- AES-256 encrypted with optional BZ2 compression.
- Multi-round password hashing to derive key material from passwords.
- No predictable patterns to search for. Offset is derived from the password, and the stride between pixels is arhythmic, with a seed value derived from the password.
- Each color is treated as a discrete channel, with messages able to span channels. This allows up to three independent messages to be overlaid on the same carrier, or one message can occupy multiple channels.
- Option for automatic re-scaling of the carrier image to minimize waste.
- All relevant parameters are derived from the key, or stored as discrete bits, allowing for simple decoding. Just supply a carrier image and a correct password.
- MD5 integrity verification.
- File storage and retrieval
- Built-in trivial logging faculty.
Bury it under the noise floor
Here is discussed a PHP class to hide encrypted messages and files inside of images without significantly changing the way the image looks.
 J. Ian Lindsay
J. Ian Lindsay

 John Boyd
John Boyd
 jimmy.c.alzen
jimmy.c.alzen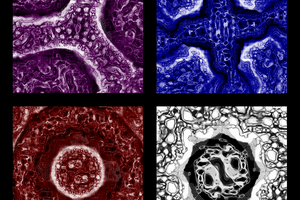
 xD
xD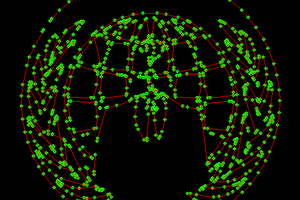
 rawe
rawe
Ha! My test fixture was inoperable since I moved my hosting. It has been fixed.