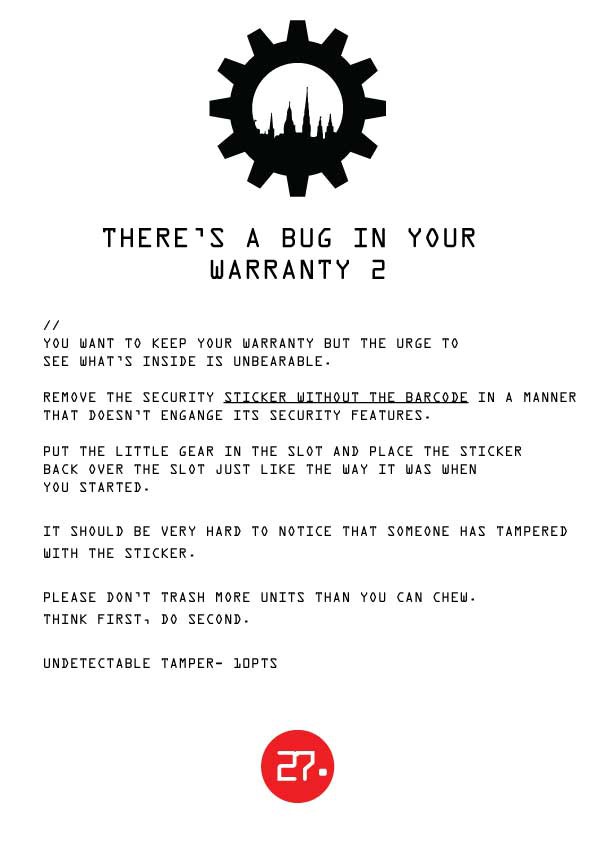
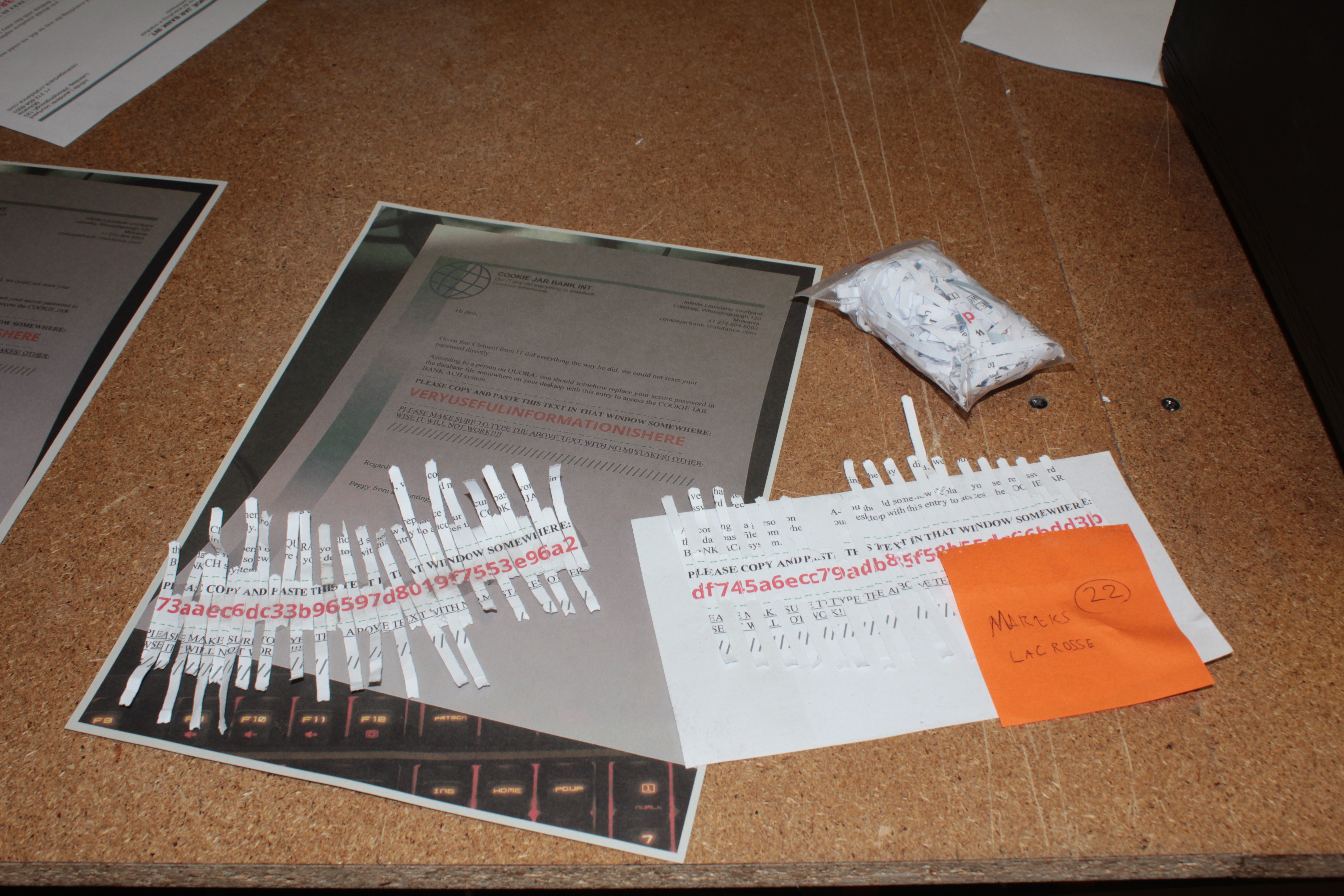
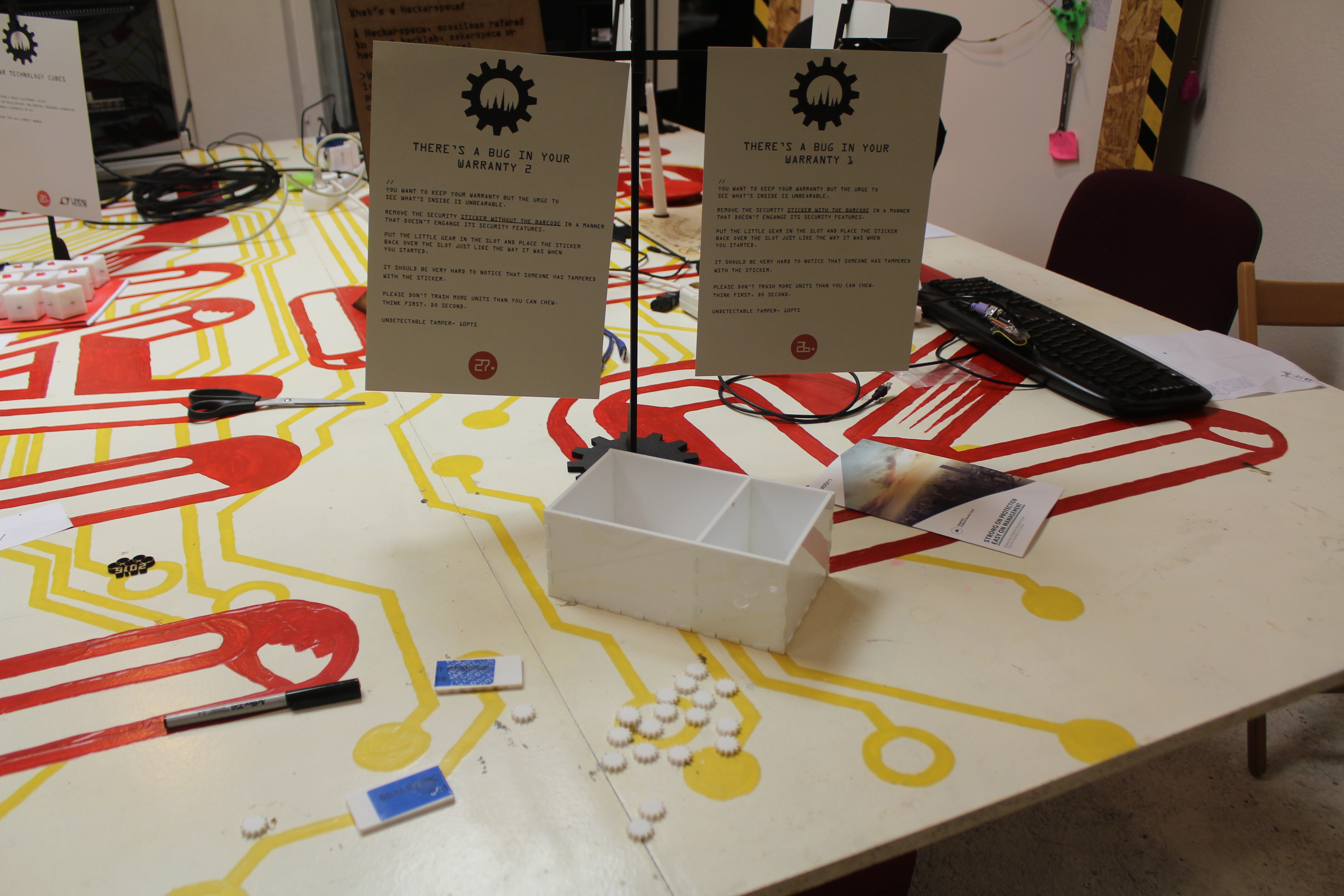 Challenge materials - pieces of plastic with a gear-shaped cutout, an anti-tamper sticker covering the cutout from both sides and gears you need to insert inder the cutout. Those two pieces of plastics show the unsuccessful attempts at ungluing the sticker, as the white marks can be seen.
Challenge materials - pieces of plastic with a gear-shaped cutout, an anti-tamper sticker covering the cutout from both sides and gears you need to insert inder the cutout. Those two pieces of plastics show the unsuccessful attempts at ungluing the sticker, as the white marks can be seen.

 Zapp
Zapp
 Jacob Creedon
Jacob Creedon
 Benchoff
Benchoff